As per requested by many friends, Following is an short guide on howto configure payment reminder for Expired users in DMASOFTLAB RADIUS MANAGER 4.x.x. I wrote this guide because its better to explain in details with snapshots here, rather then explaining to every individual.
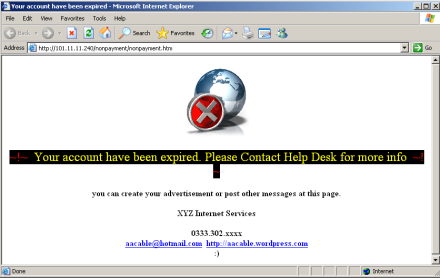
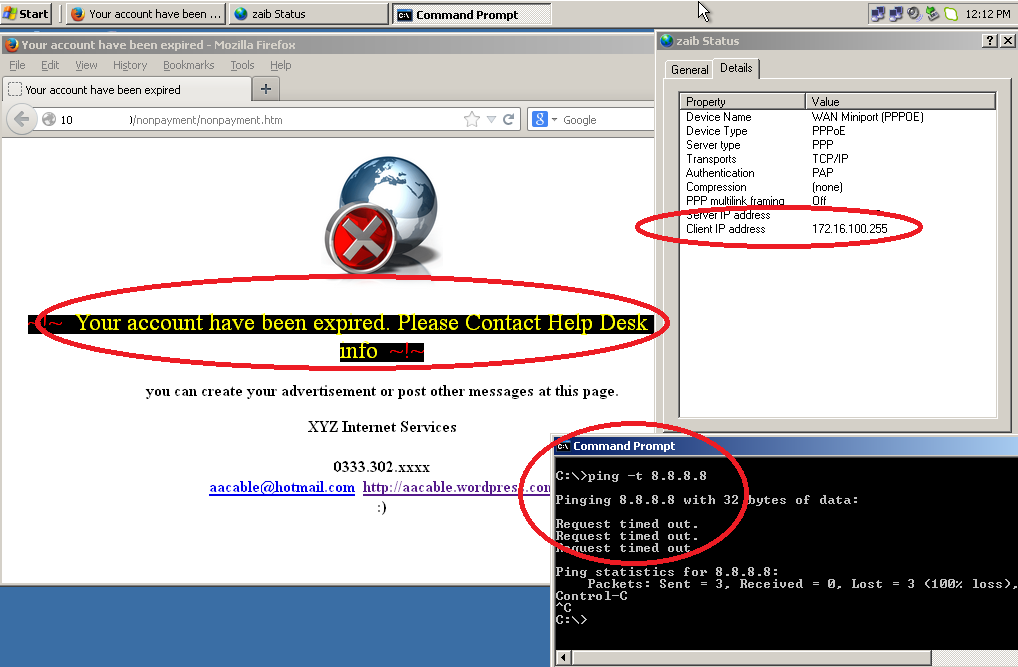
This guide will demonstrate that if the user account is expired, he still can login to your Mikrotik / NAS, but when he will try to browse, he will be redirected to Non Payment page showing why his access is blocked. Please note that only HTTP request will be redirected, HTTPS is not supported. Example if some one tries to open HTTPS://WWW.GOOGLE.COM, he will see default browser error, but if some try to open HTTP://WWW.BBC.COM he will be properly redirected.
Scenario #1 :
[Simple one]
Mikrotik is used as NAS/pppoe server, all clients are connected to it via pppoe dialer/wifi routers.
- LAN IP + Default DHCP Pool for customers = 192.168.1.0/24
- Local Web Server IP which is hosting our web site + reminder page = 192.168.1.10
- PPPoE IP Pool = 172.16.0.0/24
- EXPIRED IP Pool to be created at Mikrotik = 172.16.100.0/24
- WAN IP = 1.1.1.1 [irrelevant]
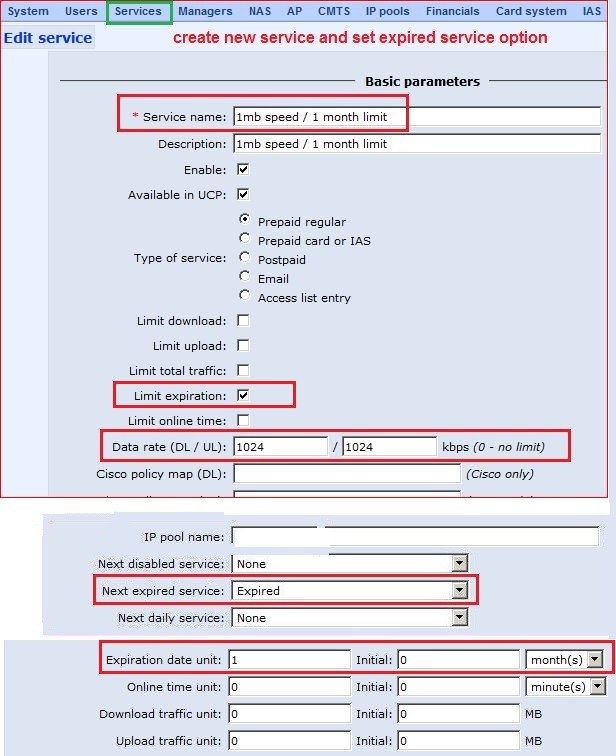
1# RADIUS MANAGER CONFIGURATION
In short, perform following steps …
- Create a new / normal service according to your requirements, like1mb / 1 month limitation
- in Next expired service option, Select EXPIRED as Next Master Service, So when primary service expires, user service will be switched to this one.
[Note: EXPIRED service is already available in RM by default, but if you are unable to find it, then you can create it manually, just add new service with EXPIRED name and set ip pool accordingly, no expiration no speed limit, simple)
As showed in the image below …
Now Create a user in users section and assign it with the new service you just created in above example > 1mb / 1 month limitation
2# MIKROTIK CONFIGURATION
- Add IP POOL for Expired Users
Add new IP Pool for EXPIRED pppoe users, when the user will expire, he will be assigned EXPIRED service, which will use this pool for these users
/ip pool add name=expired ranges=172.16.100.1-172.16.100.255
As showed in the image below …
- Enable WEB PROXY and add rules
Now enable WEB PROXY and add deny/redirect rule so that we can redirect the EXPIRED users pool to any web server showing the non payment reminder page. You can also use EXTERNAL proxy to do the redirection like squid proxy. but in this guide i am showing only the mikrotik level things.
# First Enable Mikrotik Web-Proxy (You can use external proxy server also like SQUID) /ip proxy set always-from-cache=no cache-administrator=webmaster cache-hit-dscp=4 cache-on-disk=no enabled=yes max-cache-size=unlimited max-client-connections=600 max-fresh-time=3d max-server-connections=600 \ parent-proxy=0.0.0.0 parent-proxy-port=0 port=8080 serialize-connections=no src-address=0.0.0.0 # Add rule to allow access to web server, otherwise user wont be able to access the reminder page. this rule must be on top. /ip proxy access add action=allow comment="Allow acess to web server so expired users can view the payment reminder page. it can be locally hosted or external (on internet) as well." disabled=no dst-address=192.168.0.10 \ dst-port="" # Now add rule to redirect expired ip pool users too local or external web server payment reminder page. /ip proxy add action=deny disabled=no dst-port="" redirect-to=192.168.0.10/nonpayment/nonpayment.htm
As showed in the image below …
Add FIREWALL REDIRECT rule in NAT SECTION
Now add REDIRECT rule in FIREWALL/NAT section, and add only pppoe users pool in default NAT rule.
This is to make sure that users with expired users are redirected to web proxy which will be deny there request and redirect to web server reminder page.
and also add pppoe valid users pool in default NAT rule src-address, so that only valid pppoe users can browse the internet.
As showed in the image below …
RESULT
Now when the client primary profile expires, it will switch to NEXT MASTER SERVICE which we configured to EXPIRED, thus he will get ip from EXPIRED pool, and then mikrotik will redirect to proxy which will deny its request and redirect to local payment reminder page.
As showed in the image below …
Additional Tip for those who uses Squid Proxy as well.
SQUID PROXY RULE TO BLOCK EXPIRED POOL RANGE
in squid.conf add these on before other ACL. (or on top)
acl expired-clients src 172.16.100.0/24 http_access deny expired-clients deny_info http://web_server_ip/nonpayment/nonpayment.htm expired-clients
Note: Ideally web server should be on same subnet. Also make sure you allow access to web server it self otherwise page will not be display.
Another Example of code: web server ip address is 192.168.10.2 , and expired pool is 10.0.0.0/24
#first allow access to web server acl allowed_sites dst 192.168.10.2 http_access allow allowed_sites # then block further access for expired users and redirect them to expired clients acl expired-clients src 10.0.0.0/24 http_access deny expired-clients deny_info http://192.168.10.2/nonpayment.htm expired-clients
Another working code example
/ip firewall nat add action=masquerade chain=srcnat comment="ALLOW 8.8.8.8 DNS REQUESTS for EXPIRED USERS...." dst-address=8.8.8.8 src-address-list=expired add action=redirect chain=dstnat comment="Redirect EXPIRED users to web proxy for non payment page redirection" dst-port=80 protocol=tcp src-address-list=expired-pool \ to-ports=50009 add action=masquerade chain=srcnat dst-address=192.168.100.1 src-address-list=expired-pool /ip firewall filter add action=accept chain=input comment="ALLOW DNS PORT FOR EXPIRED USERS" dst-port=53 protocol=udp src-address-list=expired-pool add action=accept chain=input comment="ALLOW WEB PROXY PORT FOR EXPIRED USERS" dst-port=50009 protocol=tcp src-address-list=expired-pool add action=accept chain=forward dst-address=8.8.8.8 src-address-list=expired-pool add action=accept chain=forward dst-address=192.168.100.1 src-address-list=expired-pool add action=accept chain=input dst-address=192.168.100.1 src-address-list=expired-pool add action=drop chain=forward comment="BLOCK EXPIRED USERS" src-address-list=expired-pool /ip firewall mangle add action=accept chain=prerouting comment="allow expired users for routing to radius account expired page" src-address-list=expired-pool /ip proxy set cache-administrator="Syed Jahanzaib - aacable@hotmail.com" enabled=yes max-cache-object-size=1KiB max-cache-size=none port=50009 /ip proxy access add dst-address=192.168.100.1 src-address=192.168.255.1-192.168.255.255 add action=deny redirect-to=192.168.100.1/expired.html
Regard’s
Syed Jahanzaib



thanx for evry thing K but if you can help me about how to configure that in proxy squid
LikeLike
Comment by Mohamed Shamallakh — June 4, 2014 @ 1:34 PM
simply redirect the expired pool to squid proxy, and in squid proxy, create an ACL for this range and deny it, and in deny_info redirect it to local web page.
BTW, article updated for squid reference too.
SQUID PROXY RULE TO BLOCK EXPIRED POOL RANGE
in squid.conf add these on before other ACL. (or on top)
Note: Ideally web server should be on same subne
LikeLike
Comment by Syed Jahanzaib / Pinochio~:) — June 4, 2014 @ 2:31 PM
thanx : can i write arabic language in web
LikeLike
Comment by Mohamed Shamallakh — June 5, 2014 @ 4:43 PM
http_access deny unpaid
deny_info http://10.10.20.6/priv/ unpaid
10.10.20.6 is ip web server but dose not work
page in clinet appear like 10.10.20.6/priv/ in url explore
please can u help me
LikeLike
Comment by Mohamed Shamallakh — June 5, 2014 @ 5:20 PM
Hi,
I have been following your blog for a long time now!
I have been waiting for this solution with Radius Manager.
Unfortunately I could not pull it off with the above example. It seems strange that the NEW SERVICE should have ip pool “expired”!
Isn’t the idea to get into EXPIRED pool only after the service actually expires and changes to Expired (where you have the expired pool fixed already!)?
Is it a mistake or am I way off the logic followed?
Don’t we need few firewall rules as well?
Your comment will be appreciated!
LikeLike
Comment by Vasko Neyov — June 28, 2014 @ 6:01 PM
I agree with you , the first service need to have a non-expired ip pool , also i don’t have a “Next Expired Service” in my panel , i have ” Next Maser Service” instead of it , so when i choose it and after the first service expired , the user still expired and didn’t changed to the new “expire” service ! ?
LikeLike
Comment by OM — August 5, 2014 @ 11:39 PM
salam alaykum Syed Jahanzaib. I’m also trying to redirect expired users to a expired service page. the problem is that my expired clients don’t get an ip from expired pool, which I have created in mikrotik and declared in radius manager. the mikrotik logs shows ‘authentication failed’ for expired clients. I have dma radius manager v4.0.4. can you help me about this please?
LikeLike
Comment by sober81 — February 5, 2015 @ 4:25 PM
better to upgrade with ver 4.1.6 to avoid un expected errors
however I have tested long time ago, the redirection do work properly in that version too. maybe you are skipping any step.
first create an ip pool in the mikrotik with exact NAME which is defined in the RM service section.
LikeLike
Comment by Syed Jahanzaib / Pinochio~:) — February 9, 2015 @ 3:35 PM
Anyone working this method with V 6.15 ? this is not working even for PPPoE or Hotspot? DNS look up creates the problem, i think the DNS must be accepted in FW, It would be nice if some one shares the working method
LikeLike
Comment by anupam das — September 29, 2014 @ 5:42 PM
by default, dns access is allowed in general cases. and for nat, we have allowed only local pppoe / hotspot series. if you are having trouble it making work, we can help.
LikeLike
Comment by Syed Jahanzaib / Pinochio~:) — September 30, 2014 @ 10:10 AM
this method has a bug, it works only with http, sites without SSL is redirected to proxy and hence reminder page, but if a user after Login with expired ip pool, he can browse internet if the site is https . it kills data , any solution?
LikeLike
Comment by Anupam das — April 28, 2015 @ 4:56 PM
No proper solution for it yet EXCEPT to buy PAID SSL certificate from good repo company. So usually its not feasible for smaller networks.
LikeLike
Comment by Syed Jahanzaib / Pinochio~:) — May 8, 2015 @ 4:44 PM
please help, have tried this mehtod too ..http://wiki.mikrotik.com/wiki/Payment_Reminders
LikeLike
Comment by anupam das — September 30, 2014 @ 12:53 PM
dear syed jee, waiting for your kind help and knowledge ..
LikeLike
Comment by anupam das — October 1, 2014 @ 6:24 PM
yes…. this method is not working. tried for pppoe first , shows error, the second way for hotspot is the same … we are using the latest release of MT V 6.19 ,, the author may have the clues , we would be grateful to him if he can show us the correct working method. thanks
LikeLike
Comment by htal ukkady — October 2, 2014 @ 6:29 PM
this method works fine. maybe somethign you are not doing right, we can do a remote session to see the problem.
LikeLike
Comment by Syed Jahanzaib / Pinochio~:) — October 3, 2014 @ 8:33 AM
i am ready , please tell me how to proceed? team viewer ?
LikeLike
Comment by anupam das — October 3, 2014 @ 9:32 AM
Thanks for your help, the expired IPs given to non payment customers should comes from the same IP pool where the hotspot gateway resides , used starting few ips for the non payment expired pool within the allowed ips, this only makes the method working perfectly, for the starting IPs a address list can be created in /ip firewall add list for easy NAT and forwarding, Thanks Syed
LikeLike
Comment by anupam das — October 3, 2014 @ 1:42 PM
Dear Bro..
whats change we can do in this for DHCP SERVER Radius Login By Mac Auth
LikeLike
Comment by Deep Patel — February 25, 2015 @ 4:23 PM
hi the above method works, however the redirect doesn’t work for https:// website. How do i go about the same thanks?
LikeLike
Comment by Ians — October 10, 2015 @ 7:27 PM
is there anyway to block HTTPS traffic
LikeLike
Comment by Rashed — November 10, 2017 @ 10:02 PM
My nas system is ocserv, is there a way to achieve this effect, I read all the tutorials about radius manager, and I think your tutorials are great
LikeLike
Comment by kailsay — June 4, 2023 @ 12:14 PM