~Mikrotik Router / 4 WAN Load Balancing using PCC method~
Updated 4th December, 2013
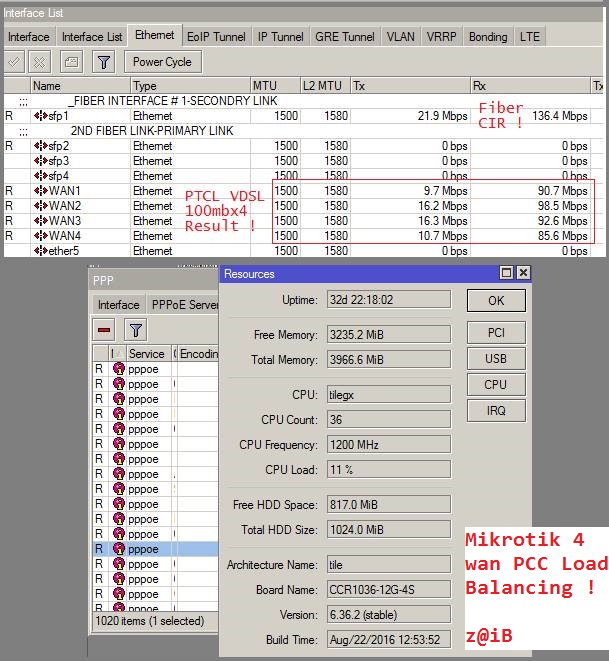
This post illustrates on how you can configure load balancing of multiple wan links using Mikrotik Routerboard hardware (or RouterOS x86 version). In this example I have used Mikrotik Routerboard CCR 1036 model. 4 ports are connected with Four DSL Routers, and 5th port was connected with User LAN. Don’t forget to rename the interface names accordingly if you are a copy paste fan.
In this example, we are using PCC (per connection classifier) method to achieve the load balancing. There are few options using this approach & each option may give you different results.
Example#1: src-address
Use src-address as classifier, this way you will get rid of problems like https/broken link, streaming issues etc (dueot ip changing on each request) . Load balancing using this PCC technique (src-address) requires that users must be hitting the PCC box directly (either dhcp/ppp server etc). In this method user will be tagged with specific WAN link once connected with the mikrotik. This way till his online session he will stick to that particular wan link. A single user will not be ale to use all WAN links. This approach works good if you have a bit higher amount of bandwidth on each link.
Example#2: both-addresses-and-ports
If somehow you are not satisfied with the src-address approach (OR your requirements is to achieve maximum download speed using all WAN links simultaneously) , Then play with the PCC Classifier, Try both addresses and ports as the classifier (as used in this guide as well). While this will randomize things the most and in theory give you the most fair allocation of bandwidth (as any request will be distributed among all WAN links), BUT there is also a good chance that it will break certain things like banking web sites and some forums. This is because often times a HTTP requests will generate several connections, so there is a chance that some requests may go out a different route than the initial one, and that will break secure web sites. For that reason I usually like to go with src-address PCC load balancing approach (but only if users are hitting the pcc box)
~Syed Jahanzaib
Scenario:
- Mikrotik LAN IP = 192.168.0.1
- DSL1 Router IP = 192.168.1.1 / INTERFACE NAME = WAN1
- DSL2 Router IP = 192.168.1.1 / INTERFACE NAME = WAN2
- DSL3 Router IP = 192.168.1.1 / INTERFACE NAME = WAN3
- DSL4 Router IP = 192.168.1.1 / INTERFACE NAME = WAN4
the Script !
# IP Addresses for reference purpose /ip address add address=192.168.0.1/24 network=192.168.0.0 broadcast=192.168.0.255 interface=Local add address=192.168.1.2/24 network=192.168.1.0 broadcast=192.168.1.255 interface=WAN1 add address=192.168.2.2/24 network=192.168.2.0 broadcast=192.168.2.255 interface=WAN2 add address=192.168.3.2/24 network=192.168.3.0 broadcast=192.168.3.255 interface=WAN3 add address=192.168.4.2/24 network=192.168.4.0 broadcast=192.168.4.255 interface=WAN4 # Add NET ALLOWED users Address list, to make sure only allowed users get internet access. Make sure to modify this as per your requirements, we can use this list later for other management purposes /ip firewall address-list add address=192.168.0.1-192.168.0.255 list=allowed_users # Accept Connections /ip firewall mangle add action=accept chain=prerouting in-interface=WAN1 add action=accept chain=prerouting in-interface=WAN2 add action=accept chain=prerouting in-interface=WAN3 add action=accept chain=prerouting in-interface=WAN4 # Mangle Section # Marking connections for 4 dsl distribution add chain=prerouting dst-address-type=!local in-interface=Local per-connection-classifier=both-addresses-and-ports:4/0 action=mark-connection new-connection-mark=WAN1_conn passthrough=yes src-address-list=allowed_users add chain=prerouting dst-address-type=!local in-interface=Local per-connection-classifier=both-addresses-and-ports:4/1 action=mark-connection new-connection-mark=WAN2_conn passthrough=yes src-address-list=allowed_users add chain=prerouting dst-address-type=!local in-interface=Local per-connection-classifier=both-addresses-and-ports:4/2 action=mark-connection new-connection-mark=WAN3_conn passthrough=yes src-address-list=allowed_users add chain=prerouting dst-address-type=!local in-interface=Local per-connection-classifier=both-addresses-and-ports:4/3 action=mark-connection new-connection-mark=WAN4_conn passthrough=yes src-address-list=allowed_users # Marking Routing Marks to be used by ROUTES Section add chain=prerouting connection-mark=WAN1_conn in-interface=Local action=mark-routing new-routing-mark=to_WAN1 add chain=prerouting connection-mark=WAN2_conn in-interface=Local action=mark-routing new-routing-mark=to_WAN2 add chain=prerouting connection-mark=WAN3_conn in-interface=Local action=mark-routing new-routing-mark=to_WAN3 add chain=prerouting connection-mark=WAN4_conn in-interface=Local action=mark-routing new-routing-mark=to_WAN4 # Adding ROUTE for marked routes (done by mangle earlier) /ip route add dst-address=0.0.0.0/0 gateway=192.168.1.1 routing-mark=to_WAN1 check-gateway=ping add dst-address=0.0.0.0/0 gateway=192.168.2.1 routing-mark=to_WAN2 check-gateway=ping add dst-address=0.0.0.0/0 gateway=192.168.3.1 routing-mark=to_WAN3 check-gateway=ping add dst-address=0.0.0.0/0 gateway=192.168.4.1 routing-mark=to_WAN4 check-gateway=ping # DEFAULT ROUTES, OR Fail over routes , just incase in any router goes offline, then these default routes as per distance, will be used as default add dst-address=0.0.0.0/0 gateway=192.168.1.1 distance=1 check-gateway=ping add dst-address=0.0.0.0/0 gateway=192.168.2.1 distance=2 check-gateway=ping add dst-address=0.0.0.0/0 gateway=192.168.3.1 distance=3 check-gateway=ping add dst-address=0.0.0.0/0 gateway=192.168.4.1 distance=4 check-gateway=ping # NAT/MASQUERADE the requests going on each interface (used by ROUTES) /ip firewall nat add chain=srcnat out-interface=WAN1 action=masquerade src-address-list=allowed_users add chain=srcnat out-interface=WAN2 action=masquerade src-address-list=allowed_users add chain=srcnat out-interface=WAN3 action=masquerade src-address-list=allowed_users add chain=srcnat out-interface=WAN4 action=masquerade src-address-list=allowed_users
Now Configure DNS server so users can resolve host names using your mikrotik.
/ip dns set allow-remote-requests=yes cache-max-ttl=1w cache-size=5000KiB max-udp-packet-size=512 servers=8.8.8.8
All Done !
Now Test the link by putting user load, the more multiple users load you put on it, the better Load Balance result you will get 🙂
PCC WITH UN-EQUAL WAN LINKS
If you have Un-Equal WAN Links, for example WAN,1,2,3 are of 4MB and WAN,4 is of 8 Mb, and you want to force MT to use WAN4 link more then other because of its capacity, Then you have to Add more PCC rules assigning the same two marks to a specific link i.e WAN4 , something like
Code:
add chain=prerouting dst-address-type=!local in-interface=Local per-connection-classifier=both-addresses-and-ports:4/0 action=mark-connection new-connection-mark=WAN1_conn passthrough=yes add chain=prerouting dst-address-type=!local in-interface=Local per-connection-classifier=both-addresses-and-ports:4/1 action=mark-connection new-connection-mark=WAN2_conn passthrough=yes add chain=prerouting dst-address-type=!local in-interface=Local per-connection-classifier=both-addresses-and-ports:4/2 action=mark-connection new-connection-mark=WAN3_conn passthrough=yes add chain=prerouting dst-address-type=!local in-interface=Local per-connection-classifier=both-addresses-and-ports:4/3 action=mark-connection new-connection-mark=WAN4_conn passthrough=yes add chain=prerouting dst-address-type=!local in-interface=Local per-connection-classifier=both-addresses-and-ports:4/4 action=mark-connection new-connection-mark=WAN4_conn passthrough=yes
PCC WITH SAME GATEWAY
Try defining the outbound interface.
For example replace this.
/ip route add dst-address=0.0.0.0/0 gateway=1.2.3.4 routing-mark=to_wan-ISP1 check-gateway=ping add dst-address=0.0.0.0/0 gateway=1.2.3.4 routing-mark=to_wan-ISP2 check-gateway=ping With following /ip route add dst-address=0.0.0.0/0 gateway=1.2.3.4%eth1-ISP routing-mark=to_wan-ISP1 check-gateway=ping add dst-address=0.0.0.0/0 gateway=1.2.3.4%eth2-ISP routing-mark=to_wan-ISP2 check-gateway=ping
Replace the eth1-ISP with your own wan interface name , use the notation % for sure.
If it works , let me know
TIP:
Using modems in BRIDGE mode will probably give you some better performance and control 🙂 Try it 😉
22 WAN PCC script , using TPLINK routers as wan gateways
Just for reference purposes,
# IP addresses for WAN Modems (TPLINK Routers) #192.168.1.1 #192.168.2.1 #and so on /ip address add address=172.16.0.1/16 interface=Local network=172.16.0.0 add address=192.168.1.50/24 interface=vlan1 network=192.168.1.0 add address=192.168.2.50/24 interface=vlan2 network=192.168.2.0 add address=192.168.3.50/24 interface=vlan3 network=192.168.3.0 add address=192.168.4.50/24 interface=vlan4 network=192.168.4.0 add address=192.168.5.50/24 interface=vlan5 network=192.168.5.0 add address=192.168.6.50/24 interface=vlan6 network=192.168.6.0 add address=192.168.7.50/24 interface=vlan7 network=192.168.7.0 add address=192.168.8.50/24 interface=vlan8 network=192.168.8.0 add address=192.168.9.25/24 interface=vlan9 network=192.168.9.0 add address=192.168.10.50/24 interface=vlan10 network=192.168.10.0 add address=192.168.11.50/24 interface=vlan11 network=192.168.11.0 add address=192.168.12.50/24 interface=vlan12 network=192.168.12.0 add address=192.168.13.50/24 interface=vlan13 network=192.168.13.0 add address=192.168.14.50/24 interface=vlan14 network=192.168.14.0 add address=192.168.15.50/24 interface=vlan15 network=192.168.15.0 add address=192.168.16.50/24 interface=vlan16 network=192.168.16.0 add address=192.168.17.50/24 interface=vlan17 network=192.168.17.0 add address=192.168.18.50/24 interface=vlan18 network=192.168.18.0 add address=192.168.19.50/24 interface=vlan19 network=192.168.19.0 add address=192.168.20.50/24 interface=vlan20 network=192.168.20.0 add address=192.168.21.50/24 interface=vlan21 network=192.168.21.0 add address=192.168.22.50/24 interface=vlan22 network=192.168.22.0 /interface vlan add comment=WAN-1 interface=WAN_TRUNK name=vlan1 vlan-id=2 add comment=WAN-2 interface=WAN_TRUNK name=vlan2 vlan-id=3 add comment=WAN-3 interface=WAN_TRUNK name=vlan3 vlan-id=4 add comment=WAN-4 interface=WAN_TRUNK name=vlan4 vlan-id=5 add comment=WAN-5 interface=WAN_TRUNK name=vlan5 vlan-id=6 add comment=WAN-6 interface=WAN_TRUNK name=vlan6 vlan-id=7 add comment=WAN-7 interface=WAN_TRUNK name=vlan7 vlan-id=8 add comment=WAN-8 interface=WAN_TRUNK name=vlan8 vlan-id=9 add comment=WAN-9 interface=WAN_TRUNK name=vlan9 vlan-id=10 add comment=WAN-10 interface=WAN_TRUNK name=vlan10 vlan-id=11 add comment=WAN-11 interface=WAN_TRUNK name=vlan11 vlan-id=12 add comment=WAN-12 interface=WAN_TRUNK name=vlan12 vlan-id=13 add comment=WAN-13 interface=WAN_TRUNK name=vlan13 vlan-id=14 add comment=WAN-14 interface=WAN_TRUNK name=vlan14 vlan-id=15 add comment=WAN-15 interface=WAN_TRUNK name=vlan15 vlan-id=16 add comment=WAN-16 interface=WAN_TRUNK name=vlan16 vlan-id=17 add comment=WAN-17 interface=WAN_TRUNK name=vlan17 vlan-id=18 add comment=WAN-18 interface=WAN_TRUNK name=vlan18 vlan-id=19 add comment=WAN-19 interface=WAN_TRUNK name=vlan19 vlan-id=20 add comment=WAN-20 interface=WAN_TRUNK name=vlan20 vlan-id=21 add comment=WAN-20 interface=WAN_TRUNK name=vlan21 vlan-id=22 add comment=WAN-21 interface=WAN_TRUNK name=vlan22 vlan-id=23 /ip firewall address-list add address=10.0.0.1-10.0.0.255 list=net_allowed_list /ip firewall mangle add action=accept chain=prerouting dst-address=192.168.1.0/24 add action=accept chain=prerouting dst-address=192.168.2.0/24 add action=accept chain=prerouting dst-address=192.168.3.0/24 add action=accept chain=prerouting dst-address=192.168.4.0/24 add action=accept chain=prerouting dst-address=192.168.5.0/24 add action=accept chain=prerouting dst-address=192.168.6.0/24 add action=accept chain=prerouting dst-address=192.168.7.0/24 add action=accept chain=prerouting dst-address=192.168.8.0/24 add action=accept chain=prerouting dst-address=192.168.9.0/24 add action=accept chain=prerouting dst-address=192.168.10.0/24 add action=accept chain=prerouting dst-address=192.168.11.0/24 add action=accept chain=prerouting dst-address=192.168.12.0/24 add action=accept chain=prerouting dst-address=192.168.13.0/24 add action=accept chain=prerouting dst-address=192.168.14.0/24 add action=accept chain=prerouting dst-address=192.168.15.0/24 add action=accept chain=prerouting dst-address=192.168.16.0/24 add action=accept chain=prerouting dst-address=192.168.17.0/24 add action=accept chain=prerouting dst-address=192.168.18.0/24 add action=accept chain=prerouting dst-address=192.168.19.0/24 add action=accept chain=prerouting dst-address=192.168.20.0/24 add action=accept chain=prerouting dst-address=192.168.21.0/24 add action=accept chain=prerouting dst-address=192.168.22.0/24 add action=mark-connection chain=prerouting comment=2 dst-address-type=!local new-connection-mark=WAN1_conn passthrough=yes per-connection-classifier=both-addresses-and-ports:22/0 src-address-list=net_allowed_list add action=mark-connection chain=prerouting dst-address-type=!local new-connection-mark=WAN2_conn passthrough=yes per-connection-classifier=both-addresses-and-ports:22/1 src-address-list=net_allowed_list add action=mark-connection chain=prerouting dst-address-type=!local new-connection-mark=WAN3_conn passthrough=yes per-connection-classifier=both-addresses-and-ports:22/2 src-address-list=net_allowed_list add action=mark-connection chain=prerouting dst-address-type=!local new-connection-mark=WAN4_conn passthrough=yes per-connection-classifier=both-addresses-and-ports:22/3 src-address-list=net_allowed_list add action=mark-connection chain=prerouting dst-address-type=!local new-connection-mark=WAN5_conn passthrough=yes per-connection-classifier=both-addresses-and-ports:22/4 src-address-list=net_allowed_list add action=mark-connection chain=prerouting dst-address-type=!local new-connection-mark=WAN6_conn passthrough=yes per-connection-classifier=both-addresses-and-ports:22/5 src-address-list=net_allowed_list add action=mark-connection chain=prerouting dst-address-type=!local new-connection-mark=WAN7_conn passthrough=yes per-connection-classifier=both-addresses-and-ports:22/6 src-address-list=net_allowed_list add action=mark-connection chain=prerouting dst-address-type=!local new-connection-mark=WAN8_conn passthrough=yes per-connection-classifier=both-addresses-and-ports:22/7 src-address-list=net_allowed_list add action=mark-connection chain=prerouting dst-address-type=!local new-connection-mark=WAN9_conn passthrough=yes per-connection-classifier=both-addresses-and-ports:22/8 src-address-list=net_allowed_list add action=mark-connection chain=prerouting dst-address-type=!local new-connection-mark=WAN10_conn passthrough=yes per-connection-classifier=both-addresses-and-ports:22/9 src-address-list=net_allowed_list add action=mark-connection chain=prerouting dst-address-type=!local new-connection-mark=WAN11_conn passthrough=yes per-connection-classifier=both-addresses-and-ports:22/10 src-address-list=net_allowed_list add action=mark-connection chain=prerouting dst-address-type=!local new-connection-mark=WAN12_Conn passthrough=yes per-connection-classifier=both-addresses-and-ports:22/11 src-address-list=net_allowed_list add action=mark-connection chain=prerouting dst-address-type=!local new-connection-mark=WAN13_Conn passthrough=yes per-connection-classifier=both-addresses-and-ports:22/12 src-address-list=net_allowed_list add action=mark-connection chain=prerouting dst-address-type=!local new-connection-mark=WAN14_Conn passthrough=yes per-connection-classifier=both-addresses-and-ports:22/13 src-address-list=net_allowed_list add action=mark-connection chain=prerouting dst-address-type=!local new-connection-mark=WAN15_conn passthrough=yes per-connection-classifier=both-addresses-and-ports:22/14 src-address-list=net_allowed_list add action=mark-connection chain=prerouting dst-address-type=!local new-connection-mark=WAN16_conn passthrough=yes per-connection-classifier=both-addresses-and-ports:22/15 src-address-list=net_allowed_list add action=mark-connection chain=prerouting dst-address-type=!local new-connection-mark=WAN17_conn passthrough=yes per-connection-classifier=both-addresses-and-ports:22/16 src-address-list=net_allowed_list add action=mark-connection chain=prerouting dst-address-type=!local new-connection-mark=WAN18_conn passthrough=yes per-connection-classifier=both-addresses-and-ports:22/17 src-address-list=net_allowed_list add action=mark-connection chain=prerouting dst-address-type=!local new-connection-mark=WAN19_conn passthrough=yes per-connection-classifier=both-addresses-and-ports:22/18 src-address-list=net_allowed_list add action=mark-connection chain=prerouting dst-address-type=!local new-connection-mark=WAN20_conn passthrough=yes per-connection-classifier=both-addresses-and-ports:22/19 src-address-list=net_allowed_list add action=mark-connection chain=prerouting dst-address-type=!local new-connection-mark=WAN21_conn passthrough=yes per-connection-classifier=both-addresses-and-ports:22/20 src-address-list=net_allowed_list add action=mark-connection chain=prerouting dst-address-type=!local new-connection-mark=WAN22_con passthrough=yes per-connection-classifier=both-addresses-and-ports:22/21 src-address-list=net_allowed_list add action=mark-routing chain=prerouting connection-mark=WAN1_conn new-routing-mark=to_WAN1 passthrough=yes add action=mark-routing chain=prerouting connection-mark=WAN2_conn new-routing-mark=to_WAN2 passthrough=yes add action=mark-routing chain=prerouting connection-mark=WAN3_conn new-routing-mark=to_WAN3 passthrough=yes add action=mark-routing chain=prerouting connection-mark=WAN4_conn new-routing-mark=to_WAN4 passthrough=yes add action=mark-routing chain=prerouting connection-mark=WAN5_conn new-routing-mark=to_WAN5 passthrough=yes add action=mark-routing chain=prerouting connection-mark=WAN6_conn new-routing-mark=to_WAN6 passthrough=yes add action=mark-routing chain=prerouting connection-mark=WAN7_conn new-routing-mark=to_WAN7 passthrough=yes add action=mark-routing chain=prerouting connection-mark=WAN8_conn new-routing-mark=to_WAN8 passthrough=yes add action=mark-routing chain=prerouting connection-mark=WAN9_conn new-routing-mark=to_WAN9 passthrough=yes add action=mark-routing chain=prerouting connection-mark=WAN10_conn new-routing-mark=to_WAN10 passthrough=yes add action=mark-routing chain=prerouting connection-mark=WAN11_conn new-routing-mark=to_WAN11 passthrough=yes add action=mark-routing chain=prerouting connection-mark=WAN12_Conn new-routing-mark=to_WAN12 passthrough=yes add action=mark-routing chain=prerouting connection-mark=WAN13_Conn new-routing-mark=to_WAN13 passthrough=yes add action=mark-routing chain=prerouting connection-mark=WAN14_Conn new-routing-mark=to_WAN14 passthrough=yes add action=mark-routing chain=prerouting connection-mark=WAN15_conn new-routing-mark=to_WAN15 passthrough=yes add action=mark-routing chain=prerouting connection-mark=WAN16_conn new-routing-mark=to_WAN16 passthrough=yes add action=mark-routing chain=prerouting connection-mark=WAN17_conn new-routing-mark=to_WAN17 passthrough=yes add action=mark-routing chain=prerouting connection-mark=WAN18_conn new-routing-mark=to_WAN18 passthrough=yes add action=mark-routing chain=prerouting connection-mark=WAN19_conn new-routing-mark=to_WAN19 passthrough=yes add action=mark-routing chain=prerouting connection-mark=WAN20_conn new-routing-mark=to_WAN20 passthrough=yes add action=mark-routing chain=prerouting connection-mark=WAN21_conn new-routing-mark=to_WAN21 passthrough=yes add action=mark-routing chain=prerouting connection-mark=WAN22_con new-routing-mark=to_WAN22 passthrough=yes /ip firewall nat add action=masquerade chain=srcnat src-address-list=net_allowed_list /ip route add check-gateway=ping distance=1 gateway=192.168.1.1 routing-mark=to_WAN1 add check-gateway=ping distance=1 gateway=192.168.2.1 routing-mark=to_WAN2 add check-gateway=ping distance=1 gateway=192.168.3.1 routing-mark=to_WAN3 add check-gateway=ping distance=1 gateway=192.168.4.1 routing-mark=to_WAN4 add check-gateway=ping distance=1 gateway=192.168.5.1 routing-mark=to_WAN5 add check-gateway=ping distance=1 gateway=192.168.6.1 routing-mark=to_WAN6 add check-gateway=ping distance=1 gateway=192.168.7.1 routing-mark=to_WAN7 add check-gateway=ping distance=1 gateway=192.168.8.1 routing-mark=to_WAN8 add check-gateway=ping distance=1 gateway=192.168.9.1 routing-mark=to_WAN9 add check-gateway=ping distance=1 gateway=192.168.10.1 routing-mark=to_WAN10 add check-gateway=ping distance=1 gateway=192.168.11.1 routing-mark=to_WAN11 add check-gateway=ping distance=1 gateway=192.168.12.1 routing-mark=to_WAN12 add check-gateway=ping distance=1 gateway=192.168.13.1 routing-mark=to_WAN13 add check-gateway=ping distance=1 gateway=192.168.14.1 routing-mark=to_WAN14 add check-gateway=ping distance=1 gateway=192.168.15.1 routing-mark=to_WAN15 add check-gateway=ping distance=1 gateway=192.168.16.1 routing-mark=to_WAN16 add check-gateway=ping distance=1 gateway=192.168.17.1 routing-mark=to_WAN17 add check-gateway=ping distance=1 gateway=192.168.18.1 routing-mark=to_WAN18 add check-gateway=ping distance=1 gateway=192.168.19.1 routing-mark=to_WAN19 add check-gateway=ping distance=1 gateway=192.168.20.1 routing-mark=to_WAN20 add check-gateway=ping distance=1 gateway=192.168.21.1 routing-mark=to_WAN21 add check-gateway=ping distance=1 gateway=192.168.22.1 routing-mark=to_WAN22 add check-gateway=ping comment="WAN-1 / DEFAULT ROUTE" distance=1 gateway=192.168.1.1
٩(●̮̮̃•̃)۶ ZaiB ٩(●̮̮̃•̃)۶

thank ur shared
LikeLike
Comment by omheru — June 18, 2011 @ 9:44 AM
plz sir mikrotik 4 wan backup to de do plzzzzzzzzzzz
LikeLike
Comment by maniimran7171 — September 25, 2013 @ 3:15 PM
nice how 10 wan load balasing
LikeLike
Comment by Aman Farooqi — June 19, 2011 @ 7:49 AM
Same as 4 WAN works, just add entries for as many dsl your system supports.
LikeLike
Comment by aacable — June 23, 2011 @ 8:36 AM
dear sir,
Fariya Or connect merge karna hain maray pas 750gl router hain main kasay karo or for example
connect pptp + Fariya pptp = lan dhcp with pptp
i need configration
LikeLike
Comment by yasir — September 6, 2014 @ 4:58 AM
hi,can u help me,just basic but i really dont know…when i follow the script,my internet dsl need to bridge or using pppoe??i very noob of it..please help me..
LikeLike
Comment by shey — April 24, 2013 @ 5:36 PM
I am new to this can you tell how to start the commands because whenever i try its saying that it doesnt match..Whats causing that???
LikeLike
Comment by Olexie Fennell — December 4, 2013 @ 10:26 PM
aslam akum janab muj tow wan one lan ki ka backp send ker plz only tow routr hai jas ki use ya ho rahi hai 192.168.13.3
192.168.13.2
LikeLike
Comment by irfan narejo — May 18, 2021 @ 12:26 PM
Aslam-o-oalikum
Sir ma nay mikrotik ka server install kiya whowa hai per jub ma DNS per ping lagata hoo too PIng MS 400 500 tak chal rahy hoty hai khabi normal 46 say 76 rahty hai too browing sahi chati hai.400 500 MS ka kiya malsa hai server ka ya kohi Aur…please help Me
LikeLike
Comment by zeshan — December 30, 2013 @ 11:16 PM
bhai setting ma msla hai no prblm
LikeLike
Comment by rana — January 12, 2014 @ 12:11 PM
good info, how to check if the network using pppoe
LikeLiked by 1 person
Comment by tq ur share — June 29, 2011 @ 5:43 PM
Try This one .
Load Balance Mikrotik with PCC using PPPoe-Client connection
First, make new mangle for mark connection, packet and routing :
/ ip firewall mangle
add chain=input in-interface=internet1 action=mark-connection new-connection-mark=internet1_conn
add chain=input in-interface=internet2 action=mark-connection new-connection-mark=internet2_conn
add chain=output connection-mark=internet1_conn action=mark-routing new-routing-mark=to_internet1
add chain=output connection-mark=internet2_conn action=mark-routing new-routing-mark=to_internet2
add chain=prerouting dst-address-type=!local in-interface=Local per-connection-classifier=both-addresses:2/0 \
action=mark-connection new-connection-mark=internet1_conn passthrough=yes
add chain=prerouting dst-address-type=!local in-interface=Local per-connection-classifier=both-addresses:2/1 \
action=mark-connection new-connection-mark=internet2_conn passthrough=yes
add chain=prerouting connection-mark=internet1_conn in-interface=Local action=mark-routing new-routing-mark=to_internet1
add chain=prerouting connection-mark=internet2_conn in-interface=Local action=mark-routing new-routing-mark=to_internet2
Than set the default route and fail over gateway : (change the ips according to your network design)
/ ip route
add dst-address=0.0.0.0/0 gateway=10.111.0.1 routing-mark=to_internet1 check-gateway=ping
add dst-address=0.0.0.0/0 gateway=10.112.0.1 routing-mark=to_internet2 check-gateway=ping
add dst-address=0.0.0.0/0 gateway=10.111.0.1 distance=1 check-gateway=ping
add dst-address=0.0.0.0/0 gateway=10.112.0.1 distance=2 check-gateway=ping
Last, set the NAT for local connection:
/ ip firewall nat
add chain=srcnat out-interface=internet1 action=masquerade
add chain=srcnat out-interface=internet2 action=masquerade
That is simple script for Load Balance Mikrotik with PCC using PPPoe-Client connection.
LikeLike
Comment by aacable — June 30, 2011 @ 5:51 AM
Asalam o Alikum
sir agar 9wan PPPoE Client Connection karni ho to plzzzz os ka bana dain plzzzzzzzzzzzzzzzzzzzzzzzz
LikeLike
Comment by Hamza Shaikh — July 4, 2013 @ 5:44 PM
So, to use this PPC script, i change the interface names to match my interface names and the ips to match my static ips?
Then i am good to go?
Thanks!
LikeLike
Comment by sam — July 2, 2011 @ 11:32 PM
yep.
LikeLike
Comment by aacable — July 4, 2011 @ 5:48 AM
plz sir koi mikrotik 4 wan backup to de do plzzzzzzzzzzzzzzzzzzzzzzzzzzzzzzzzzzzzzz
LikeLike
Comment by maniimran7171 — September 25, 2013 @ 3:13 PM
hi, thanks for the reply!
what is the purpose of these ping lines? are they necessary for the load balance to operate correctly on dsl?
are they supposed to be 0.0.0.0 or am i to change them to something?
/ip route
add dst-address=0.0.0.0/0 gateway=192.168.1.1 routing-mark=to_WAN1 check-gateway=ping
add dst-address=0.0.0.0/0 gateway=192.168.2.1 routing-mark=to_WAN2 check-gateway=ping
add dst-address=0.0.0.0/0 gateway=192.168.3.1 routing-mark=to_WAN3 check-gateway=ping
add dst-address=0.0.0.0/0 gateway=192.168.4.1 routing-mark=to_WAN4 check-gateway=ping
add dst-address=0.0.0.0/0 gateway=192.168.1.1 distance=1 check-gateway=ping
add dst-address=0.0.0.0/0 gateway=192.168.2.1 distance=2 check-gateway=ping
add dst-address=0.0.0.0/0 gateway=192.168.3.1 distance=3 check-gateway=ping
add dst-address=0.0.0.0/0 gateway=192.168.4.1 distance=4 check-gateway=ping
LikeLike
Comment by sam — July 4, 2011 @ 5:51 AM
check-gateway=ping is used in fail-over scenario. means if the gateway is not available mikrotik will not forward request to that link. its a fail-over feature.
LikeLike
Comment by aacable — July 4, 2011 @ 5:59 AM
great! so i change the 0.0.0.0 to the ip of where i wish to ping for checking link status/if im online on what wan?
LikeLike
Comment by sam — July 4, 2011 @ 6:00 AM
0.0.0.0/0 usually represents internet. or any other network that is not on your subnet.
don’t mix this with check-gateway=ping syntax.
LikeLike
Comment by aacable — July 4, 2011 @ 6:15 AM
Ok. Got is, so for example i could use
add dst-address=8.8.8.8/24 gateway=192.168.1.1 distance=1 check-gateway=ping
add dst-address=4.2.2.2/24 gateway=192.168.2.1 distance=1 check-gateway=ping
is the x.x.x.x/24 correct? or is 24 wrong?
LikeLike
Comment by sam — July 4, 2011 @ 6:18 AM
this line “ip route add dst-address=0.0.0.0/0 gateway=192.168.1.1” means that it will route any data that is not on your same subnet , to gateway 192.168.1.1 (dsl)
you don’t add command like this “add dst-address=8.8.8.8/24 gateway=192.168.1.1” its wrong.
use packet marking/mangling feature to route specific traffic to gateway of your choice. for example you can mark packets for youtube/fb and then in route you can decide that from which dsl/gateway should fb/youtube data go, (for load balancing) there are several types of load balancing available in mikrotik. Reat the wiki. use this example
http://wiki.mikrotik.com/wiki/Per-Traffic_Load_Balancing
http://wiki.mikrotik.com/wiki/Category:Routing
LikeLike
Comment by aacable — July 4, 2011 @ 6:25 AM
Dear Sir,
Related to fail over scenario, can it change ping to gateway to be ping to the dns such 8.8.8.8 or 8.8.4.4 (google) ?
Thanks,
Gumilar
LikeLike
Comment by gumilar — January 27, 2014 @ 5:45 PM
yes you can change to any destination you like
LikeLike
Comment by Syed Jahanzaib / Pinochio~:) — January 28, 2014 @ 3:07 PM
Hey, i really appreciate your help. I am new to mikrotik, but looking to understand it better. I have a 4 wan 450g to get working so i really appreciate your help!
Thanks for explaining the ip route line to me. So i dont change anything there but my gateway ip in that line.
Do you mind if i send you my draft of script and you let me know if everything is good once i have played around with it? I will only be on site for one day to actually test it, and if it doesnt work, im dead. but i have a week or so to play around.
Thanks again!
LikeLike
Comment by sam — July 4, 2011 @ 6:29 AM
send me a copy along with your network scenario , ip series or other possible detal on dsl.
LikeLike
Comment by aacable — July 4, 2011 @ 6:36 AM
will do!
i dont know the static ips until the tech comes in to install the dsl lines. BUT i can give you some other ips in place of them and i can easily change them out to the new ones.
Thanks!
LikeLike
Comment by sam — July 4, 2011 @ 6:45 AM
Hey,
I have a question you may be able to answer. I am trying to make it so the mikrotik router captures all DNS traffic and points it to opendns.
Is it a mangle script that does this?
We have the dns in the router for open dns, but i want to make sure people cant get around it.
Do you know how to write this script for opendns? (this may make a popular blog entry 😉
The OpenDNS nameservers are 208.67.222.222 and 208.67.220.220.
ill post it in the opendns community too.
LikeLike
Comment by sam — July 4, 2011 @ 7:11 PM
If you have a small lan, its better to use Mikrotik default dns server, and in mt dns forwarder, add opendns entries , this way all your users dns request will be fulfilled by opendns via mikrotik (you will be benefited with mikrotik dns cache facility)
or else Following is just simple firewall rule which will force all Your users behind mikrotik to use DNS server which You will define.
In /ip firewall filter nat
add chain=dstnat action=dst-nat to-addresses=192.168.1.1 to-ports=53 protocol=tcp dst-port=53
add chain=dstnat action=dst-nat to-addresses=192.168.1.1 to-ports=53 protocol=udp dst-port=53
This rule will force all users with custom defined DNS server to use 192.168.1.1 as their DNS server, this rule will simply redirect all request sent to ANY-IP:53 to 192.168.1.1:53
LikeLike
Comment by aacable — July 5, 2011 @ 5:47 AM
so i have a quite large LAN, so should i still use the mikrotik dns forwarder? or will the firewall rule acomplish the same thing?
do you have a script for quickly configuring the dns server? (this is where the lan will get DNS info via DHCP? so their computers will read the mikrotik gateway as the dns?) or is it a different area where dns server is configured?
With a very large and busy lan is it a good idea to have the mikrotik cache dns? (on a 450g)
thanks!
LikeLike
Comment by sam — July 8, 2011 @ 4:30 AM
Its generally not a good idea to use mikrotik as a dns server for really busy network. because mikrotik dns is not designed for heavy network load, however it works
.
If you have high load of users, its better to use another box preferably with linux as DHCP n DNS Server. Recevtly I done installation of relatively a large network with around 3000 Users, and I used UBUNTU linux as dhcp n dns server with DNS Cache service name DNSMASQ. Result was good, and it really reduce some load from mikrotik.
Read my story at : https://aacable.wordpress.com/2011/07/05/a-network-design-glass-line-pvt-ltd-june-2011/
LikeLike
Comment by aacable — July 8, 2011 @ 11:18 AM
and i take it 192.168.1.1 is the miktorik gateway lan ip address in this script?
LikeLike
Comment by sam — July 8, 2011 @ 4:32 AM
i read yr script
but i need to know how it work my dsl router
i hv 3 DSL {3 x (2Mb) = 6} connection i want to combine them together
how i merge 3 modems (LAN) outputs
plz help me
LikeLike
Comment by UsmanGhani — July 8, 2011 @ 1:46 PM
You can get combined bandwidth only if your carrier /ISP offers MLPPP.
to get near, you can use LOAD BALANCING method, including PCC,
read the mikrotik wiki and you will get many ideas on how to achieve this.
LikeLike
Comment by aacable — July 9, 2011 @ 9:24 AM
> and i take it 192.168.1.1 is the miktorik gateway lan ip address in this script?
> Comment by sam — July 8, 2011 @ 4:32 AM ”
The very first post with the PCC setup have 192.168.0.1 as mikrotik LAN for users.
but in the last post where I posted DNS server redirecting command, 192.168.1.1 is the LAN facing ethernet. it was an example. try to judge things by common sense :~) 😛
LikeLike
Comment by aacable — July 9, 2011 @ 5:43 AM
dear zaib
kia app teamviewer per mere router ki configration kr deen gay
via winbox
i hv 2 dsl connection
LikeLike
Comment by usman — July 10, 2011 @ 9:52 AM
Yeah sure, contact me aacable at hotmail.com
LikeLike
Comment by aacable — July 15, 2011 @ 7:41 AM
good zaib bhai Allah aap ko hamari help kernay ka Agar day Aameen
LikeLike
Comment by shoaib — July 1, 2013 @ 12:33 PM
add chain=prerouting dst-address-type=!local in-interface=Local per-connection-classifier=src-address:3/0 action=mark-connection new-connection-mark=WAN1_conn passthrough=yes
add chain=prerouting dst-address-type=!local in-interface=Local per-connection-classifier=src-address:3/1 action=mark-connection new-connection-mark=WAN2_conn passthrough=yes
add chain=prerouting dst-address-type=!local in-interface=Local per-connection-classifier=src-address:3/2 action=mark-connection new-connection-mark=WAN3_conn passthrough=yes
I CANT UNDERSTAND ABOVE
PLZ EXPLANE dst-address-type=!local
WHATS MEANS >>>>>> !local <<<<<<<<<
LikeLike
Comment by usman — July 10, 2011 @ 10:22 AM
As per Mikrotik Wiki explains:
“The first line means “produce the output of the hash function given the packet’s source IP address and port, divide it by 3 and if the remainder is 0, perform the action of marking the connection as 1st_conn”. The second line means “produce the output of the hash function given the packet’s source IP address and port, divide it by 3 and if the remainder is 1, perform the action of marking the connection as 2nd_conn”. And correspondingly the third line means “produce the output of the hash function given the packet’s source IP address and port, divide it by 3 and if the remainder is 2, perform the action of marking the connection as 3rd_conn”.
Read this link thoroughly and you will understand the voodoo 😉
http://wiki.mikrotik.com/wiki/How_PCC_works_%28beginner%29
LikeLike
Comment by aacable — July 10, 2011 @ 11:53 AM
[admin@MikroTik] /ip firewall mangle> add chain=prerouting dst-address-type=!
local in-interface=Local per-connection-classifier=src-addresses:3/2 action=mark
-connection new-connection-mark=WAN3_conn passthrough=yes
syntax error (line 1 column 42)
LikeLike
Comment by usman — July 10, 2011 @ 10:24 AM
There was some mistake in the post. Please change src-address from per-connection-classifier=src-addresses TO
per-connection-classifier=src-address:4/0 [or vise versa]
LikeLike
Comment by aacable — July 10, 2011 @ 12:02 PM
Hey,
I finally got my scripts all setup, and i started plugging them in to my 450g. (i reset config, and chose not to have the default start up script)
Everything i had was accepted fine, but this portion is giving me a syntax error right at the “src-addresses” portion. I am looking at another 450g that has the same setup, and in winbox it has the Local per-connection-classifier set to “both” I did not set that up, so i dont know what it really means.
Any tips?
/ip firewall mangle
add chain=prerouting dst-address-type=!local in-interface=Local per-connection-classifier=src-addresses:4/0 action=mark-connection new-connection-mark=WAN1_conn passthrough=yes
add chain=prerouting dst-address-type=!local in-interface=Local per-connection-classifier=src-addresses:4/1 action=mark-connection new-connection-mark=WAN2_conn passthrough=yes
add chain=prerouting dst-address-type=!local in-interface=Local per-connection-classifier=src-addresses:4/2 action=mark-connection new-connection-mark=WAN3_conn passthrough=yes
add chain=prerouting dst-address-type=!local in-interface=Local per-connection-classifier=src-addresses:4/3 action=mark-connection new-connection-mark=WAN4_conn passthrough=yes
LikeLike
Comment by sam — July 13, 2011 @ 10:17 PM
Dear Jahanzaib Sir,
I want to build a chache server in afghanistan in my ISP.
also I want to make a hotspot card system.
need you contact no. to talk you about that.
LikeLike
Comment by Afghan Cyber ISP — March 7, 2014 @ 9:22 PM
“/ip firewall mangle> add chain=prerouting dst-address-type=!
local in-interface=Local per-connection-classifier=src-addresses:3/2 action=mark
-connection new-connection-mark=WAN3_conn passthrough=yes
syntax error (line 1 column 42)”
There was some mistake in the post. Please change src-address from per-connection-classifier=src-addresses TO
per-connection-classifier=src-address
LikeLike
Comment by aacable — July 15, 2011 @ 8:27 AM
salam sir mere pass 4 DSL Lin hai dsl ke kya ap muje kar k dege load balance mikrotik pe muje nai hata hai sir
LikeLike
Comment by khalid sam — June 28, 2012 @ 2:44 PM
hello
LikeLike
Comment by phool zia — March 3, 2016 @ 7:16 PM
dear sir i want share internet fron VPN so plz if u give me some script
LikeLike
Comment by malik — July 13, 2011 @ 6:13 PM
Try PPPoE , its more secure than VPN ,
http://wiki.mikrotik.com/wiki/Pppoe_server_with_profiles
http://seoroot.com/blog/networking/setting-up-mikrotik-pppoe-server.html
LikeLike
Comment by aacable — July 15, 2011 @ 6:45 AM
i used ur sripts very nice work very fine but it allow all users directly i want to allow internet by vpn
LikeLike
Comment by malik — July 13, 2011 @ 6:16 PM
l like this post but please can i have your contact number so i can contact you clear some of my questions
LikeLike
Comment by owais — July 14, 2011 @ 7:12 AM
contact me aacable at hotmail.com
LikeLike
Comment by aacable — July 15, 2011 @ 7:41 AM
dear sir pls give me some script i have 4 dsl line or ur contact
LikeLike
Comment by malik — July 25, 2011 @ 8:27 PM
You can get the script in this post, just read it fully n will find what u r looking for.
or contact me at aacable [at] hotmail.com
LikeLike
Comment by Pinochio / zaib — July 26, 2011 @ 6:05 AM
Nice work you doing zaib.
i am new about mikrotik. i am using mikrotik router os (on pc) v.2.2.10 is it possible to make it 4xWan (dsl link bind or load balancing) and 1Xlan
and what is pcc i dont know about it will you share link or abrevation of pcc
LikeLike
Comment by waqas — July 29, 2011 @ 12:26 PM
v.2.2.10 :S thats way too old.
please upgrade to latest version for reliable load balancing.
PCC = per connection classifier
Read some basic info on PCC
http://wiki.mikrotik.com/wiki/Manual:PCC
http://wiki.mikrotik.com/wiki/How_PCC_works_%28beginner%29
LikeLike
Comment by Pinochio / zaib — July 29, 2011 @ 5:51 PM
hi !
Very nice article. I am trying to implement something similar but with a big difference. I don’t have multiple gateways. I have multiple dynamic ips given by my internet provider and I want my routerboard to “split” the traffic on these different interfaces (based on traffic type). To simplify let’s say that I have two wan interfaces wan1 and wan2 directly connected to internet with external ips and same gw (obtained thru dhcp). How could I adapt your script to load balance these two interfaces ?
thanks in advance !
LikeLike
Comment by ashmodai — August 8, 2011 @ 3:28 PM
Simple ! instead of ‘gateway=1.2.3.4’ use ‘gateway=pppoe-out1’ or wan1 or wan2
Also this link will help yo in splitting traffic base on TRAFFIC type.
http://wiki.mikrotik.com/wiki/Per-Traffic_Load_Balancing
Reagrd’s
zaiB !
LikeLike
Comment by Pinochio / zaib — August 8, 2011 @ 6:11 PM
Thanks for your very quick answer ! but what about the pre routing ones ?
add chain=prerouting dst-address=192.168.1.0/24 action=accept in-interface=Local
Since I don’t have two subnets ?
LikeLike
Comment by ashmodai — August 9, 2011 @ 11:07 AM
oops sorry I am stupid 🙂 forget my question and thanks again !
LikeLike
Comment by ashmodai — August 9, 2011 @ 11:15 AM
Oups … it does work fine but I am facing a strange side effect. The fetch tool used for dyndns on my router does not return any result any more ?
LikeLike
Comment by ashmodai — August 9, 2011 @ 2:29 PM
do some r&D and see which part of script is having trouble with DYNDNS.
have u tried
http://forum.mikrotik.com/viewtopic.php?f=9&t=50415
http://wiki.mikrotik.com/wiki/Dynamic_DNS_Update_Script_for_dynDNS
LikeLike
Comment by Pinochio / zaib — August 9, 2011 @ 2:38 PM
Yes actually the script I use is very similar. It was working fine until I activate the second wan interface. It looks almost like since the connection is originating from the router itself it is not marked and therefore not routed anywhere. Possible ?
LikeLike
Comment by ashmodai — August 9, 2011 @ 2:42 PM
Actually to complement my message the part of the script having issue is the “fetch” command which is never returning any value if i have the two wan interfaces active
LikeLike
Comment by ashmodai — August 10, 2011 @ 9:01 PM
I made some trials yesterday and I can confirm that the issue is with the ip routing. Deleting the new routes solve the issue …
LikeLike
Comment by ashmodai — August 11, 2011 @ 5:15 PM
Great stuff! It works like a charm. Any idea what this will do to VPN services on the WAN1 side of things?
LikeLike
Comment by Matthew Adam Byrd — August 17, 2011 @ 8:03 PM
Unable to understand what you meant by ‘VPN services on the WAN1 side of things?’
Can you please describe more briefly.
LikeLike
Comment by Pinochio / zaib — August 18, 2011 @ 10:55 AM
I’ve got the load balancing side working. Now I’m going to add PPTP/L2TP services to the WAN1 and WAN2 interface. Will the load balancing interfere with the PPTP/L2TP services?
LikeLike
Comment by Matthew Adam Byrd — August 18, 2011 @ 5:16 PM
I have never tested it in LB scenario. But I am sure it will work fine. Please test and share your experience 🙂
However I personally not recommend to do so due to the load balancing inter-connectivity with the WAN interfaces.
LikeLike
Comment by Pinochio / zaib — August 18, 2011 @ 6:24 PM
It doesn’t work with PPTP services… I’m still checking the Mikrotik forum for a workaround but so far no such luck.
LikeLike
Comment by Matthew Adam Byrd — August 23, 2011 @ 1:32 AM
I may have just fixed the PPTP services with PCC… I created an address list and on the mangle rules I did a src-address-list=!pptpusers and dst-address-list=!pptpusers
LikeLike
Comment by Matthew Adam Byrd — August 23, 2011 @ 1:51 AM
With your exclusion address list I get better results but mixed. I will need to test from an outside wifi since I don’t know if the issue is coming from my mobile network provider. Sounds promising ! Thanks for sharing !
LikeLike
Comment by ashmodai — August 23, 2011 @ 2:25 AM
I have the same issue. Since i implemented load balancing VPN is not working 😦 if you find a solution please share it here ! Thanks !
LikeLike
Comment by Asmodai — August 23, 2011 @ 1:38 AM
You may try Matthew Adam Byrd suggestion.
Just create an address list and on the mangle rules exclude them , e.g src-address-list=!pptpusers and dst-address-list=!pptpusers
Comment by Matthew Adam Byrd — August 23, 2011 @ 1:51 AM | Edit This
LikeLike
Comment by Pinochio / zaib — August 23, 2011 @ 10:54 AM
It is verified working 😉
LikeLike
Comment by Matthew Adam Byrd — August 23, 2011 @ 4:57 PM
Thanks a lot to all ! I finally got it working but adding this exclude list AND add to it not only the pptp users dedicated addresses but also the two external wan ips … by the way this also solved my dyndns scripts that were not working either anymore since I implemented load balancing.
LikeLike
Comment by ashmodai — August 24, 2011 @ 3:29 AM
That’s Great ! We are glad you have managed to solve your problem 🙂
LikeLike
Comment by Pinochio / zaib — August 24, 2011 @ 10:48 AM
Looks like the cfg i’ve been using for over a year, nice to see the info on how to do it is now easier to find!!
One thing I’m trying to figure out is how to do fail over, we’ve got a few DSL lines that you can ping up to the gateway, but after that, nothing gets out. and it seems after the line dies, we lose net access entirely off the Mikrotik 493AH unless we reboot the modem, or remove it from the PCC list. Have you come across a way to do that via script?
LikeLike
Comment by Drew — August 30, 2011 @ 1:11 AM
Maybe this will help you.
:local i 0; {:do {:set i ($i + 1)} while (($i < 3) && ([/ping 8.8.8.8 interval=2 routing-table=ISP1-Test count=3]<=1))};
:local x 0; {:do {:set x ($x + 1)} while (($x < 3) && ([/ping 8.8.8.8 interval=2 routing-table=ISP1-Test count=3]<=1))};
:local y 0; {:do {:set y ($y + 1)} while (($y < 3) && ([/ping 8.8.8.8 interval=2 routing-table=ISP1-Test count=3]=3 && $x>=3 && $y>=3) do={
:log info "ISP1 Down";
/ip address disable [find comment="ISP1 One-To-One NAT"];
/ip address enable [find comment="ISP2 One-To-One NAT"];
/ip firewall nat disable [find comment="ISP1 One-To-One NAT"];
/ip firewall nat enable [find comment="ISP2 One-To-One NAT"];
/ip route disable [find comment=ISP1];
} else { :log info "ISP1 UP";
/ip address enable [find comment="ISP1 One-To-One NAT"];
/ip address disable [find comment="ISP2 One-To-One NAT"];
/ip firewall nat enable [find comment="ISP1 One-To-One NAT"];
/ip firewall nat disable [find comment="ISP2 One-To-One NAT"];
/ip route enable [find comment=ISP1];
}
Also in order for this to work properly you need to disable the check-gateway function inside of “/ip routes”. The reason for this is because it will disable any of the same route if one of them has check-gateway enabled.
Also read the following.
http://forum.mikrotik.com/viewtopic.php?f=3&t=38023
But personally I have never tested it or integrate it with pcc in any setup. If you find its working solution to integrate failover with pcc, do let me know 🙂
LikeLike
Comment by Pinochio / zaib — August 30, 2011 @ 10:52 AM
Sir,
we have started cablenet & Hotspot service. currently we are using Mikrotik 3.20 ver with Wifi Card & Single NIC, i have 2 ISPs connected with Switch and used on tht single NetworkCard. one is on PPPOE Dialer another with Static IP.. i dont knwo howto utalize both links with single End User.
LikeLike
Comment by Fast Net — September 2, 2011 @ 3:36 PM
3.20 ?? I am sure it must be the cracked version 🙂 I cannot really provide your any better support in this version.
I suggest you to BUY the Licensed version which is 5.6 at a moment. Which have very nice load balancing method known as PCC (Per Connection Classifier) which can combine multiple WAN links at very best and with multiple methods available.
Provide me some info first,
Currently Are you doing any kind of load balancing using both links ? if yes, what method you are using ?
LikeLike
Comment by Pinochio / zaib — September 2, 2011 @ 5:45 PM
Dear , we are currently using linux based indian software (and want to switch to MT). for this purpose i just shared the both connections to Hotspot and LAN users using mark-routing . we upgraded MT to 5.6 but wifi clients were having disconnection problem.
LikeLike
Comment by Fast Net — September 4, 2011 @ 1:02 AM
Hi,
Is it possible with Mikrotik to load balancing fail over but checking not the gateway, but other ip behind the gateway. To be sure that there’s reachability after the gateway. Because the gateway can be reachable and that gateway itself don’t have reacheability and checking the gateway will always tell you that all is ok.
You know like IP SLA on Cisco routers. Is it an script on MIKROTIK to check reachability behind the gateway?
Germain
LikeLike
Comment by Germain — September 15, 2011 @ 9:58 PM
I am not aware of the method,
However it can be done by customized netwatch scripts that can work with PCC
LikeLike
Comment by Pinochio~:) — October 10, 2011 @ 3:23 PM
Salaam,
Can you please upload/or send a link in which it shows the configuration of mikrotik pcc load balancing. Also which ips do i need to change in this configuration?
LikeLike
Comment by Nouman Aziz — October 13, 2011 @ 4:42 AM
You have to change dsl modems ips to match with the examples given in this article. OR change the ips in the script as it suites you. Its easier to change the modem ips.
LikeLike
Comment by Pinochio~:) — October 13, 2011 @ 10:36 AM
So I just canage ip’s as below? Correct me if Im wrong
192.168.1.2 = WAN1
192.168.2.2 = WAN2
192.168.3.2 = WAN3
192.168.4.2 = WAN4
Also I have configured it. But the loging page didn’t came on. So I typed in ip address, then loged into mikrotik but internet did not came on! Tell me what I might be doing wrong?
Thank you
LikeLike
Comment by Nouman Aziz — October 14, 2011 @ 12:57 PM
What exactly “loggin page” is? This script does not create any hotspot type login page. This is just to load balance 4 wan links. This is fully tested in many networks and working good.
LikeLike
Comment by Pinochio~:) — October 14, 2011 @ 2:00 PM
sorry leave hotspot page. My mistake just answer first question.
Do I just change modem ip’s to the listed above?
LikeLike
Comment by Nouman Aziz — October 14, 2011 @ 4:28 PM
I’m starting to think that 5.7 has broken the setup. I don’t seem to have fault tolerance anymore. Are any of you guys still using this with 5.7?
LikeLike
Comment by Matthew Adam Byrd — October 20, 2011 @ 6:29 PM
LikeLike
Comment by Matthew Adam Byrd — October 20, 2011 @ 6:43 PM
Ignore this… a very very strange coincidence but my ISP for the secondary 10mbit connection actually assigned my static IP to another CPE so it wasn’t surfing. All is well in the land of the load balanced Mikrotik!
LikeLike
Comment by Matthew Adam Byrd — October 20, 2011 @ 7:31 PM
🙂
LikeLike
Comment by Pinochio~:) — October 21, 2011 @ 10:44 AM
Hi, this is really nice but I have different case. My scenario is to use 2x WAN and 3x LAN (same network, DHCP Server on all three). When I come to lines with following “mangle” rules:
add chain=prerouting dst-address-type=!local in-interface=Local per-connection-classifier=both-addresses-and-ports:4/0 action=mark-connection new-connection-mark=WAN1_conn passthrough=yes
….. etc
do I have to create all possibilities in my scenario because I have wan1, wan2, lan1, lan2 and lan3 interfaces? Should I enter something like following:
add chain=prerouting dst-address-type=!local in-interface=lan1 per-connection-classifier=both-addresses-and-ports:2/0 action=mark-connection new-connection-mark=WAN1_conn passthrough=yes
add chain=prerouting dst-address-type=!local in-interface=lan1 per-connection-classifier=both-addresses-and-ports:2/1 action=mark-connection new-connection-mark=WAN2_conn passthrough=yes
add chain=prerouting dst-address-type=!local in-interface=lan2 per-connection-classifier=both-addresses-and-ports:2/0 action=mark-connection new-connection-mark=WAN1_conn passthrough=yes
add chain=prerouting dst-address-type=!local in-interface=lan2 per-connection-classifier=both-addresses-and-ports:2/1 action=mark-connection new-connection-mark=WAN2_conn passthrough=yes
add chain=prerouting dst-address-type=!local in-interface=lan3 per-connection-classifier=both-addresses-and-ports:2/0 action=mark-connection new-connection-mark=WAN1_conn passthrough=yes
add chain=prerouting dst-address-type=!local in-interface=lan3 per-connection-classifier=both-addresses-and-ports:2/1 action=mark-connection new-connection-mark=WAN2_conn passthrough=yes
LikeLike
Comment by Jovan P — October 21, 2011 @ 6:10 PM
I guess you have already been replied on the mikrotik forum, you have pasted the same thread in the forum too.
LikeLike
Comment by Pinochio~:) — October 22, 2011 @ 2:35 PM
Yes, I found solution but I was waiting and was unpatient 🙂 Thanks, anyhow!
LikeLike
Comment by Jovan P — October 22, 2011 @ 5:06 PM
I have router IP as
192.168.8.254 WAN1
192.168.6.254 WAN2
And out Interface is 192.168.9.1 as out ip address.
so where do i change address and how because i have changed your script but no internet out off mikrotik kindly help me because i don’t want to change router ip address .
Naveed
naveed.innocent@yahoo.com
LikeLike
Comment by Naveed Akhter — October 24, 2011 @ 3:24 PM
Find along with attachment is Mikrotik PCC script, customized according to your requirement.
It may work fine. If not please do some googling.
/ip address
add address=192.168.9.1/24 network=192.168.9.0 broadcast=192.168.9.255 interface=Local
add address=192.168.8.254/24 network=192.168.8.0 broadcast=192.168.8.255 interface=WAN1
add address=192.168.6.254/24 network=192.168.6.0 broadcast=192.168.6.255 interface=WAN2
/ip dns set allow-remote-requests=yes cache-max-ttl=1w cache-size=5000KiB max-udp-packet-size=512 servers=221.132.112.8,8.8.8.8
/ip firewall mangle
add chain=input in-interface=WAN1 action=mark-connection new-connection-mark=WAN1_conn
add chain=input in-interface=WAN2 action=mark-connection new-connection-mark=WAN2_conn
add chain=output connection-mark=WAN1_conn action=mark-routing new-routing-mark=to_WAN1
add chain=output connection-mark=WAN2_conn action=mark-routing new-routing-mark=to_WAN2
add chain=prerouting dst-address=192.168.8.0/24 action=accept in-interface=Local
add chain=prerouting dst-address=192.168.6.0/24 action=accept in-interface=Local
add chain=prerouting dst-address-type=!local in-interface=Local per-connection-classifier=both-addresses-and-ports:2/0 action=mark-connection new-connection-mark=WAN1_conn passthrough=yes
add chain=prerouting dst-address-type=!local in-interface=Local per-connection-classifier=both-addresses-and-ports:2/1 action=mark-connection new-connection-mark=WAN2_conn passthrough=yes
add chain=prerouting connection-mark=WAN1_conn in-interface=Local action=mark-routing new-routing-mark=to_WAN1
add chain=prerouting connection-mark=WAN2_conn in-interface=Local action=mark-routing new-routing-mark=to_WAN2
/ip route
add dst-address=0.0.0.0/0 gateway=192.168.8.254 routing-mark=to_WAN1 check-gateway=ping
add dst-address=0.0.0.0/0 gateway=192.168.6.254 routing-mark=to_WAN2 check-gateway=ping
add dst-address=0.0.0.0/0 gateway=192.168.8.254 distance=1 check-gateway=ping
add dst-address=0.0.0.0/0 gateway=192.168.6.254 distance=2 check-gateway=ping
/ip firewall nat
add chain=srcnat out-interface=WAN1 action=masquerade
add chain=srcnat out-interface=WAN2 action=masquerade
LikeLike
Comment by Pinochio~:) — October 25, 2011 @ 3:36 PM
It,s not working , when i write 192.168.6.254 to open modem through mozilla it opens configuration panel of mikrotik webconfig and also on 192.168.9.1 when i disconnect modem 192.168.6.254 form mikrotik it still pings it in terminal..kindly help..
LikeLike
Comment by naveed akhter — November 4, 2011 @ 10:30 AM
There are few ways you can do it.
if you use PCC than you know the result of PCC classifier in your mangle creates two different packet or connection markers. Each of these are than the source for two different policy routing rules.
Now all you need to do is to make sure that the destination addresses of the two modem is not passed through the PCC process but get a dedicated set packer or connection marker which as result give them the proper routing mark and route to reach the right destination.
So what you do is set a packet or connection marker rule BEFORE the PCC rules where traffic coming from (src address classifier) your PC and going TO (dst address classifier) (and for instance tcp protocol on port 80) get their own mark.
Upon this manually assigned mark the traffic hits the designed routing marker rule and gets the desired route.
Or just accept the traffic in those rules before PCC. That way the traffic is exempted from PCC and the normal routing table is used.
The following solution will surely work for you I m sure.
Create following rules and move the /ip firewall mangle TOP in the mangle rules, above all rules.
/ip firewall address-list
add list=exempt-from-pcc address=192.168.6.254/32
/ip firewall mangle
add chain=prerouting dst-address-list=exempt-from-pcc action=accept
(make sure this rule is above all other rules.)
LikeLike
Comment by Pinochio~:) — November 14, 2011 @ 10:53 AM
Hello sir,….
I have tried to apply this way, at 10 WAN but not run properly, about what obstacles I experienced? thank you
LikeLike
Comment by Linambaran Faradha Qisthas — November 2, 2011 @ 3:01 AM
It depends on what rules you have added accordingly for 10 WAN.
Email me your complete PCC script that you are using for 10 WAN and I will see what could be possibly wrong in it.
LikeLike
Comment by Pinochio~:) — November 2, 2011 @ 10:49 AM
It depends on what rules you have added accordingly for 10 WAN.
Email me your complete script and I will see what could be possibly wrong in it.
LikeLike
Comment by Pinochio~:) — November 2, 2011 @ 10:50 AM
if you allow and favor, I beg permission, to put this blog link on my blog, thanks
LikeLike
Comment by Linambaran Faradha Qisthas — November 2, 2011 @ 3:07 AM
Sure , You can use it on your blog. Its under G.P.L 🙂
LikeLike
Comment by Pinochio~:) — November 2, 2011 @ 10:48 AM
I have posted on this forum,
http://forum.mikrotik.com/viewtopic.php?f=2&t=56315
please help me solve the problem. and thank for your allowing to put your blog link.
warm regards
HP Tio
LikeLike
Comment by Linambaran Faradha Qisthas — November 2, 2011 @ 1:00 PM
I have posted on the forum below
http://forum.mikrotik.com/viewtopic.php?f=2&t=57001
so Can any one help me
thanks
LikeLike
Comment by saly — November 27, 2011 @ 3:10 PM
What exactly is your requirement ?
is load balancing not working ?
or script not working ?
LikeLike
Comment by Pinochio~:) — November 28, 2011 @ 11:07 AM
I deployed your script but I want Internet Download Manager to use both line wan1 and wan2 at the same time so download speed will be doubled.
My current status is as much users browsing the loadbalance be better.
In real I use this script in Internet Cafe so I want my customers see the speed in the internet download manager program increasing
thanks a lot
LikeLike
Comment by saly — November 28, 2011 @ 11:41 AM
Sir i have done loadbalancing using pcc method .my problem is when i plug second wan link …routerboard hanged .and hotsopt stop working ….my local ip is 172.16.0.1….wan 1 is 4 mb and wan 2 is 2 mb …..plz advise …
Regards
LikeLike
Comment by faisalmirzapk — April 10, 2012 @ 12:11 AM
I don’t understand why its hanging. have you configured the pcc rules accordingly to 2 wan? Also hotspot with pcc doesn’t work, you have to create addition rule for it.
LikeLike
Comment by Syed Jahanzaib / Pinochio~:) — April 10, 2012 @ 8:54 AM
yes sir i have configure pcc rules …my lan ip is 172.16.0.1/16 ? wan networks are : 192.168.1.0,192.168.2.0/24…?
LikeLike
Comment by faisalmirzapk — April 10, 2012 @ 5:48 PM
Thanks …now working after adding rule.
LikeLike
Comment by faisalmirzapk — April 12, 2012 @ 12:46 AM
If you use per-connection-classifier = both-addresses-and-ports
Then It will use all wan links and you will see speed increment in IDM downloads.
LikeLike
Comment by Pinochio~:) — November 28, 2011 @ 3:51 PM
This is the Best Site i ever Seen .. Thanks a Lot Bro.. you r the genious ……….
LikeLike
Comment by Tanz — November 30, 2011 @ 1:21 AM
Dear Bro can u pls teach us how to merge 12 hours(2 mbps only 21:00 to 8 AM) Bandwidth with 24 Hours 1 Mbps Load balance
Like 15 ADSL 512k/1024k with 512k/2048 Bandwidth
LikeLike
Comment by Tanz — November 30, 2011 @ 1:24 AM
Unable to understand your question. please be specific.
LikeLike
Comment by Pinochio~:) — November 30, 2011 @ 10:44 AM
Dear Sir,
I attached 750 with my system. I am getting follow error on 750 router board which I got from log file :
Buffer memory
Topics
dhcp
error
Message dhcp-client on WAN1 failed to add IP address 192.168.1.2: already have such address (6)
Kindly help me .
Thank you.
Muhammad Fawad
LikeLike
Comment by Muhammad Fawad — December 1, 2011 @ 10:37 AM
Hello Bro
I used :
per-connection-classifier=both-addresses-and-ports:2/0
per-connection-classifier=both-addresses-and-ports:2/1
As your script mentioned
So can we alter this to obtain double speed in Internet Download Manager
thanks a lot
LikeLike
Comment by saly — December 1, 2011 @ 5:48 PM
JAZAKALLAH bahi sahib …. Really thankful to u for this post but need some assistance please explain
1). i have only 3 wan (4+4+2 mb) . Trying to modified. Is this Right WAN1 =4MB WAN2=4MB WAN3=2MB,,,,,, 😉
/ip address
add address=192.168.0.1/24 network=192.168.0.0 broadcast=192.168.0.255 interface=Local
add address=192.168.1.2/24 network=192.168.1.0 broadcast=192.168.1.255 interface=WAN1
add address=192.168.2.2/24 network=192.168.2.0 broadcast=192.168.2.255 interface=WAN2
add address=192.168.3.2/24 network=192.168.3.0 broadcast=192.168.3.255 interface=WAN3
/ip firewall mangle
add chain=input in-interface=WAN1 action=mark-connection new-connection-mark=WAN1_conn
add chain=input in-interface=WAN2 action=mark-connection new-connection-mark=WAN2_conn
add chain=input in-interface=WAN3 action=mark-connection new-connection-mark=WAN3_conn
add chain=output connection-mark=WAN1_conn action=mark-routing new-routing-mark=to_WAN1
add chain=output connection-mark=WAN2_conn action=mark-routing new-routing-mark=to_WAN2
add chain=output connection-mark=WAN3_conn action=mark-routing new-routing-mark=to_WAN3
add chain=prerouting dst-address=192.168.1.0/24 action=accept in-interface=Local
add chain=prerouting dst-address=192.168.2.0/24 action=accept in-interface=Local
add chain=prerouting dst-address=192.168.3.0/24 action=accept in-interface=Local
add chain=prerouting dst-address-type=!local in-interface=Local per-connection-classifier=both-addresses-and-ports:5/0 action=mark-connection new-connection-mark=WAN1_conn passthrough=yes
add chain=prerouting dst-address-type=!local in-interface=Local per-connection-classifier=both-addresses-and-ports:5/1 action=mark-connection new-connection-mark=WAN1_conn passthrough=yes
add chain=prerouting dst-address-type=!local in-interface=Local per-connection-classifier=both-addresses-and-ports:5/2 action=mark-connection new-connection-mark=WAN2_conn passthrough=yes
add chain=prerouting dst-address-type=!local in-interface=Local per-connection-classifier=both-addresses-and-ports:5/3 action=mark-connection new-connection-mark=WAN2_conn passthrough=yes
add chain=prerouting dst-address-type=!local in-interface=Local per-connection-classifier=both-addresses-and-ports:5/4 action=mark-connection new-connection-mark=WAN3_conn passthrough=yes
add chain=prerouting connection-mark=WAN1_conn in-interface=Local action=mark-routing new-routing-mark=to_WAN1
add chain=prerouting connection-mark=WAN2_conn in-interface=Local action=mark-routing new-routing-mark=to_WAN2
add chain=prerouting connection-mark=WAN3_conn in-interface=Local action=mark-routing new-routing-mark=to_WAN3
/ip route
add dst-address=0.0.0.0/0 gateway=192.168.1.1 routing-mark=to_WAN1 check-gateway=ping
add dst-address=0.0.0.0/0 gateway=192.168.2.1 routing-mark=to_WAN2 check-gateway=ping
add dst-address=0.0.0.0/0 gateway=192.168.3.1 routing-mark=to_WAN3 check-gateway=ping
add dst-address=0.0.0.0/0 gateway=192.168.1.1 distance=1 check-gateway=ping
add dst-address=0.0.0.0/0 gateway=192.168.2.1 distance=2 check-gateway=ping
add dst-address=0.0.0.0/0 gateway=192.168.3.1 distance=3 check-gateway=ping
/ip firewall nat
add chain=srcnat out-interface=WAN1 action=masquerade
add chain=srcnat out-interface=WAN2 action=masquerade
add chain=srcnat out-interface=WAN3 action=masquerade
REGARDS
WAQAS AHMAD
LikeLike
Comment by WAQAS AHMAD — December 6, 2011 @ 7:07 PM
Seems fine to me 🙂 Go ahead and test
But remember, you can’t get 100% even result, but anything near even 60-70% will be considered fine.
LikeLike
Comment by Pinochio~:) — December 7, 2011 @ 1:33 PM
sir lan merge script give me my email addr: nasir_rahman86@yahoo.com
plzzzzzzzzzzzzzzzzzzzzzzzzzzzzzzz
LikeLike
Comment by zeeshan — December 14, 2011 @ 10:05 AM
Dear Jhanzaib Bhai
Assalam O Allaykum
muje 190 users run karne hai rb450g pe with pppoe (maximum active clients 80)
aur 4mb ke 4 (4+4+4+4) line hai yani 16mb total
aur per user 3pm-3am 512kbit aur 3am-3pm unlimited speed deni hai
to mere liye load combiner compatible rahega ya load balance
PLEASE TELL ME ????
I AM WAITING ………………
LikeLike
Comment by zohaib — December 7, 2011 @ 1:15 PM
Both will work fine.
Mikrotik base Load balancer have added benefit that you can use src-address as classifier. using this technique you will be safe from broken links, broken download, streaming freezing etc which is very common in every load balancer. IF you want to get combined bandwidth from all Links, then use both-address-and-ports
But again its up to you to test which method is best suited as per your network users habit. Its all about research and testing.
LikeLike
Comment by Pinochio~:) — December 7, 2011 @ 1:30 PM
is your RB450G working best for 80active clients. im planning to buy that RB. THank You
FAST ISP
03008403633
Hammad Hassan
LikeLike
Comment by hammad hassan — February 1, 2013 @ 8:30 AM
Yes RB450G works fine for 80 users. However it also depends on the configuration / firewall /mangle rules. Also try to avoid simple queues. instead using simple queues, try to use pcq.
LikeLike
Comment by Syed Jahanzaib / Pinochio~:) — February 1, 2013 @ 8:43 AM
Im new in Mikrotik.
What is PCQ??
Aur main Hotspot main koi Mangle ya firewall nahi laga raha. Jst Hotspot aur “simple queues” mere liye zarori hai. k main client ko kitni speed dena chahta hon. main hotspot user profile main speed limitation rakhta hoon….
tu kia RB450G thek work nahi kare ga?
LikeLike
Comment by hammad hassan — February 1, 2013 @ 2:08 PM
Per Connection Queue (PCQ) is a queuing discipline that can be used to dynamically equalize or shape traffic for multiple users, using little administration. It takes less resources as compared to simple queues. Also it supports many customization like equal bandwidth for a number of users, certain bandwidth equal distribution between users, unknown bandwidth equal distribution between users.
Like this.
http://wiki.mikrotik.com/wiki/Manual:Queues_-_PCQ_Examples
LikeLike
Comment by Syed Jahanzaib / Pinochio~:) — February 3, 2013 @ 11:32 AM
This load balancing merge all link into 1 or not ?
like if i have 4mb 4 dsl & when i download any file it show 16mb or not ?
LikeLike
Comment by sunny — December 15, 2011 @ 12:40 PM
Hi everyone, nice post! I want to use load balancing on mikrotik for two wans. But I wanted ask you a question before implement it:
– The load balancing above described don’t make problem about voip connections and https website? Or it is possible say to mikrotik that all connections about voip and https must go out through only one wan?
Thank you in advance!
Gio
LikeLike
Comment by Giovanni Piemontese — December 15, 2011 @ 3:32 PM
If you want to use VOIP / HTTPS , its better to use SRC_ADDRESS as your classifier.
This way you wont be able to get combined bandwidth of both link but There will be no connection resetting / broken links problem.
Or you can use traffic base routing and set your desired gateway for your makred traffic.,
LikeLike
Comment by Pinochio~:) — December 15, 2011 @ 4:02 PM
Thank you for your quickly reply. I prefer get combined bandwith avoiding connection resetting / broken links problem. So I think that the second implementation is better but i need to understand too how to implement it. For setting desidered gateway for marked traffic (voip, https, streaming etc…), I have to do it in nat section or direclty in mangle rules? Can u make please a short example for me?
Thank u very much for your time!
Best Regards,
gio
LikeLike
Comment by Giovanni Piemontese — December 15, 2011 @ 4:23 PM
So you want to go with Traffic base routing. (Which I will recommend you because some services/apps requires dedicated connection) , Please read the following article which describes very well on howto classify traffic and route them to various links.
http://wiki.mikrotik.com/wiki/Per-Traffic_Load_Balancing
LikeLike
Comment by Pinochio~:) — December 16, 2011 @ 10:50 AM
Yes it will merge /load balance all the WAN to give you combined bandwidth. (If you are using both-address-and-ports as your classifier as mentioned in this post)
LikeLike
Comment by Pinochio~:) — December 15, 2011 @ 3:35 PM
Hi, I need help, a make this script to my MK 5.7 but not working!
My WAN lines are form dhcp servers form ISPs
One of te routing add dst-address=0.0.0.0/0 gateway=192.168.2.1 distance=2 check-gateway=ping showed in blue color and not doing trafic!!
Another problem that I have, I have question about DNS, two ISP- have diferent DNS, have can I balanc the DNS???
LikeLike
Comment by Elhem — December 16, 2011 @ 10:36 PM
If a route is showing in blue color, it’s just inactive. Finger it.
Regarding DNS, It’s not much important to use Both ISp’s DNS.
Make sure your clients are using MIKROTIk as there primary dns server.
On mikrotik server, use primary/secondary dns pointing to ISP-1 and ISP-2 respectively.
LikeLike
Comment by Pinochio~:) — December 19, 2011 @ 10:49 AM
Zaib thanks man, I trying to change distance in my dynamic route but is inposible, I tryting to set 0 distance to my static ruote but is unaceptable!Any helpe please!
LikeLike
Comment by Elhem — December 20, 2011 @ 3:56 AM
Hmm its strange. I told one of my friend to check this script at his setup (who is already using this script at his setup to load balance 4 wan links) and he informed me that it’s working fine.
Do one thing , Simply reset all configuration, and re-configure it and check it again.
One More Guess, Are you using any pppoe server on the same mikrotik?
LikeLike
Comment by Pinochio~:) — December 20, 2011 @ 12:56 PM
Bro Zaib, Im not using any ppoe-server in my MK, I using two routers to get internet connection (IP dimaic) in my MK from two ISP, because if I use PPOE-Client I can not change the IP route (ISP gives it to by default).
LikeLike
Comment by Elhem — December 20, 2011 @ 4:33 PM
Zaib is OK now, is working, reconfigure all script and now working, anytime I have some problems with http, and with Youtube, any solution??!
LikeLike
Comment by Elhem — December 20, 2011 @ 9:39 PM
You have to try several classifier to sort out http/s+streaming breaking issue. Start with src-address
using src-address, user will be stick to the specific link, his wan link will not be load balance, he will always use the same wan link at which PCC bind with it.
LikeLike
Comment by Pinochio~:) — December 21, 2011 @ 10:47 AM
Zaib god bless you man, man like you are very special, I wish you a long and happy life! thanks for heping.If you can post any script (example) for this solution!?
LikeLike
Comment by Elhem — December 22, 2011 @ 6:29 AM
unable to understand what solution you are asking?
LikeLike
Comment by Pinochio~:) — December 22, 2011 @ 11:05 AM
Zaib I think about this:several classifier to sort out http/s+streaming breaking issue. Start with src-address, If you can post exaple (scrip). thnks
LikeLike
Comment by Elhem — December 22, 2011 @ 12:40 PM
Just replace both-addressess-and-ports with src-address in all lines . Example.
add chain=prerouting dst-address-type=!local in-interface=Local per-connection-classifier=src-address:4/0 action=mark-connection new-connection-mark=WAN1_conn passthrough=yes
LikeLike
Comment by Pinochio~:) — December 22, 2011 @ 12:52 PM
Yes Bro I make this change, but now when I test download bandwith, only one of two lines geting me speed (ps.10 mb) another line not doing nothing!
LikeLike
Comment by Elhem — December 22, 2011 @ 4:34 PM
Zaib is OK now, I Just replace both-addressess-and-ports with src-address in all line and working soo good! THANKS MAN!
LikeLike
Comment by Elhem — December 22, 2011 @ 9:06 PM
Bro Zaib I upload the printscr, please take e look and see my problem, Im waiting for your help. pls….
LikeLike
Comment by Elhem — December 17, 2011 @ 4:14 AM
Hi, I don’t know if this is normal or a problem of route configuration. I have the same situation and mikrotik routes all traffic on wan1. Can anyone help us?
Thanks in advance.
Gio
LikeLike
Comment by Giovanni Piemontese — December 18, 2011 @ 7:34 PM
FOCUS on ‘distance’ value.
The dynamic route has a distance of 0, and your static route has a distance of 1. The lower distance wins.
Make all route’s distance same i.e 1.
LikeLike
Comment by Pinochio~:) — December 19, 2011 @ 10:50 AM
Focus on DISTANCE value.
The dynamic route has a distance of 0, and your static route has a distance of 1. The lower distance wins.
Try to make ‘distance’ value 0 or 1 for all routes.
LikeLike
Comment by Pinochio~:) — December 19, 2011 @ 10:51 AM
Hi, I have set all routes to distance 1 as you suggested but now all traffic use only wan2 and wan1 is blue become. Here a screenshoot of ip route on mikrotik:
Thanks in advance.
Gio
LikeLike
Comment by Giovanni Piemontese — December 19, 2011 @ 4:00 PM
Sir, can u help me please? As before all traffic of pppoe clients go out through only one wan (the active route). Why? Now all routes have the same distance but one reamain always blue. Thank u in advance.
LikeLike
Comment by Giovanni Piemontese — December 19, 2011 @ 11:28 PM
If you have PPPoE Server on the Same mikrotik where PCC is also configured.
Then use the following Link.
LikeLike
Comment by Pinochio~:) — December 20, 2011 @ 1:36 PM
Hi Sir, I have already followed this tutorial with pppoe server but it doesn’t work.. I have pppoe server with dhcp configured and then the rest is the same as this post/tutorial. So I don’t understand why one route remain always blue and traffic go out only one interface. There is a method so u can see my configuration?
Thank u in advance.
Gio
LikeLike
Comment by Giovanni Piemontese — December 20, 2011 @ 3:21 PM
Giovanni is not a normal, I think a problem is on OS 5.7, I waiting for Zaib help, hi is expert.
LikeLike
Comment by Elhem — December 19, 2011 @ 4:10 AM
Bro I can’t change it. I trying in my Ip route but, still showing 0 distance ip route of my ISP!?
LikeLike
Comment by Elhem — December 20, 2011 @ 3:20 AM
Thanks Alot bro your script work for me …………….. great job
LikeLike
Comment by waqar hameed — January 2, 2012 @ 12:16 PM
I am glad it helped you 🙂
LikeLike
Comment by Syed Jahanzaib / Pinochio~:) — January 3, 2012 @ 11:22 AM
thank u so much bro….. Very Appreciated work … spread the knowledge
LikeLike
Comment by Mobeen Ahmad — January 4, 2012 @ 2:07 PM
good evening bro
and assalamualaikum (if you moslem)
your tutor is really great….
but i have problem in loadbalancing PCC…
i have try all PCC method..
but when i change server for texas holdem poker…
its always reconect…
i use RB 750 with mt v5.11
big thanks for helping bro…
LikeLike
Comment by iamspailham — January 11, 2012 @ 2:15 PM
Wa Alaekum Assalam,
Use src-address as your classifier. It will solve your problem.
Or dedicate this web site ip to always go through dedicated wan link.
LikeLike
Comment by Syed Jahanzaib / Pinochio~:) — January 11, 2012 @ 2:19 PM
thanks for you reply….
but it still reconect….
i have use src-address..
but stil reconect bro…
i also use external proxy for caching
this is my mangle
[admin@MUTIARA.NET] > ip fi mangle pr
Flags: X – disabled, I – invalid, D – dynamic
0 ;;; PROXY-HIT
chain=prerouting action=mark-packet new-packet-mark=PROXY-HIT
passthrough=no dscp=12
1 ;;; LOADBALANCING SPEEDY
chain=input action=mark-connection new-connection-mark=internet1_conn
passthrough=yes in-interface=modem-1-dial
2 chain=input action=mark-connection new-connection-mark=internet2_conn
passthrough=yes in-interface=modem-2-dial
3 chain=output action=mark-routing new-routing-mark=to_internet1
passthrough=yes connection-mark=internet1_conn
4 chain=output action=mark-routing new-routing-mark=to_internet2
passthrough=yes connection-mark=internet2_conn
5 ;;; LOKAL
chain=prerouting action=mark-connection new-connection-mark=lokal1_conn
passthrough=yes protocol=tcp dst-address-type=!local in-interface=lokal
dst-port=!80,81,8080,3128,21 per-connection-classifier=src-address:2/0
6 chain=prerouting action=mark-connection new-connection-mark=lokal2_conn
passthrough=yes protocol=tcp dst-address-type=!local in-interface=lokal
dst-port=!80,81,8080,3128,21 per-connection-classifier=src-address:2/1
7 chain=prerouting action=mark-routing new-routing-mark=lokal1_route
passthrough=yes in-interface=lokal connection-mark=lokal1_conn
8 chain=prerouting action=mark-routing new-routing-mark=lokal2_route
passthrough=yes in-interface=lokal connection-mark=lokal2_conn
9 ;;; PROXY
chain=prerouting action=mark-connection new-connection-mark=proxy1_conn
passthrough=yes protocol=tcp dst-address-type=!local in-interface=PROXY
dst-port=80,81,8080,3128,21 per-connection-classifier=src-address:2/0
10 chain=prerouting action=mark-connection new-connection-mark=proxy2_conn
passthrough=yes protocol=tcp dst-address-type=!local in-interface=PROXY
dst-port=80,81,8080,3128,21 per-connection-classifier=src-address:2/1
11 chain=prerouting action=mark-routing new-routing-mark=proxy1_route
passthrough=yes in-interface=PROXY connection-mark=proxy1_conn
12 chain=prerouting action=mark-routing new-routing-mark=proxy2_route
passthrough=yes in-interface=PROXY connection-mark=proxy2_conn
and this is my route
# DST-ADDRESS PREF-SRC GATEWAY DISTANCE
0 A S ;;; PCC LOKAL
0.0.0.0/0 modem-1-dial 1
1 A S 0.0.0.0/0 modem-2-dial 1
2 A S ;;; PCC PROXY
0.0.0.0/0 modem-1-dial 1
3 A S 0.0.0.0/0 modem-2-dial 1
5 A S ;;; DEFAULT GATEWAY….
0.0.0.0/0 modem-1-dial 1
thank you my brother….
LikeLike
Comment by iamspailham — January 11, 2012 @ 4:10 PM
Assalaam o Alekom
sir……i have a 4 dsl lines on birdge mode and i wan’t to connect mikrotik routerOS with pcc load balance.
how to configure this senerio can you help me?
Thanks!
LikeLike
Comment by M,Salman — January 14, 2012 @ 4:25 AM
Just create pppoe client connection, they will auto connect.
then use the following script , adjust it according to your scenario.
http://mikrotikz.blogspot.com/2010/07/load-balance-mikrotik-with-pcc-using.html
LikeLike
Comment by Syed Jahanzaib / Pinochio~:) — January 14, 2012 @ 10:41 AM
salam sir
sir plz mikrotik 3.30 per 4wan pcc load balancing with hotspot server ka script de dain shuktia
LikeLike
Comment by noshad — January 15, 2012 @ 10:33 PM
Search the forums. Hotspots don’t work out of the box with PCC. Several threads contain workarounds. On the same box the workarounds are fairly complicated. The simplest option is to buy a RB750 or comparable router or add another mikrotik PC and use it for PCC, and to put the Hotspot server behind it
However following is some working configuration posted by Fewi. You can modify it according to your need.
http://forum.mikrotik.com/viewtopic.php?p=175525#p175525
LikeLike
Comment by Syed Jahanzaib / Pinochio~:) — January 15, 2012 @ 11:10 PM
Assalam o Alekom
Thanks
sir………they are working…..! but sir……that is pppoe-client failover senerio 1st down then 2nd up, i want to merge with pcc loadbalancing on bridge mode 4 adsl line.
LikeLike
Comment by M,Salman — January 16, 2012 @ 5:28 AM
sir ye mikrotik ki products pakistan me kahan se hasil ki ja sakti hain
LikeLike
Comment by noshad — January 16, 2012 @ 10:00 AM
You can get Mikrotik products from
Dreams Network Technology
Karachi , Pakistan
http://www.dreamnw.com/contact_us.html
Office : A-1349 Gulshan-e-Hadeed Phase-1 Karachi
Contact No: +923132118237 , +923332828526
Email: info@dreamnw.com
You can give them my reference.
LikeLike
Comment by Syed Jahanzaib / Pinochio~:) — January 16, 2012 @ 10:44 AM
Assalam o Alekom
Thanks
sir………they are working…..! but sir……that is pppoe-client failover senerio 1st down then 2nd up, i want to merge with pcc loadbalancing on bridge mode 4 adsl line.
LikeLike
Comment by M,Salman — January 17, 2012 @ 3:46 AM
The link provided is just an idea, modify it according to your requirements.
LikeLike
Comment by Syed Jahanzaib / Pinochio~:) — January 18, 2012 @ 10:42 AM
Sir pcc load balancing aur hotspot server ke liya koon koon sa router board kharid loon
LikeLike
Comment by noshad — January 17, 2012 @ 5:38 PM
depend on number of users / firewall rules / filtering etc.
usually RB450 or RB405G is good choice for small size networks.
LikeLike
Comment by Syed Jahanzaib / Pinochio~:) — January 18, 2012 @ 10:33 AM
sir kia aik hi he kharidoon ya do le loon (hotspot with pcc load balancing)
LikeLike
Comment by noshad — January 18, 2012 @ 11:39 AM
It’s better if you separate both services,
One for hotspot
Second for PCC
LikeLike
Comment by Syed Jahanzaib / Pinochio~:) — January 18, 2012 @ 12:00 PM
sory sory sir likhna ye tha k
hotspot server & pcc load balancing dono ke liye aik hi RB450 kafi ho ga ya do alag alag lene honge
thanks
LikeLike
Comment by noshad — January 18, 2012 @ 1:02 PM
acha sir wireless pe pppoe aur hotspot dono me kia behtar he ya agar koi aur mashwara he to wo de dain
thanks
LikeLike
Comment by noshad — January 18, 2012 @ 1:16 PM
pppoe is much secure then hotspot.
both services have there positive and negatives, however pppoe wins in many aspects, go for it.
A HOTSPOT is way to provide internet access to subscribers by means of an easy to use login interface as it does not require any client software/driver/dialer at user end. To log in, users may use almost any web browser , so they are not required to install additional software.It is also possible to allow users to access some web pages without authentication using Walled Garden feature.
In my personnel opinion, Hotspot is best suited for ad hoc situations, where you cannot control how the client has their machines configured. This is generally useful in Conference Rooms, Hotels, Cafe’s , Restaurants and likewise since people will come and go and you have few permanent users.
One big advantage of using hotspot is that HotSpot does not require any client software/driver/dialer. One disadvantage of using HotSpot is that its usually requires your client to open up his browser to log in before he can use your service . So users wanting to connect to your service using a router or some kind usually have a problem (as routers usually don’t support logging in via HTTP).
LikeLike
Comment by Syed Jahanzaib / Pinochio~:) — January 18, 2012 @ 5:39 PM
sir aap ka ye aik bohat acha qadam he Allah aap ko jaza de
LikeLike
Comment by noshad — January 18, 2012 @ 1:18 PM
salam sir
poochna ye tha ke hotspot server with pcc load balancing ke liye aik hi RB450 kafi ho ga ya do alag alag lene honge ?
LikeLike
Comment by noshad — January 18, 2012 @ 9:50 PM
1 RB450 is enough, Try it.
Usually its not recommended to run both services (pcc+hotspot) on same router due to its complexity.
However you can try it on single RB if you have some budget related issues.
LikeLike
Comment by Syed Jahanzaib / Pinochio~:) — January 18, 2012 @ 11:16 PM
SALAM SIR
related with comment no 74
so sir plz give me the script (hotspot with pcc)
advice me can i try it on pc first
i am already using ubnt bullet 2hp with 12dbi dlink omni and behind this i am using pcc with ppoe server on a single pc
i observed when the number of connected clients exceeded more then almost ten the system not worked properly sending and receiving data become very low i think the bullet can handle only 25 or 25 ips at a time
therefore i want to try hotspot server what is your opinion about that matter plz guide me
thank u very much
Allah hafiz
LikeLike
Comment by noshad — January 19, 2012 @ 10:32 AM
Dear I have never tested or worked with PCC+HOTSPOT on same Mikrotik.
It is not recommended to use hotspot and pcc on same mikrotik, BUT still you can make it work.
there are few workarounds for it,
Just add
hotspot=auth
in all pcc rules.
Search the mikrotik forums and you will find few working scripts for it.
LikeLike
Comment by Syed Jahanzaib / Pinochio~:) — January 19, 2012 @ 11:16 AM
IN TAMAM KHUDA TARSIYOUN AUR MEHERBANIYOUN KA SHUKRIA
LikeLike
Comment by noshad — January 19, 2012 @ 10:56 AM
hello i use the script from first post and it works fine for outgoing connections.
but portforward from wan1 to network cam port 80 in local net didn’t work (in connection table i see network-cam connections marked with to_wan3).
when i forward from wan3 it works. how can i tell the pcc that incoming connections goes out through the same interface as they come in
LikeLike
Comment by vectrum — January 20, 2012 @ 4:50 PM
no reply for me?
LikeLike
Comment by vectrum — January 24, 2012 @ 1:54 AM
What was your question?
I have to answers several threads per day, so its possible that Your thread left un-answered.
Please post your query again.
LikeLike
Comment by Syed Jahanzaib / Pinochio~:) — January 24, 2012 @ 11:26 AM
Asslam-o-aikum, sir!
Please correct the mistake bellow, i`m to much tried but fail.
add chain=prerouting dst-address-type=!local in-interface=Local per-connection-classifier=both-addresses-and-ports:2/0 action=mark-connection new-connection-mark=WAN1_conn passthrough=yes
add chain=prerouting dst-address-type=!local in-interface=Local per-connection-classifier=both-addresses-and-ports:2/1 action=mark-connection new-connection-mark=WAN2_conn passthrough=yes
Thanks in advance
LikeLike
Comment by smn4all — January 21, 2012 @ 9:45 PM
What’s the error you are getting
LikeLike
Comment by Syed Jahanzaib / Pinochio~:) — January 22, 2012 @ 12:19 PM
per-connection-classifier=both-addresses-and-ports:2/0 action=mark-connection new-connection-mark=WAN1_conn passthrough=yes
This one , when i past it into new terminal the it say “syntax error (line 1 column 42)” ( per-connection-classifier=both-addresses-and-ports:2/0 action=mark-connection )
LikeLike
Comment by smn4all — January 22, 2012 @ 12:28 PM
@ smn4all,
You must Mikrotik version 3.30 or above.
IF you are using older version, UPGRADE or buy licensed version.
LikeLike
Comment by Syed Jahanzaib / Pinochio~:) — January 22, 2012 @ 5:26 PM
Sir!
I`m using Mikrotik 3.9 version, but it is not working script .
per-connection-classifier=both-addresses-and-ports:2/0 action=mark-connection new-connection-mark=WAN1_conn passthrough=yes
This one , when i past it into new terminal the it say “syntax error (line 1 column 42)” ( per-connection-classifier=both-addresses-and-ports:2/0 action=mark-connection )
LikeLike
Comment by smn4all — January 22, 2012 @ 7:00 PM
First learn howto copy paste rules in mikrotik. You must be aware of some basic while dealing with mikrotik.
Try posting this line. This is complete one line.
/ip firewall mangle add chain=prerouting dst-address-type=!local in-interface=Local per-connection-classifier=both-addresses-and-ports:4/0 action=mark-connection new-connection-mark=WAN1_conn passthrough=yes
If it works, modify your rules
LikeLike
Comment by Syed Jahanzaib / Pinochio~:) — January 23, 2012 @ 11:45 AM
Asslam-o-alaikum, bhai! i`ve checked your given lines but it is not working again ERROR is
” bad argument name per-connection-classifier (line 1 column 85) “
LikeLike
Comment by smn4all — January 23, 2012 @ 4:05 PM
Only two possibilities.
1# You are using older version then 3.30
2# You are not pasting rules correctly, try typing them and see at which exact wording its giving error , Then sort it out.
# Also try to use some common logic’s.
LikeLike
Comment by Syed Jahanzaib / Pinochio~:) — January 24, 2012 @ 11:16 AM
my question again:
i use the script from first post and it works fine for outgoing connections.
but portforward/dstnat from wan1 to a network cam port or other devices in local net didn’t work smoothly (in connection table i see network-cam connections marked with to_wan3).
when i forward from wan3 it works. how can i tell the pcc that incoming dstnat connections goes out through the same wan interface as they come in?
LikeLike
Comment by vectrum — January 25, 2012 @ 4:46 AM
I have not used port forwarding , may be this link will help you.
Fewi @ mikrotik forum have explained it very well.
Read it
http://forum.mikrotik.com/viewtopic.php?f=2&t=49581
http://forum.mikrotik.com/viewtopic.php?f=2&t=45974
LikeLike
Comment by Syed Jahanzaib / Pinochio~:) — January 25, 2012 @ 11:13 AM
salam bhai
kia aisa ho sakta he k pcc loadbalancing server ka aik ya akik se ziada modem internet dena band kar dain lekin powered on hoon to mikrotik un ko request bhejna band kar de
shukria
LikeLike
Comment by noshad — January 29, 2012 @ 9:29 PM
Yes its possible through some modified scripting integrated with the pcc.
LikeLike
Comment by Syed Jahanzaib / Pinochio~:) — January 30, 2012 @ 10:48 AM
related with 82 (Yes its possible through some modified scripting integrated with the pcc.)
salam
to sir plz help kar dain
LikeLike
Comment by noshad — January 30, 2012 @ 1:59 PM
salam sir
sir main ne 2 dsl lagaye hain load balancing ki script sahi tarah kam nahi kar rahi chalte chalte net ruk jati hai aur thori der bad khud chalna start ho jathi hai dono dsl main plz rep the solution
LikeLike
Comment by umer — February 1, 2012 @ 8:38 AM
as salaam alaikum
4 DSL lines, but all load goes to only 1 DSL meri pass ye peroblam horahi hai iam new planes help me
LikeLike
Comment by ALi — February 2, 2012 @ 12:19 AM
Try removing CHECK-GATEWAY entries
LikeLike
Comment by Syed Jahanzaib / Pinochio~:) — February 2, 2012 @ 10:38 AM
thank for your response meri problem solv hogiy hai, one more question 4 MB ka 4 dsl combine speed deasakte hai
aur ek bate is Script mine hotspot aad kia hai login page nahi show kereta dns name typ kerna perta hai, thanks
LikeLike
Comment by ALi — February 3, 2012 @ 2:19 AM
you can combine as many wan links you like. just use the script with both-address-and-ports and it will combine the badnwidth.
for hotspot with pcc, Just add
hotspot=auth
in all pcc rules.
LikeLike
Comment by Syed Jahanzaib / Pinochio~:) — February 3, 2012 @ 6:54 PM
How you manage to solve “all loads goes to single WAN only” issue?
LikeLike
Comment by Syed Jahanzaib / Pinochio~:) — February 3, 2012 @ 6:54 PM
hello jahanzaib sir
sir app na pcc load balancing ki script di usa ma na used ki magr us ma ak problem ai ha ka ak getaway add hua magr dusra nahi sir plz helo me
LikeLike
Comment by shail2234 — February 3, 2012 @ 11:38 PM
reset all settings, and then configure it again, this time line by line,so that you can track at which point , the script is giving you error, note that error and fix it on appropriate section.
LikeLike
Comment by Syed Jahanzaib / Pinochio~:) — February 4, 2012 @ 9:34 AM
ma mikrotik 3.30 used kar raha with pppoe server
LikeLike
Comment by shail2234 — February 3, 2012 @ 11:40 PM
salaam Syed Jahanzaib
i m from karachi.
i want contact u to configure for my network plz contact
my number +92-300-2496909
thanx
best regard
shahbaz usman.
LikeLike
Comment by shahbaz usman — February 4, 2012 @ 11:05 PM
You can send me your requirements at my email aacable [at] hotmail.com ,
LikeLike
Comment by Syed Jahanzaib / Pinochio~:) — February 5, 2012 @ 10:28 AM
Asslam-o-laikum, bhai!
Mikrotik 4 WAN Load Balancing using PCC method. Complete Script ! only work on MIkrotik 4.0 and above versions of mikrotik. Now please give me solution for mikrotik 3.xx versions
Thanks
LikeLike
Comment by smn4all — February 10, 2012 @ 1:18 PM
Asslam-o-alaikum, bhai!
Mikrotik 4 WAN Load Balancing using PCC method. Complete Script ! only work on MIkrotik 4.0 and above versions of mikrotik. Now please give me solution for mikrotik 3.xx versions
Thanks
LikeLike
Comment by smn4all — February 10, 2012 @ 1:20 PM
This works on Mikrotik 3.30 and above.
So if you have 3.30 it can work fine. Its tested
LikeLike
Comment by Syed Jahanzaib / Pinochio~:) — February 10, 2012 @ 2:59 PM
Bhai!
Main ne bhot dafa test kia hai lakin ya mikrotik 4 plus version pe chalta hai 3.3 plus pe nai chalta …….
LikeLike
Comment by smn4all — February 10, 2012 @ 3:47 PM
I won’t argue with you.
But it do works with mirkotik ver 3.30 and above.
3.30 (not 3.3)
LikeLike
Comment by Syed Jahanzaib / Pinochio~:) — February 10, 2012 @ 4:45 PM
asalam-o-alikum sir mare pass broadcast ho rahi ha ,
To sir is ka kohi rule ha broadcast rokna ka
plz sir help me
LikeLike
Comment by shail2234 — February 12, 2012 @ 11:10 PM
There are various types of broadcast, Which type you are asking about 😀
LikeLike
Comment by Syed Jahanzaib / Pinochio~:) — February 14, 2012 @ 9:07 AM
salaam \
plz tell me and help me
i am useing mikrotik 3.30 MY LOAD BALASING IS PCC BUT MY PROBLAM IS WEBPROXY IS NOT WORK WITH PPPOE SERVER
JAB PROXY PAR LAGTA HOO TO NET DISABILE HO JATA HAI KIA KARO
LikeLike
Comment by MANI — February 14, 2012 @ 12:42 PM
Web proxy usually don’t work with PCC. You have to create some extra rules in order to make it work.
It’s more simpler if you add external proxy server along with mikrotik to make things simpler and more efficient and easy to troubleshoot.
LikeLike
Comment by Syed Jahanzaib / Pinochio~:) — February 14, 2012 @ 7:03 PM
Slam bhai!
User-manager is working in Mikrotik 3.30, please give me any solution ….
LikeLike
Comment by smn4all — February 14, 2012 @ 3:44 PM
Slam bhai!
User-manager is not working in Mikrotik 3.30, please give me any solution …
LikeLike
Comment by smn4all — February 14, 2012 @ 3:45 PM
Dear Sir,
I am using RB750 for load balancing and x86 system for mikrotik hotspot. I am suing two PTCL DSL lines for load balancing. I am unable to access winbox via port forwarding. I have already sent you both scripts for guidance. Please help me in this regard.
Thank you.
Muhammad Fawad
LikeLike
Comment by Muhammad Fawad — February 15, 2012 @ 10:24 AM
Dear Sir,
I am still waiting for your kind reply.
Muhammad Fawad
LikeLike
Comment by Muhammad Fawad — February 20, 2012 @ 12:48 PM
Here is a very good discussion and its solution regarding PCC and Port Forwarding.
http://forum.mikrotik.com/viewtopic.php?f=2&t=45974
LikeLike
Comment by Syed Jahanzaib / Pinochio~:) — February 20, 2012 @ 2:19 PM
A good discussion and solution regarding PCC and Port forward is available here.
LikeLike
Comment by Syed Jahanzaib / Pinochio~:) — February 20, 2012 @ 2:20 PM
Selam Zaib, I have one problem with dns, on my clients pc-s I have configured this dns primary 80.80.160.8 and sec 80.80.160.9!
Now I change ISP and the dns of new ISP are 213.163.97.5 and 213.163.97.10 in my mikrotik I make this configuration:
chain=dstnat action=dst-nat to-addresses=213.163.97.5 dst-address=80.80.160.8
chain=dstnat action=dst-nat to-addresses=213.163.97.10 dst-address=80.80.160.9
But I have problem with msn messenger, msn closed avery 3-4 minuts and open again!!
I haved the same problem when I make the load balancin PCC the two diferent ISP not worked bicouse this was a problem MSN!!!
Please any help bro?
LikeLike
Comment by Ahmet — February 16, 2012 @ 3:01 AM
The first thing is Don’t provide public DNS server directly to your user,
Use your mikrotik internal ip as there primary dns server. and in mikrotik DNS, use your ISP or standard DNS servers like google 8.8.8.8
Second, You can forcefully route client DNS request to your mikrotik DNS server, this way no matter what dns server client have in there network settings, they will be routed to your mikrotik.
maybe it can work for you
http://forum.mikrotik.com/viewtopic.php?f=2&t=54300
/ip firewall nat add protocol=udp dst-port=53 action=redirect to-ports=53
/ip firewall nat add protocol=tcp dst-port=53 action=redirect to-ports=53
LikeLike
Comment by Syed Jahanzaib / Pinochio~:) — February 16, 2012 @ 9:22 AM
Aslam o alikum
Bro. will this pcc script will result like this…
1mbps + 1mbps + 1mbps + 1mbps = 4mbps internet connection downstream on single file over single client in LAN…
or this will provide 4 files 1 mbps that is about ~128 kbps transfer rate…. as all normal routers do.
i am basically have virtually privding internet to my firends and relitives in my area via W LAN
about 40 users.
will this combine bandwidht to single file or as normal tp-link load balancers do…
provides 1 mbps speed max to single file …. 4 files can have benefit of 4 mb.
sory for bad english as i am just 16 year old ….
i hope i have eleborated my point well.
thanks.
LikeLike
Comment by Billy — February 18, 2012 @ 3:43 AM
PCC doesn’t combine bandwidth. Its possible only if MLPP or by any method your ISP allows/provide on some extra charge.
PCC only load balance user request among multiple WAN Links.
If you will using any IDM type application, a single client can use the whole bandwidth because of multiple HTTP request request fetched from multiple mirror downloads location.
If a single client is download single file via normal browser , it will be using only one link.
The more load you put on it, the better chances would be to get good load balancing.
Its also depends on your classifier. Focus on it
LikeLike
Comment by Syed Jahanzaib / Pinochio~:) — February 18, 2012 @ 12:53 PM
You have done a really nice work by sharing a knowledge BUT dealing with Soooooo many reaplies its BRILLIANT 🙂 Keep it up
LikeLike
Comment by Sohail — February 19, 2012 @ 1:29 AM
Thanks bro
LikeLike
Comment by Syed Jahanzaib / Pinochio~:) — February 19, 2012 @ 7:43 PM
Dear sir,,
how teo set contention ratio for user in mikrotik 5.8
LikeLike
Comment by Muhammad kazim — February 20, 2012 @ 10:28 AM
Dear sir,,
how to set contention ratio for user in mikrotik 5.8
LikeLike
Comment by Muhammad kazim — February 20, 2012 @ 10:29 AM
What you exactly meant by “contention ratio” ?
LikeLike
Comment by Syed Jahanzaib / Pinochio~:) — February 20, 2012 @ 11:08 AM
dear sir
I am working in isp at kabul.I am using Mikrotik 5.8.I ahve 5 interfaces.In each interface have different address connected with rocket M5 ubiquiti.I have some clients in CIR and some 1:2 to shared so what can i do in this sacuation.
LikeLike
Comment by Muhammad kazim — February 20, 2012 @ 1:22 PM
You haven’t mentioned your query clearly. What’s the goal ?
LikeLike
Comment by Syed Jahanzaib / Pinochio~:) — February 20, 2012 @ 2:14 PM
salam jahanzaib bhai i need ur skype id so please tell me here my cell phone number is +92-332-2222-320 and i need ur help for load balancing
LikeLike
Comment by Syed Muhammad Hamza Naushahi — February 20, 2012 @ 11:10 AM
I don’t use SKYPE.
Post your query here at forum or use the EMAIL.
LikeLike
Comment by Syed Jahanzaib / Pinochio~:) — February 20, 2012 @ 11:20 AM
Thanks bro….
all i wanted now is cracked makrotik version which can do PCC i have downloaded from your friend urdu tutorial but a got error bad package 0,0
or error cddrive is crupted.
can i have a link please.
is there any system requirements ?
all i want to do is PCC load balancing i have system with 1 Ghz process 8o GB baracoda HDD with 7200 rpm and 512Mhz RAM.
with 1 built in lan on mmother borad and.
5 pci LAN adapters.
your help is precious.
LikeLike
Comment by billy — February 21, 2012 @ 12:26 AM
Have you tried this link ?
https://aacable.wordpress.com/tag/aacable-mikrotik-crack/
LikeLike
Comment by Syed Jahanzaib / Pinochio~:) — February 21, 2012 @ 9:35 AM
aslam o alikum i m back again with another problem…
i have installed makrotik ROS 3.3 and cracked it with level 6 license..
i have configured it as u have mentioned…
but now i want to confugre its hotspot i have tried about 100 plus times …
using winbox
/ip hotspot
added server on local interface with ip range 192.168.0.2/24 – 192.168.0.254/24
dns server ip 192.168.0.1
dns server name http://www.billynet.com
added user admin with admin password
but when user or client opens any webpage …..
its not redirecting them to any page….
only an error is displayed
this page is not available…
but when user types…
192.168.0.1/login
or
http://www.billynet.com/login
a login page is displayed.
whereas 192.168.0.1 is ip of local interface and ip of dns server as defined in
/ip dns
dns server ip 192.168.0.1
dns server name http://www.billynet.com
please help me 😦
LikeLike
Comment by billy — February 23, 2012 @ 1:33 AM
IS you rmikrotik hotspot server properly connected to internet ? can you able to ping any web site from terminal ?
make sure it is connected.
From client end, open command prompt, and try to ping any web site
like
ping google.com
Client must be able to resolve ip address of google.com , otherwise he will not be able to see the login page.
LikeLike
Comment by Syed Jahanzaib / Pinochio~:) — February 23, 2012 @ 9:08 AM
i have connected dsl router to wan 1
dsl router ip 192.168.1.1
when i directly connect to my dsl router net is working…
but when i contect through local port of MT ROS.
i cant access internet
while pinging router gateway 192.168.0.1
ping result is destination net unreachable
while pinging google.com
ping is blank
and after manually opening hotspot login page and after providing login and user name.
the ping result is as following
ping 192.168.0.1 result <1ms
and ping google.com
ping is blank.
any suggestion.
when i am directly connected to my dsl router i can ping google as well as other website.
LikeLike
Comment by billy — February 23, 2012 @ 1:52 PM
when i ping via winbox
tools ping option
ping google.com
is blank
ping 8.8.8.8
result is inbetween 280ms to 317ms
i am confused 😦
will u please check my settings via teamviewer.
please:(
LikeLike
Comment by billy — February 23, 2012 @ 2:08 PM
i just reinstalled and then cracked makrotik 3.3 with level 6
then via console of makrotik i typed each and every command as it as same sequence and same parameters.
i have re configured each and every bit of setting…. result is same.
with gateway as
192.168.0.1
and dns as 192.168.0.1
no browsing no download 😦
please help. 😦
LikeLike
Comment by billy — February 23, 2012 @ 10:37 PM
Can i use this method + hotspot on RB750GL?
i use the latest version 5.14
it work without hotspot , there anything i can do?
Thanks in advance.
LikeLike
Comment by Ahmed Fathi — February 24, 2012 @ 8:22 AM
TO make PCC work with Hotspot, follow the below guide
LikeLike
Comment by Syed Jahanzaib / Pinochio~:) — February 24, 2012 @ 9:26 AM
hey does this work with hotspot cuz i tried the NTH way it worked but when i add the hotspot it dosn’t work .. ty
LikeLike
Comment by Aladdin — February 24, 2012 @ 8:30 AM
i also have version 5.14 on RG750GL
LikeLike
Comment by Aladdin — February 24, 2012 @ 8:32 AM
LikeLike
Comment by Syed Jahanzaib / Pinochio~:) — February 24, 2012 @ 9:26 AM
Hi,
First off , awesome sharing of knowledge which is much appreciated.
I’d like your thoughts on something I’m trying to do. I’m trying to load balance voip only over 2 adsl links, preferably each session going over a different adsl line, source ip is always the same, destination ip is always the same , just ports change per call.
Any assistance is greatly appreciated
LikeLike
Comment by Nitrious — February 25, 2012 @ 1:29 AM
You can load balance your clients request in various ways.
Either via PCC with src-address as classifier,
or client base routing to marked gateway.
For example.
LikeLike
Comment by Syed Jahanzaib / Pinochio~:) — February 25, 2012 @ 12:41 PM
Hi,
Thanks for your quick response, I will give it a try. Really nice to be able to bounce ideas off someone who knows their stuff.
Regards,
Nitrious
LikeLike
Comment by Nitrious — February 25, 2012 @ 4:24 PM
salam
sir mujhe ppptp main 4 wan ki load balancing ki script chahiye for example 4 dsl jin ka gateway same hai
LikeLike
Comment by umer — February 25, 2012 @ 3:28 PM
Dear Jhanzaib,
i am running mikrotik 5.11 hotspot but problem is that if customer use skype call then it disconnect after 5 to 10 mins.please help me
LikeLike
Comment by mubashir — February 27, 2012 @ 5:01 PM
That’s unusual.
Are you limiting per user connection in firewall ?
Post your mikrotik config,
LikeLike
Comment by Syed Jahanzaib / Pinochio~:) — February 27, 2012 @ 5:18 PM
hi i have RB1100 AH and i wanted to loadbalance 4xE1 lines is your scrip applicable? im not use to scrip can i configure this using webfig (User Interface). I want to activate ehter6 as LAN output and Ether7-10 as WAN input.
LikeLike
Comment by Raymond — February 28, 2012 @ 11:34 AM
It doesn’t matter what kind of WAN links you are using. PCC can work with all of them.
LikeLike
Comment by Syed Jahanzaib / Pinochio~:) — February 29, 2012 @ 12:08 PM
hey,
i have 3 adsl lines working together with the PCC but i would like to know if there any way i could make a Specific user uses only the data from wan3 for example not the 3 lines , im trying to do this so i don’t have ping conflicts while playing online games . thanks
LikeLike
Comment by Aladdin — February 29, 2012 @ 3:19 AM
Create an address list, and exempt this list from pcc rules.
Also then you can mark packets for specific address list, and then in route define route for these marked packets to go through your desired wan link.
LikeLike
Comment by Syed Jahanzaib / Pinochio~:) — February 29, 2012 @ 12:05 PM
Slam bhai! main 3wan loadblancing ke hai lakin wo kam he nai ker rahi main ne apki config post ker di hai plzzz help me to correct it ….
/ip address
add address=192.168.125.2/24 network=192.168.125.0 broadcast=192.168.125.255 interface=Local
add address=192.168.1.2/24 network=192.168.1.0 broadcast=192.168.1.255 interface=WAN1
add address=192.168.2.2/24 network=192.168.2.0 broadcast=192.168.2.255 interface=WAN2
add address=192.168.3.2/24 network=192.168.3.0 broadcast=192.168.3.255 interface=WAN3
/ip firewall mangle
add chain=input in-interface=WAN1 action=mark-connection new-connection-mark=WAN1_conn
add chain=input in-interface=WAN2 action=mark-connection new-connection-mark=WAN2_conn
add chain=input in-interface=WAN3 action=mark-connection new-connection-mark=WAN3_conn
add chain=output connection-mark=WAN1_conn action=mark-routing new-routing-mark=to_WAN1
add chain=output connection-mark=WAN2_conn action=mark-routing new-routing-mark=to_WAN2
add chain=output connection-mark=WAN3_conn action=mark-routing new-routing-mark=to_WAN3
add chain=prerouting dst-address=192.168.1.0/24 action=accept in-interface=Local
add chain=prerouting dst-address=192.168.2.0/24 action=accept in-interface=Local
add chain=prerouting dst-address=192.168.3.0/24 action=accept in-interface=Local
add chain=prerouting dst-address-type=!local hotspot=auth in-interface=Local per-connection-classifier=both-addresses-and-ports:3/0 action=mark-connection new-connection-mark=WAN1_conn passthrough=yes
add chain=prerouting dst-address-type=!local hotspot=auth in-interface=Local per-connection-classifier=both-addresses-and-ports:3/1 action=mark-connection new-connection-mark=WAN2_conn passthrough=yes
add chain=prerouting dst-address-type=!local hotspot=auth in-interface=Local per-connection-classifier=both-addresses-and-ports:3/2 action=mark-connection new-connection-mark=WAN3_conn passthrough=yes
add chain=prerouting connection-mark=WAN1_conn in-interface=Local action=mark-routing new-routing-mark=to_WAN1
add chain=prerouting connection-mark=WAN2_conn in-interface=Local action=mark-routing new-routing-mark=to_WAN2
add chain=prerouting connection-mark=WAN3_conn in-interface=Local action=mark-routing new-routing-mark=to_WAN3
/ip route
add dst-address=0.0.0.0/0 gateway=192.168.1.1 routing-mark=to_WAN1 check-gateway=ping
add dst-address=0.0.0.0/0 gateway=192.168.2.1 routing-mark=to_WAN2 check-gateway=ping
add dst-address=0.0.0.0/0 gateway=192.168.3.1 routing-mark=to_WAN3 check-gateway=ping
add dst-address=0.0.0.0/0 gateway=192.168.1.1 distance=1 check-gateway=ping
add dst-address=0.0.0.0/0 gateway=192.168.2.1 distance=2 check-gateway=ping
add dst-address=0.0.0.0/0 gateway=192.168.3.1 distance=3 check-gateway=ping
/ip firewall nat
add chain=srcnat out-interface=WAN1 action=masquerade
add chain=srcnat out-interface=WAN2 action=masquerade
add chain=srcnat out-interface=WAN3 action=masquerade
LikeLike
Comment by smn4all — March 3, 2012 @ 10:49 AM
AOA sir i am running a small ISP. i have started HFS server. i want that all(512kb, 1mb, 2mb) clients get access to HFS server with unlimited speed.
how can we do this. ?
LikeLiked by 1 person
Comment by Suleman — March 6, 2012 @ 10:53 PM
LikeLike
Comment by Syed Jahanzaib / Pinochio~:) — March 7, 2012 @ 9:51 AM
hi, i have a complecated network in my office. i have RB750 and PC mikrotik, can u give me suggest mikrotik setting. i’ll appreciate ur help !
LikeLike
Comment by Ahmad Zulfa — March 15, 2012 @ 6:36 AM
:s unable to understand what kind of suggestion you are looking for ?
LikeLike
Comment by Syed Jahanzaib / Pinochio~:) — March 15, 2012 @ 9:55 AM
sir i have 2 Wan and 2 Lan i want that Wan1 route to Lan1 and Wan2 route to Lan2 plz sir post script
LikeLike
Comment by Owais Malik — March 15, 2012 @ 8:42 PM
create nat/masquerading rules for both interfaces , in out interface, select appropriate WAN link.
so if a use connected with lan1, he will be routed to WAN1 auto.
or read this
LikeLike
Comment by Syed Jahanzaib / Pinochio~:) — March 16, 2012 @ 2:18 PM
Thanks a lot Jahanzaib Bhai
LikeLike
Comment by Owais Malik — March 16, 2012 @ 7:06 PM
Sir yay ptcl nay jo 300 gb bandwidth limit lagae hai, Is ka koi solution hai…
LikeLike
Comment by Owais Malik — March 16, 2012 @ 7:08 PM
sir licence kahan say purchase hota hai or yay kitnay ka hota hai
LikeLike
Comment by Owais Malik — March 16, 2012 @ 7:09 PM
You can get license details from
Mr. Shakeel / Aqeel
Dreams Network Technology
Karachi , Pakistan
Contact No: +923132118237 , +923332828526
Email: info@dreamnw.com
LikeLike
Comment by Syed Jahanzaib / Pinochio~:) — March 17, 2012 @ 10:26 PM
Dear Sir,
I hope that you will fine and ok.I want to further subnet my /28 public ip pool in mikrotik. I have five interfaces in mikrotik and i want subent into two /29 subnets.One pool is for
my WAN and the 2nd pool to provide a customer.I shall be very thankful to you.
LikeLike
Comment by Muhammad kazim — March 22, 2012 @ 3:03 PM
using a subnet calculator for instance, http://www.subnet-calculator.com/ you can divide your ip’s quite easily.
for instance, RB750 using port 2 (wan) and 3-5(Cust). RB750G one can use 1(Wan) and 2-5(Cust).
(RB750G example) Then depending on one’s setup, make 2 master, 3,4,5 slaves to port 2. Then setup dhcp to port 2 with clients /29. pretty much the default RB75X setup but with your IP’s not mikrotiks default ones. Perhaps even 1:1 nat can be added if needed, unlikely but an option.
Then add the ips to port 1 as its /29 and your done. You’ll need to have a gateway, ie 10.2.0.1/29 then 10.2.0.2/29 will be port 1’s (wan) ip. mikrotik dns will also be your gateway IP. Dont forget to have nat with mascerading.
Hope it helps, but as always, its what the customer wants and usually many ways to achieve the same goals.
Lastly, awesome site, always enjoy the insights to be had here.
LikeLike
Comment by Nitrious — March 23, 2012 @ 11:36 PM
Thaanks A lot sir
LikeLike
Comment by muhammad kazim — March 24, 2012 @ 12:21 PM
salam jahanzaib bhai,,i hope ap bil kul thek thak hon gay…jahanzaib bhai mujhy ap sy thoei help chaye thi..k mikrotik main VPN kis trha bna sktay hain ..main hotspot use kerta hn…kia vpn k liye static ip ka hna zaorori hai…?i mean how to creat vpn for monitring our network thrw winbox…
LikeLike
Comment by ALi haider — March 26, 2012 @ 6:15 PM
Hmm actually you dont VPN just to monitor your Mikrotik BOX, you can use simple port forward rule for it, and Yes you will be needing static IP for it to connect remotely, (There is a service called DYNADNS but I dunt have any idea about it, in this service you dont need static ip, domain name will be binded with the link and you will connect to it using dns name)
on the other hand, if you want to connect to your network from outside world to monitor the whole network, access any pc/server on your lan from outside world, then YES you will be needing VPN Server, which can be configured on Mikrotik.
LikeLike
Comment by Syed Jahanzaib / Pinochio~:) — March 27, 2012 @ 10:37 PM
i mean kisi b dsl sy hm jst apna vpn host name winbox y enter kerain aur winbox hmain hmare server pay lay jaye…plzzz help me i ll b very thnkfull to u…
LikeLike
Comment by ALi haider — March 26, 2012 @ 6:17 PM
Please rephrase your question in English.
LikeLike
Comment by Syed Jahanzaib / Pinochio~:) — March 27, 2012 @ 10:35 PM
Asalam o alikum
Jahanzib bhai i am Najam from karachi,pakistan i am using MICROTIK RB750GL and i have 3 ADSL and i want to configure Router lan port in to load balancing can you help me somebuddy told me about script so what kind of script that and how to configure my email address is frankenstene@hotmail.com and my cell number is +92 321 2346 223 .
LikeLike
Comment by Najam — March 27, 2012 @ 1:28 AM
The above script does the same that you want to achieve. Just read them thoroughly.
Nobody will do it for you, You have to earn it
Read, Read, Read , Practice, Practice and Practice , and you wins 🙂
There is no elevator for success, you have to use Stairs , step by step 🙂
LikeLike
Comment by Syed Jahanzaib / Pinochio~:) — March 27, 2012 @ 10:33 PM
Hello,
First, thank you for sharing such great info and tutorials!
Next, I got a question regarding my scenario:
I have three WANs where each of them has the same IP of 10.0.0.2 because until now I have been using them by connecting only WAN to the main switch physically, if that connection was down I just unplugged one CAT5 cable and plugged the other one, this is why all three WANs have same IP 10.0.0.2 (so I don’t need to reconfigure all computers IPs every time I unplug provider)
What would be the necessary changes to your script if my addresses are the same? I can get up to here so far:
add dst-address=0.0.0.0/0 gateway=10.0.0.2 routing-mark=to_WAN1 check-gateway=ping
add dst-address=0.0.0.0/0 gateway=10.0.0.2 routing-mark=to_WAN2 check-gateway=ping
add dst-address=0.0.0.0/0 gateway=10.0.0.2 routing-mark=to_WAN3 check-gateway=ping
add dst-address=0.0.0.0/0 gateway=10.0.0.2 routing-mark=to_WAN4 check-gateway=ping
Thanks for your help and your time…
LikeLike
Comment by gereqi — March 27, 2012 @ 2:08 PM
You need different subnet ip’s / gateway in order to use PCC
LikeLike
Comment by Syed Jahanzaib / Pinochio~:) — March 27, 2012 @ 10:29 PM
Thanks a lot
it works for me
I have used in a Vmware machine
LikeLike
Comment by masud — March 29, 2012 @ 1:45 AM
Greetings, I wonder my settings for the static routing + 4wan loadbalancing to two hotspot network, the result of the modifications you have the ‘right guns’ .. We are input, thank you
Salam-Indonesia-Amirudin
/ip firewall mangle
add action=mark-connection chain=input comment=New_inbound_connection_wan connection-state=new disabled=no in-interface=vlan3-id101-wintel new-connection-mark=wan1_in_conn passthrough=yes
add action=mark-connection chain=input connection-state=new disabled=no in-interface=wan2-speedy-3mb new-connection-mark=wan2_in_conn passthrough=yes
add action=mark-connection chain=input connection-state=new disabled=no in-interface=wan3-speedy-2mb new-connection-mark=wan3_in_conn passthrough=yes
add action=mark-connection chain=input connection-state=new disabled=no in-interface=wan4-speedy-2mb new-connection-mark=wan4_in_conn passthrough=yes
add action=mark-connection chain=input comment=Established_inbound_connection_wan connection-state=established disabled=no in-interface=vlan3-id101-wintel new-connection-mark=wan1_in_conn passthrough=yes
add action=mark-connection chain=input connection-state=established disabled=no in-interface=wan2-speedy-3mb new-connection-mark=wan2_in_conn passthrough=yes
add action=mark-connection chain=input connection-state=established disabled=no in-interface=wan3-speedy-2mb new-connection-mark=wan3_in_conn passthrough=yes
add action=mark-connection chain=input connection-state=established disabled=no in-interface=wan4-speedy-2mb new-connection-mark=wan4_in_conn passthrough=yes
add action=mark-connection chain=input comment=Related_inbound_connection_wan connection-state=related disabled=no in-interface=vlan3-id101-wintel new-connection-mark=wan1_in_conn passthrough=yes
add action=mark-connection chain=input connection-state=related disabled=no in-interface=wan2-speedy-3mb new-connection-mark=wan2_in_conn passthrough=yes
add action=mark-connection chain=input connection-state=related disabled=no in-interface=wan3-speedy-2mb new-connection-mark=wan3_in_conn passthrough=yes
add action=mark-connection chain=input connection-state=related disabled=no in-interface=wan4-speedy-2mb new-connection-mark=wan4_in_conn passthrough=yes
add action=mark-routing chain=output comment=Mark-new-inbound-route-static-wan connection-mark=wan1_in_conn disabled=no new-routing-mark=static-wan1 passthrough=no
add action=mark-routing chain=output connection-mark=wan2_in_conn disabled=no new-routing-mark=static-wan2 passthrough=no
add action=mark-routing chain=output connection-mark=wan3_in_conn disabled=no new-routing-mark=static-wan3 passthrough=no
add action=mark-routing chain=output connection-mark=wan4_in_conn disabled=no new-routing-mark=static-wan4 passthrough=no
add action=mark-connection chain=prerouting comment=”Mark-traffic-that-isn’t-local-with-PCC-jamsostek” connection-state=new disabled=no dst-address-type=!local hotspot=auth in-interface=eoip-tunnel1-id100-Hotspot-Jamsostek new-connection-mark=wan1_pcc_conn passthrough=yes per-connection-classifier=both-addresses-and-ports:4/0
add action=mark-connection chain=prerouting connection-state=new disabled=no dst-address-type=!local hotspot=auth in-interface=eoip-tunnel1-id100-Hotspot-Jamsostek new-connection-mark=wan1_pcc_conn passthrough=yes per-connection-classifier=both-addresses-and-ports:4/1
add action=mark-connection chain=prerouting connection-state=new disabled=no dst-address-type=!local hotspot=auth in-interface=eoip-tunnel1-id100-Hotspot-Jamsostek new-connection-mark=wan2_pcc_conn passthrough=yes per-connection-classifier=both-addresses-and-ports:4/2
add action=mark-connection chain=prerouting connection-state=new disabled=no dst-address-type=!local hotspot=auth in-interface=eoip-tunnel1-id100-Hotspot-Jamsostek new-connection-mark=wan3_pcc_conn passthrough=yes per-connection-classifier=both-addresses-and-ports:4/3
add action=mark-connection chain=prerouting connection-state=new disabled=no dst-address-type=!local hotspot=auth in-interface=eoip-tunnel1-id100-Hotspot-Jamsostek new-connection-mark=wan4_pcc_conn passthrough=yes per-connection-classifier=both-addresses-and-ports:4/4
add action=mark-connection chain=prerouting comment=”Mark Established Traffic That Isn’t Local with PCC-jamsostek” connection-state=established disabled=no dst-address-type=!local hotspot=auth in-interface=eoip-tunnel1-id100-Hotspot-Jamsostek new-connection-mark=wan1_pcc_conn passthrough=yes per-connection-classifier=both-addresses-and-ports:4/0
add action=mark-connection chain=prerouting connection-state=established disabled=no dst-address-type=!local hotspot=auth in-interface=eoip-tunnel1-id100-Hotspot-Jamsostek new-connection-mark=wan1_pcc_conn passthrough=yes per-connection-classifier=both-addresses-and-ports:4/1
add action=mark-connection chain=prerouting connection-state=established disabled=no dst-address-type=!local hotspot=auth in-interface=eoip-tunnel1-id100-Hotspot-Jamsostek new-connection-mark=wan2_pcc_conn passthrough=yes per-connection-classifier=both-addresses-and-ports:4/2
add action=mark-connection chain=prerouting connection-state=established disabled=no dst-address-type=!local hotspot=auth in-interface=eoip-tunnel1-id100-Hotspot-Jamsostek new-connection-mark=wan3_pcc_conn passthrough=yes per-connection-classifier=both-addresses-and-ports:4/3
add action=mark-connection chain=prerouting connection-state=established disabled=no dst-address-type=!local hotspot=auth in-interface=eoip-tunnel1-id100-Hotspot-Jamsostek new-connection-mark=wan4_pcc_conn passthrough=yes per-connection-classifier=both-addresses-and-ports:4/4
add action=mark-connection chain=prerouting comment=”Mark related traffic thatisn’t local with PCC – Jamsostek” connection-state=related disabled=no dst-address-type=!local hotspot=auth in-interface=eoip-tunnel1-id100-Hotspot-Jamsostek new-connection-mark=wan1_pcc_conn passthrough=yes per-connection-classifier=both-addresses-and-ports:4/0
add action=mark-connection chain=prerouting connection-state=related disabled=no dst-address-type=!local hotspot=auth in-interface=eoip-tunnel1-id100-Hotspot-Jamsostek new-connection-mark=wan1_pcc_conn passthrough=yes per-connection-classifier=both-addresses-and-ports:4/1
add action=mark-connection chain=prerouting connection-state=related disabled=no dst-address-type=!local hotspot=auth in-interface=eoip-tunnel1-id100-Hotspot-Jamsostek new-connection-mark=wan2_pcc_conn passthrough=yes per-connection-classifier=both-addresses-and-ports:4/2
add action=mark-connection chain=prerouting connection-state=related disabled=no dst-address-type=!local hotspot=auth in-interface=eoip-tunnel1-id100-Hotspot-Jamsostek new-connection-mark=wan3_pcc_conn passthrough=yes per-connection-classifier=both-addresses-and-ports:4/3
add action=mark-connection chain=prerouting connection-state=related disabled=no dst-address-type=!local hotspot=auth in-interface=eoip-tunnel1-id100-Hotspot-Jamsostek new-connection-mark=wan4_pcc_conn passthrough=yes per-connection-classifier=both-addresses-and-ports:4/4
add action=mark-routing chain=prerouting comment=MarkroutingforPCCmark-option-JAMSOSTEK connection-mark=wan1_pcc_conn disabled=no new-routing-mark=wan1 passthrough=yes
add action=mark-routing chain=prerouting connection-mark=wan2_pcc_conn disabled=no new-routing-mark=wan2 passthrough=yes
add action=mark-routing chain=prerouting connection-mark=wan3_pcc_conn disabled=no new-routing-mark=wan3 passthrough=yes
add action=mark-routing chain=prerouting connection-mark=wan4_pcc_conn disabled=no new-routing-mark=wan4 passthrough=yes
add action=mark-connection chain=prerouting comment=”—-Mark-traffic-that-isn’t-local-with-PCC-mark-rand-(2-possibilities)-option-bida” connection-state=new disabled=no dst-address-type=!local hotspot=auth in-interface=eth5.hotspot-bida new-connection-mark=wan1_pcc_connA passthrough=yes per-connection-classifier=both-addresses-and-ports:4/0
add action=mark-connection chain=prerouting connection-state=new disabled=no dst-address-type=!local hotspot=auth in-interface=eth5.hotspot-bida new-connection-mark=wan1_pcc_connA passthrough=yes per-connection-classifier=both-addresses-and-ports:4/1
add action=mark-connection chain=prerouting connection-state=new disabled=no dst-address-type=!local hotspot=auth in-interface=eth5.hotspot-bida new-connection-mark=wan2_pcc_connB passthrough=yes per-connection-classifier=both-addresses-and-ports:4/2
add action=mark-connection chain=prerouting connection-state=new disabled=no dst-address-type=!local hotspot=auth in-interface=eth5.hotspot-bida new-connection-mark=wan3_pcc_connC passthrough=yes per-connection-classifier=both-addresses-and-ports:4/3
add action=mark-connection chain=prerouting connection-state=new disabled=no dst-address-type=!local hotspot=auth in-interface=eth5.hotspot-bida new-connection-mark=wan4_pcc_connD passthrough=yes per-connection-classifier=both-addresses-and-ports:4/4
add action=mark-connection chain=prerouting comment=”MarkestablishedTrafficThatIsn’tLocalwithPCCmarkrand(2possibilities)-option-bida” connection-state=established disabled=no dst-address-type=!local hotspot=auth in-interface=eth5.hotspot-bida new-connection-mark=wan1_pcc_connA passthrough=yes per-connection-classifier=both-addresses-and-ports:4/0
add action=mark-connection chain=prerouting connection-state=established disabled=no dst-address-type=!local hotspot=auth in-interface=eth5.hotspot-bida new-connection-mark=wan1_pcc_connA passthrough=yes per-connection-classifier=both-addresses-and-ports:4/1
add action=mark-connection chain=prerouting connection-state=established disabled=no dst-address-type=!local hotspot=auth in-interface=eth5.hotspot-bida new-connection-mark=wan2_pcc_connB passthrough=yes per-connection-classifier=both-addresses-and-ports:4/2
add action=mark-connection chain=prerouting connection-state=established disabled=no dst-address-type=!local hotspot=auth in-interface=eth5.hotspot-bida new-connection-mark=wan3_pcc_connC passthrough=yes per-connection-classifier=both-addresses-and-ports:4/3
add action=mark-connection chain=prerouting connection-state=established disabled=no dst-address-type=!local hotspot=auth in-interface=eth5.hotspot-bida new-connection-mark=wan4_pcc_connD passthrough=yes per-connection-classifier=both-addresses-and-ports:4/4
add action=mark-connection chain=prerouting comment=”Markrelatedtrafficthatisn’tlocalwithPCCmarkrand(2possibilities)-option1″ connection-state=related disabled=no dst-address-type=!local hotspot=auth in-interface=eth5.hotspot-bida new-connection-mark=wan1_pcc_connA passthrough=yes per-connection-classifier=both-addresses-and-ports:4/0
add action=mark-connection chain=prerouting connection-state=related disabled=no dst-address-type=!local hotspot=auth in-interface=eth5.hotspot-bida new-connection-mark=wan1_pcc_connA passthrough=yes per-connection-classifier=both-addresses-and-ports:4/1
add action=mark-connection chain=prerouting connection-state=related disabled=no dst-address-type=!local hotspot=auth in-interface=eth5.hotspot-bida new-connection-mark=wan2_pcc_connB passthrough=yes per-connection-classifier=both-addresses-and-ports:4/2
add action=mark-connection chain=prerouting connection-state=related disabled=no dst-address-type=!local hotspot=auth in-interface=eth5.hotspot-bida new-connection-mark=wan3_pcc_connC passthrough=yes per-connection-classifier=both-addresses-and-ports:4/3
add action=mark-connection chain=prerouting connection-state=related disabled=no dst-address-type=!local hotspot=auth in-interface=eth5.hotspot-bida new-connection-mark=wan4_pcc_connD passthrough=yes per-connection-classifier=both-addresses-and-ports:4/4
add action=mark-routing chain=prerouting comment=MarkroutingforPCCmark-option-BIDA connection-mark=wan1_pcc_connA disabled=no new-routing-mark=wan1 passthrough=yes
add action=mark-routing chain=prerouting connection-mark=wan2_pcc_connB disabled=no new-routing-mark=wan2 passthrough=yes
add action=mark-routing chain=prerouting connection-mark=wan2_pcc_connC disabled=no new-routing-mark=wan2 passthrough=yes
add action=mark-routing chain=prerouting connection-mark=wan2_pcc_connD disabled=no new-routing-mark=wan2 passthrough=yes
/ip route
add check-gateway=ping comment=StaticRoute-WAN disabled=no distance=1 dst-address=0.0.0.0/0 gateway=vlan3-id101-wintel routing-mark=static-wan1 scope=30 target-scope=10
add check-gateway=ping disabled=no distance=1 dst-address=0.0.0.0/0 gateway=wan2-speedy-3mb routing-mark=static-wan2 scope=30 target-scope=10
add check-gateway=ping disabled=no distance=1 dst-address=0.0.0.0/0 gateway=wan3-speedy-2mb routing-mark=static-wan3 scope=30 target-scope=10
add check-gateway=ping disabled=no distance=1 dst-address=0.0.0.0/0 gateway=wan4-speedy-2mb routing-mark=static-wan4 scope=30 target-scope=10
add check-gateway=arp disabled=no distance=1 dst-address=0.0.0.0/0 gateway=vlan3-id101-wintel routing-mark=wan1 scope=30 target-scope=10
add check-gateway=arp disabled=no distance=2 dst-address=0.0.0.0/0 gateway=wan2-speedy-3mb routing-mark=wan1 scope=30 target-scope=10
add check-gateway=arp disabled=no distance=3 dst-address=0.0.0.0/0 gateway=wan3-speedy-2mb routing-mark=wan1 scope=30 target-scope=10
add check-gateway=arp comment=WAN1-Distance1 disabled=no distance=4 dst-address=0.0.0.0/0 gateway=wan4-speedy-2mb routing-mark=wan1 scope=30 target-scope=10
add check-gateway=arp disabled=no distance=1 dst-address=0.0.0.0/0 gateway=wan2-speedy-3mb routing-mark=wan2 scope=30 target-scope=10
add check-gateway=arp disabled=no distance=2 dst-address=0.0.0.0/0 gateway=vlan3-id101-wintel routing-mark=wan2 scope=30 target-scope=10
add check-gateway=arp disabled=no distance=3 dst-address=0.0.0.0/0 gateway=wan3-speedy-2mb routing-mark=wan2 scope=30 target-scope=10
add check-gateway=arp comment=WAN2-Distance1 disabled=no distance=4 dst-address=0.0.0.0/0 gateway=wan4-speedy-2mb routing-mark=wan2 scope=30 target-scope=10
add check-gateway=arp disabled=no distance=1 dst-address=0.0.0.0/0 gateway=wan3-speedy-2mb routing-mark=wan3 scope=30 target-scope=10
add check-gateway=arp comment=WAN3-Distance1 disabled=no distance=2 dst-address=0.0.0.0/0 gateway=wan4-speedy-2mb routing-mark=wan3 scope=30 target-scope=10
add check-gateway=arp disabled=no distance=3 dst-address=0.0.0.0/0 gateway=vlan3-id101-wintel routing-mark=wan3 scope=30 target-scope=10
add check-gateway=arp disabled=no distance=4 dst-address=0.0.0.0/0 gateway=wan2-speedy-3mb routing-mark=wan3 scope=30 target-scope=10
add check-gateway=arp comment=WAN4-Distance1 disabled=no distance=1 dst-address=0.0.0.0/0 gateway=wan4-speedy-2mb routing-mark=wan4 scope=30 target-scope=10
add check-gateway=arp disabled=no distance=2 dst-address=0.0.0.0/0 gateway=vlan3-id101-wintel routing-mark=wan4 scope=30 target-scope=10
add check-gateway=arp disabled=no distance=3 dst-address=0.0.0.0/0 gateway=wan2-speedy-3mb routing-mark=wan4 scope=30 target-scope=10
add check-gateway=arp disabled=no distance=4 dst-address=0.0.0.0/0 gateway=wan3-speedy-2mb routing-mark=wan4 scope=30 target-scope=10
add check-gateway=ping disabled=no distance=1 dst-address=0.0.0.0/0 gateway=wan4-speedy-2mb routing-mark=link-youtube scope=30 target-scope=10
add check-gateway=ping comment=”WAN3 link for the NEWS WEB” disabled=no distance=1 dst-address=0.0.0.0/0 gateway=wan3-speedy-2mb routing-mark=link-news scope=30 target-scope=10
add disabled=no distance=120 dst-address=192.168.100.4/30 gateway=192.168.100.2 scope=30 target-scope=10
add comment=”load balancing the DNS requests” disabled=no distance=10 dst-address=202.87.248.1/32 gateway=119.2.68.213 pref-src=119.2.68.214 scope=30 target-scope=10
add disabled=no distance=10 dst-address=202.134.0.155/32 gateway=wan2-speedy-3mb,wan3-speedy-2mb,wan4-speedy-2mb scope=30 target-scope=10
add disabled=no distance=10 dst-address=203.130.193.74/32 gateway=wan2-speedy-3mb,wan3-speedy-2mb,wan4-speedy-2mb scope=30 target-scope=10
/ip route rule
add action=lookup disabled=no routing-mark=wan3 table=wan3
add action=lookup disabled=no routing-mark=wan4 table=wan4
add action=lookup disabled=no dst-address=74.125.236.100/32 table=link-youtube
add action=lookup disabled=no dst-address=74.125.236.105/32 table=link-youtube
add action=lookup disabled=no dst-address=74.125.236.111/32 table=link-youtube
add action=lookup disabled=no dst-address=202.134.0.0/16 table=link-youtube
add action=lookup disabled=no dst-address=208.117.0.0/16 table=link-youtube
add action=lookup disabled=no dst-address=208.65.0.0/16 table=link-youtube
add action=lookup comment=kompas disabled=no dst-address=202.146.4.100/32 table=link-news
add action=lookup comment=detik disabled=no dst-address=203.190.241.43/32 table=link-news
add action=lookup comment=detik disabled=no dst-address=203.190.241.44/32 table=link-news
add action=lookup comment=detik disabled=no dst-address=203.190.241.69/32 table=link-news
add action=lookup comment=detik disabled=no dst-address=203.190.242.69/32 table=link-news
add action=lookup comment=detik disabled=no dst-address=203.190.243.69/32 table=link-news
LikeLike
Comment by amirudin — March 30, 2012 @ 10:50 PM
Hallo ,Sellam Al.
i have one problem on my rb with 2 isp provider, download working fine but upload maximum its 768 kb/s ,but i have this speed :
Now where is problem .
ISP1 WLAN1 —-20mb/s download ,, upload 768 kb/s ether1
ISP2 WLAN2 —-50mb/s Download ,, upload 50mb/s ether2
Local ether3
Download the speedtest is ok 68-70 mb/s but the upload never goes more than 768 kb/s
which is used to upload the ISP1.
My configuration :
/ip address
add address=172.16.88.1/24 broadcast=172.16.88.255 comment=”” disabled=no interface=Local network=172.16.88.0
add address=10.10.10.188/24 broadcast=10.10.10.255 comment=”” disabled=no interface=WAN2 network=10.10.10.0
add address=10.0.20.105/24 broadcast=10.0.20.255 comment=”” disabled=no interface=WAN1 network=10.0.20.0
admin@MikroTik] > ip firewall mangle print
Flags: X – disabled, I – invalid, D – dynamic
0 chain=input action=mark-connection new-connection-mark=WAN1_conn passthrough=yes in-interface=WAN1
1 chain=input action=mark-connection new-connection-mark=WAN2_conn passthrough=yes in-interface=WAN2
2 chain=output action=mark-routing new-routing-mark=to_WAN1 passthrough=yes connection-mark=WAN1_conn
3 chain=output action=mark-routing new-routing-mark=to_WAN2 passthrough=yes connection-mark=WAN2_conn
4 chain=prerouting action=accept dst-address=10.0.20.0/24 in-interface=Local
5 chain=prerouting action=accept dst-address=10.10.10.0/24 in-interface=Local
6 ;;; 2/0 PCC
chain=prerouting action=mark-connection new-connection-mark=WAN1_conn passthrough=yes dst-address-type=!local in-interface=Local
per-connection-classifier=both-addresses-and-ports:2/0
7 ;;; 2/1 PCC
chain=prerouting action=mark-connection new-connection-mark=WAN2_conn passthrough=yes dst-address-type=!local in-interface=Local
per-connection-classifier=both-addresses-and-ports:2/1
8 chain=prerouting action=mark-routing new-routing-mark=to_WAN1 passthrough=yes in-interface=Local connection-mark=WAN1_conn
9 chain=prerouting action=mark-routing new-routing-mark=to_WAN2 passthrough=yes in-interface=Local connection-mark=WAN2_conn
/ ip route
0 A S dst-address=0.0.0.0/0 gateway=10.0.20.1 gateway-status=10.0.20.1 reachable WAN1 check-gateway=ping distance=1 scope=30 target-scope=10 routing-mark=to_WAN1
1 A S dst-address=0.0.0.0/0 gateway=10.10.10.1 gateway-status=10.10.10.1 reachable WAN2 check-gateway=ping distance=1 scope=30 target-scope=10 routing-mark=to_WAN2
2 A S dst-address=0.0.0.0/0 gateway=10.0.20.1 gateway-status=10.0.20.1 reachable WAN1 check-gateway=ping distance=1 scope=30 target-scope=10
3 S dst-address=0.0.0.0/0 gateway=10.10.10.1 gateway-status=10.10.10.1 reachable WAN2 check-gateway=ping distance=2 scope=30 target-scope=10
4 ADC dst-address=10.0.20.0/24 pref-src=10.0.20.105 gateway=WAN1 gateway-status=WAN1 reachable distance=0 scope=10
please help to finis my problem ..thanky
/ ip firewall nat
0 chain=srcnat action=masquerade out-interface=WAN1
1 chain=srcnat action=masquerade out-interface=WAN2
5 ADC dst-address=10.10.10.0/24 pref-src=10.10.10.188 gateway=WAN2 gateway-status=WAN2 reachable distance=0 scope=10
6 ADC dst-address=172.16.88.0/24 pref-src=172.16.88.1 gateway=Local gateway-status=Local reachable distance=0 scope=10
LikeLike
Comment by askopz — April 8, 2012 @ 5:22 AM
please reply my problem thx. a.s
LikeLike
Comment by askopz — April 14, 2012 @ 9:44 PM
please fix my probbb ….
LikeLike
Comment by askopz — April 21, 2012 @ 6:56 AM
Mikrotik merge download speed only…… upload speed take from default DSL wan….
LikeLike
Comment by smn4all — April 21, 2012 @ 1:16 PM
Syed, u ar a genius
LikeLike
Comment by JP — April 9, 2012 @ 5:12 PM
sir i am using RB750 and using your given load balancing which works great when i m using with hotspot but when i m using PPPOE server then my user can only use wan 1 please help out.
LikeLike
Comment by fizzi khan — April 14, 2012 @ 4:49 PM
Things are handled differently when it comes to PPPoE clients because pppoe client create there own interface on mikrtik after connected.
You can use the following method (designed to work PCC with PPPoE client)
A quick search on Google , is the best way to dig thing quickly,
LikeLike
Comment by Syed Jahanzaib / Pinochio~:) — April 14, 2012 @ 7:40 PM
ASSLAM O ALIKUM WAA RAHMATULLAH.
Sir i have one more question abt RB750. Sir can we use this small mikrotik board for 200 users ? is it will work perfect including load balancing and pppoe and hotspot both users ? achully i m running both services at same time. your quick response is really appreciated.
LikeLike
Comment by fizzi khan — April 14, 2012 @ 10:19 PM
please you have any results for 2 isp , 2 isp both download one isp only upload
LikeLike
Comment by askopz — April 14, 2012 @ 11:26 PM
ASSLAM O ALIKUM
jahanzaib sir i have applied mikrotik-4-wan-load-balancing-using-pcc-with-pppoe-server- PPPOE is working perfectly but now my hotspot on same device isn’t work first of all the client lan is not geting default gateway so hotspot page isn’t open please help me how i can edit or change some rules for hotspot ?
Jaza kumula Khairan.
LikeLike
Comment by fizzi khan — April 15, 2012 @ 2:10 AM
Dear Bro. how can we use User Manager and manage users and their accounting on v3.3 with level4 license. if their some solution please tell me how can i do it.
LikeLike
Comment by Junaid — April 16, 2012 @ 3:06 PM
Assalamu alikum Bro Syed Jahanzaid. This is Nahid from Bangladesh. Thanks a lot for your sharing knowledge. Now I can marge bandwidth with mikrotik router. I have learn everything from your post. But now I am facing new problem. I have two Internet connection where Gateway are same Like : 192.168.3.1 another one also like this. So my load Blanching not working properly. What I should do in this situation. Please give me necessary advice. May Allah always keep you well…..
LikeLike
Comment by GSB NAHID — April 19, 2012 @ 11:10 AM
You must have different Gateways for Proper load balancing.
One workaround is to add any cheap router like tplink or any on one link, so you will get different gateway. For example
Mikrotik PCC
>> WAN1 ==> DSL1 >>> INTERNET
>> WAN2 ==> Router >> DSL2 >> INTERNET
This way your pcc will work.
LikeLike
Comment by Syed Jahanzaib / Pinochio~:) — April 19, 2012 @ 1:02 PM
Hi,
The way I did load balancing/aggregation with pcc was to simply put the adsl account on the adsl modem, and give each modem a different ip on a different subnet. Each of these is then put on their own ethernet on the mikrotik.
It doesnt work for me if you use pppoe client on the mikrotik directly and the adsl modem in bridge mode.
so the following works nicely (IPs included for example purposes, can also use /30 subnets)
>>ETHER1 >> DSL1 >> INTERNET
10.1.0.2/29 10.1.0.1/29
>>ETHER2 >> DSL2>>INTERNET
10.1.0.9/29 10.1.0.10/29
Then 8.8.8.8 for DNS.
LikeLike
Comment by Nitrious — April 21, 2012 @ 4:25 PM
Assalamu alikum Bro…Thanks a lot for your replay. Now my pcc working excellent.
LikeLike
Comment by GSB NAHID — April 23, 2012 @ 9:28 AM
Assalamu alikum Syed Bro.. This is Nahid. I am facing a new problem in Mikrotik Queues. I am using ip 192.168.3.254 to 253>252 …..Like this for user. And using Simple Queues for user Bandwidth control individually like 512KBs or 256KBs . After ip 192.168.3.200 , I want to control all ip in one Queue like 265KBs. How i will make this queues. I am waiting for your replay..
LikeLike
Comment by GSB NAHID — April 24, 2012 @ 9:26 AM
Use PCQ.
Use the below method / logic and modify it as per your requirement.
http://wiki.mikrotik.com/wiki/Cable_setup
LikeLike
Comment by Syed Jahanzaib / Pinochio~:) — April 25, 2012 @ 10:59 AM
Bro My main problem is…I am using Mac Binding and Static ip for users so that anyone cant get connection without my permission. But someone taking access without mac and using any ip after my Queue list and getting full Bandwidth speed. I can just watch him with Torch function. Please help me how can I stop his access.
LikeLike
Comment by GSB NAHID — April 24, 2012 @ 9:52 AM
There must be some security weakness in your firewall.
I recommend you to move on to pppoe base authentication and use ip less scenario.
This way you will be saved from many problems and security weakness.
LikeLike
Comment by Syed Jahanzaib / Pinochio~:) — April 25, 2012 @ 11:03 AM
Hallo ,Sellam Al.
i have one problem on my rb with 2 isp provider, download working fine but upload maximum its 768 kb/s ,but i have this speed :
Now where is problem .
ISP1 WLAN1 —-20mb/s download ,, upload 768 kb/s ether1
ISP2 WLAN2 —-50mb/s Download ,, upload 50mb/s ether2
Local ether3
Download the speedtest is ok 68-70 mb/s but the upload never goes more than 768 kb/s
which is used to upload the ISP1.
My configuration :
/ip address
add address=172.16.88.1/24 broadcast=172.16.88.255 comment=”” disabled=no interface=Local network=172.16.88.0
add address=10.10.10.188/24 broadcast=10.10.10.255 comment=”” disabled=no interface=WAN2 network=10.10.10.0
add address=10.0.20.105/24 broadcast=10.0.20.255 comment=”” disabled=no interface=WAN1 network=10.0.20.0
admin@MikroTik] > ip firewall mangle print
Flags: X – disabled, I – invalid, D – dynamic
0 chain=input action=mark-connection new-connection-mark=WAN1_conn passthrough=yes in-interface=WAN1
1 chain=input action=mark-connection new-connection-mark=WAN2_conn passthrough=yes in-interface=WAN2
2 chain=output action=mark-routing new-routing-mark=to_WAN1 passthrough=yes connection-mark=WAN1_conn
3 chain=output action=mark-routing new-routing-mark=to_WAN2 passthrough=yes connection-mark=WAN2_conn
4 chain=prerouting action=accept dst-address=10.0.20.0/24 in-interface=Local
5 chain=prerouting action=accept dst-address=10.10.10.0/24 in-interface=Local
6 ;;; 2/0 PCC
chain=prerouting action=mark-connection new-connection-mark=WAN1_conn passthrough=yes dst-address-type=!local in-interface=Local
per-connection-classifier=both-addresses-and-ports:2/0
7 ;;; 2/1 PCC
chain=prerouting action=mark-connection new-connection-mark=WAN2_conn passthrough=yes dst-address-type=!local in-interface=Local
per-connection-classifier=both-addresses-and-ports:2/1
8 chain=prerouting action=mark-routing new-routing-mark=to_WAN1 passthrough=yes in-interface=Local connection-mark=WAN1_conn
9 chain=prerouting action=mark-routing new-routing-mark=to_WAN2 passthrough=yes in-interface=Local connection-mark=WAN2_conn
/ ip route
0 A S dst-address=0.0.0.0/0 gateway=10.0.20.1 gateway-status=10.0.20.1 reachable WAN1 check-gateway=ping distance=1 scope=30 target-scope=10 routing-mark=to_WAN1
1 A S dst-address=0.0.0.0/0 gateway=10.10.10.1 gateway-status=10.10.10.1 reachable WAN2 check-gateway=ping distance=1 scope=30 target-scope=10 routing-mark=to_WAN2
2 A S dst-address=0.0.0.0/0 gateway=10.0.20.1 gateway-status=10.0.20.1 reachable WAN1 check-gateway=ping distance=1 scope=30 target-scope=10
3 S dst-address=0.0.0.0/0 gateway=10.10.10.1 gateway-status=10.10.10.1 reachable WAN2 check-gateway=ping distance=2 scope=30 target-scope=10
4 ADC dst-address=10.0.20.0/24 pref-src=10.0.20.105 gateway=WAN1 gateway-status=WAN1 reachable distance=0 scope=10
please help to finis my problem ..thanky
/ ip firewall nat
0 chain=srcnat action=masquerade out-interface=WAN1
1 chain=srcnat action=masquerade out-interface=WAN2
5 ADC dst-address=10.10.10.0/24 pref-src=10.10.10.188 gateway=WAN2 gateway-status=WAN2 reachable distance=0 scope=10
6 ADC dst-address=172.16.88.0/24 pref-src=172.16.88.1 gateway=Local gateway-status=Local reachable distance=0 scope=10
LikeLike
Comment by askopz — April 25, 2012 @ 2:11 PM
Brother! Mikrotik is not merge multi WAN upload speed . this only merge Download Speed. Understand it , don`t try more and more
LikeLike
Comment by smn4all — April 25, 2012 @ 3:15 PM
Dear Jahanzaib Bhai, My pcc with pppoe server is working fine with 2 WANS. I want to enable proxy as well what to do as pcc is not supporting the webproxy. Kindly guide with anyother solution if there it is
thanks
LikeLike
Comment by khalid Iqbal — April 27, 2012 @ 11:13 PM
Its better to use external proxy like squid or other, rather then fighting with Mikrotik’s internal web proxy to make it work.
If you still want it, search the mikrotik forum, there are lot of posts regarding this issue and its solution.
LikeLike
Comment by Syed Jahanzaib / Pinochio~:) — April 28, 2012 @ 4:19 PM
Dear Syed Jahanzaib
I have RB1100 and i want create Load balancer with 8 WAN input with pcc, and each bandwidth wan not same, please help me, thanks alot for your help
LikeLike
Comment by yovi — April 28, 2012 @ 2:27 AM
/ ip address
add address=192.168.0.1/24 network=192.168.0.0 broadcast=192.168.0.255 interface=LAN
add address=10.111.0.2/24 network=10.111.0.0 broadcast=10.111.0.255 interface=ISP1
add address=10.112.0.2/24 network=10.112.0.0 broadcast=10.112.0.255 interface=ISP2
/ ip firewall mangle
add chain=prerouting dst-address=10.111.0.0/24 action=accept in-interface=LAN
add chain=prerouting dst-address=10.112.0.0/24 action=accept in-interface=LAN
add chain=prerouting in-interface=ISP1 connection-mark=no-mark action=mark-connection \
new-connection-mark=ISP1_conn
add chain=prerouting in-interface=ISP2 connection-mark=no-mark action=mark-connection \
new-connection-mark=ISP2_conn
add chain=prerouting in-interface=LAN connection-mark=no-mark dst-address-type=!local \
per-connection-classifier=both-addresses:2/0 action=mark-connection new-connection-mark=ISP1_conn
add chain=prerouting in-interface=LAN connection-mark=no-mark dst-address-type=!local \
per-connection-classifier=both-addresses:2/1 action=mark-connection new-connection-mark=ISP2_conn
add chain=prerouting connection-mark=ISP1_conn in-interface=LAN action=mark-routing \
new-routing-mark=to_ISP1
add chain=prerouting connection-mark=ISP2_conn in-interface=LAN action=mark-routing \
new-routing-mark=to_ISP2
add chain=output connection-mark=ISP1_conn action=mark-routing new-routing-mark=to_ISP1
add chain=output connection-mark=ISP2_conn action=mark-routing new-routing-mark=to_ISP2
/ ip route
add dst-address=0.0.0.0/0 gateway=10.111.0.1 routing-mark=to_ISP1 check-gateway=ping
add dst-address=0.0.0.0/0 gateway=10.112.0.1 routing-mark=to_ISP2 check-gateway=ping
add dst-address=0.0.0.0/0 gateway=10.111.0.1 distance=1 check-gateway=ping
add dst-address=0.0.0.0/0 gateway=10.112.0.1 distance=2 check-gateway=ping
/ ip firewall nat
add chain=srcnat out-interface=ISP1 action=masquerade
add chain=srcnat out-interface=ISP2 action=masquerade
salaam yaar yeh new pcc mikrotik ki load balasing yeh chal nahi rahi is main kia problam hai
LikeLike
Comment by mani — May 8, 2012 @ 4:53 PM
i need this router i have 8 line , all line adsl 20 mb but i get only 400 kb but when i use download excelator i get near about 2 mb download , can u help me and if i used 4 wan router its helpme or not. i am in ksa. how much cost mikrotik 4 wan load balancer.
LikeLike
Comment by raja bazal aslam — May 11, 2012 @ 6:00 PM
if i use rb750 for load balancing and rb750gl as a hotspot in front of rb750 then what would be the result ???? Good, better or best ?
LikeLike
Comment by SHAFQAT FARHAN — May 14, 2012 @ 11:06 AM
Salam sir
sir mere pas 2 mb or 4 mb connection hy mje merging karni hy one lan speed double kiya ap mje configure kardegany ap ka bohat Shukar Guzar raho ga mje mikrotik bikul ni ata or mere pas machine dell 670 server hy sir ap
thodi help kr dain thnx 4
friendsalman@hotmail.com
LikeLike
Comment by syed salman — May 14, 2012 @ 7:12 PM
team viewer ky zariya or kb time de gain plz thnx 4
LikeLike
Comment by syed salman — May 14, 2012 @ 7:13 PM
mikrotik rb750gl kitne ki hai aaj kl ?
LikeLike
Comment by ali zaib — May 16, 2012 @ 9:02 PM
Here are the rates.
http://www.autechnologies.com/network-products-load-balancer-mikrotik-5p-giga-router-board-pakistan-p.2421.aspx
====================================
Also you can get it at your door step from Dream Network at following.
Dreams Network Technology
Karachi , Pakistan
Asia
Office : A-1349 Gulshan-e-Hadeed Phase-1 Karachi
Contact No: +923132118237 , +923332828526
Email: support@dreamnw.com
LikeLike
Comment by Syed Jahanzaib / Pinochio~:) — May 17, 2012 @ 8:47 AM
sir can you tell me how to crack mikrotik 4.17
LikeLike
Comment by obaid — May 19, 2012 @ 6:53 PM
It is not possible to crack MT4.xx or above
http://www.smn4all.tk
LikeLike
Comment by smn4all — May 19, 2012 @ 6:55 PM
just pay for it, its not exactly huge amounts of cash, then you can update easily etc. Actually has anyone found an advantage of pc’s over say 1100ah ?
LikeLike
Comment by Nitrious — May 20, 2012 @ 12:33 PM
1100AH is an excellent piece of Mikrotik RouterOS. Once configured, you won’t have to worry about it.
I have found it very good and stable , it’s also rack supported which makes it comparable with other vendors appliances.
PC have one added advantage that you can increase its capacity in terms of storage and speed by adding more storage or processor/board.
LikeLike
Comment by Syed Jahanzaib / Pinochio~:) — May 20, 2012 @ 8:14 PM
hello sir,
can u plz tell me how can i reduce raw bandwidth for vpn converted bandwidth? currently i have a vpn server. it used 1 Mbps vpn bandwidth = 2.3 Mbps Rab (Local ISP) bandwidth. i need to reduce my local isp bandwidth so there any soluation for that?plz inform me sir, it’ll be vary great full to me.my email address is – pialdhkbd@gmail.com
Thanks
LikeLike
Comment by Md. Rezwan ul Alam — May 24, 2012 @ 3:23 PM
Hello Sir,
i m facing some problem in my Microtik. i have 7 Mbps Bandwidth & manage my bandwidth by Microtik.problem is my bandwidth shows in my queue rules in group 5.6/5.7 Mbps but if i see my interface then i see it using near about 7 Mbps.so i m facing packet loss issue.why it’s happening sir? i m also checked all my IP address.only specific IP address is open so no 1 can steal bandwidth from my server … then why it’s happens? plz advice me sir ASAP.
LikeLike
Comment by Md. Rezwan ul Alam. PIal — June 2, 2012 @ 7:02 AM
slam alikom
ihave mikrotik on x86 with 2 lan card and i’m plane to load balance using 4 wan can i made that using vlan
thank you
LikeLike
Comment by hesham — June 2, 2012 @ 11:12 AM
Hi,
technically its possibly but try find a switch that implements it properly. After 5 brands I gave up and used a 1100AH. A RB750 would suit your needs just fine.
LikeLike
Comment by Nitrious — June 3, 2012 @ 11:37 AM
Yes you can.
LikeLike
Comment by Syed Jahanzaib / Pinochio~:) — June 4, 2012 @ 10:05 AM
Asalam o Alikum Bro. how can we use User Manager and manage users and their accounting on v3.3 with level4 license. if their some solution please tell me how can i do it.
LikeLike
Comment by Junaid — June 3, 2012 @ 10:39 AM
Previous versions have bugs and simultaneous login from same ID issue.
Go and buy Licensed version.
LikeLike
Comment by Syed Jahanzaib / Pinochio~:) — June 4, 2012 @ 10:06 AM
hey, i need help in load balancing, i have do like u right in the first, but it’s the same, all pppoe client use the same account (wan1) , i have rb750 version 5.2, can u help me please.
LikeLike
Comment by Peter — June 6, 2012 @ 2:57 AM
Hello,
I applied 4 wan PCC +Hotspot with your directions on RB450 today for a student dormitory building witch has aprx. 120 students and it is working like a charm.
But I figured out hotspot transparent proxy does not work. Even I tried NAT forwarding rule but it didn’t work also. (NAT forwarding works only when I disable hotspot)
I am trying to avoid users to download illegal copyrighted content from web. I have no chance to use external proxy. Do you have any suggestion?
Thank you.
LikeLike
Comment by nacer — June 11, 2012 @ 12:02 AM
Hi,
Thanks for uploading the script. I have a small WISP in Albania. For the moment i have 4 WAN connections with a total throughput 20Mbps and i am using a Mikrotik RB450G as a PPPoE Server for my network. When i write the /ip route code and i open winbox at IP->Route> only the first Gateway is OK. Three other gateways are in blue. I change the distance but is the same thing. Also i want to tell you that three WAN are from the same ISP. My network doesn’t have performance. When the clients are surfing webpages in internet they need to refresh the page in way to open it. Can you help me please?
Thank you very much !
Klevis.
LikeLike
Comment by maxnetisp — June 14, 2012 @ 6:15 AM
# For PCC with PPPoE Server on same box, use the below script
https://aacable.wordpress.com/2011/08/29/mikrotik-4-wan-load-balancing-using-pcc-with-pppoe-server-complete-script/
# For unstable browsing issue, Try changing your PCC classifier to src-address.
LikeLike
Comment by Syed Jahanzaib / Pinochio~:) — June 14, 2012 @ 10:56 AM
bhai aap ka contect # kia hai ? bhai 5 wan 4mbps ki lagane se lan me 20 mbps speed aey gi ?
LikeLike
Comment by Qasim Electronics — June 25, 2012 @ 10:15 PM
PCC only load balance connections between multiple WAN, it don’t MERGE the wan connections.
LikeLike
Comment by Syed Jahanzaib / Pinochio~:) — June 27, 2012 @ 9:02 AM
you can get more speed on downloads through pcc by using a download manager with multiple threads. I got 48Mbps via 7 x 8Mbps lines that way. Its not consistent though, and it isnt 48Mbps internet either, browsing etc is still at 8Mbps.
LikeLike
Comment by Nitrious — June 27, 2012 @ 7:36 PM
I have tried the script but i think you have to mension that you have to change the interfaces setting not to be slave with port 1. also in my test i have 12 pcs with 2 adsl wans and all the pcs are passing through wan 1. i can see only some kb coming from adsl wan 2. i dont know if i am making anything wrong. any suggestion?
LikeLike
Comment by zoubit — June 29, 2012 @ 5:17 AM
thanks for you detailed script, can i use hotspot on the local interface, does it need any change in the routing line, i read somewhere for hot spot the last line in the route has to be rip not ping. please clarify
LikeLike
Comment by jibd — June 29, 2012 @ 9:32 AM
No need to change in routing line.
fyi:
LikeLike
Comment by Syed Jahanzaib / Pinochio~:) — July 1, 2012 @ 5:32 PM
how to access mikrotik by team viewer from any where ? can u help me pls?
LikeLike
Comment by ruhul — July 9, 2012 @ 5:33 PM
brother i have mikrotik router os 2.7.9 and rb 750 i want to distribute net tell me i use rb 750 for modem and also for loadbalancing or rb 750 for loadbalancing and router for modem………waqar_love15@yahoo.com what is ur hotmail adress?????
LikeLike
Comment by waqar — July 15, 2012 @ 12:08 AM
i want to access shared folders and remote desktop etc after extabishing PPTP VPN, my PPTP vpn is working ok but i am unable to access share folder and remote desktop. i ahve two WAN and LAN, one wan has Live IP other is private ip which is PTCL, can you please help me to make rule to access shared folders and remote desktop after establishing PPTP VPN, please write rules for above scenario. Thank you
LikeLike
Comment by opheliapu — July 17, 2012 @ 4:09 PM
this is raju from india, andhrapradesh.
Iam using mikrotik 750g router. iam using hotspot server in this.
but 30% web sites are not opening all times with hotspot clients.
If i setup simple queue, then all clients(queue) can access all web sites.
please give suggestion to me.
LikeLike
Comment by raju — July 24, 2012 @ 10:59 PM
Try changing the classifier to src-address
LikeLike
Comment by Syed Jahanzaib / Pinochio~:) — July 25, 2012 @ 9:42 AM
i have a problem with mikrotik i found that some people hack the network by using mac address they connect to intenet by tacking any mac active how can i block this plz help me
LikeLike
Comment by mohamed — July 28, 2012 @ 1:46 AM
[…] […]
LikeLike
Pingback by Anonymous — July 31, 2012 @ 10:38 PM
Hello, I wish to implement your load balancing code above. I have one WAN connection that has a static IP (there is a switch on this also to handle my DNS and Email servers). The other 2 WAN connections are DHCP cable modems.
Can you tell me what I need to change to make this work?
Thank you.
LikeLike
Comment by J West — August 6, 2012 @ 11:06 PM
your script support fail-over..? if not plz make one for me and not in ppoe
Regards
Muhammad Ahtesham
LikeLike
Comment by Ahtesham — August 29, 2012 @ 11:55 AM
salam sir ap se ek request karni thi sir main squid proxy server banaliya hy lkin her client may proxy ki manual setting karni parti hy lihaza ap mje aisa rule de jis se kisi bi browser may manual proxy ki setting na karo na idm may or sir ek or problem jab may squid proxy server lagta ho tu na facebook login hoti hy na yahoo or na koi messanger plz sir may ap se help mag raha Allah ap ko jaze khair de or sir squid proxy ki script sent kar dije ga shukriya ky sath ap ka bhai Syed Salman thnx 4 u khush rahain hamesha ap hamari dua ap ky sath hy please sir Date: Wed, 29 Aug 2012 07:40:36 +0000 To: friendsalman@hotmail.com
LikeLike
Comment by Salman Habib — August 30, 2012 @ 5:33 AM
Configure SQUID in Transparent mode, Aslo configure iptables so that it can redirect port 80 to 8080 automatically.
I Don’t know how you have configure your network , I can’t suggest more without knowing the exact details.
LikeLike
Comment by Syed Jahanzaib / Pinochio~:) — August 30, 2012 @ 9:11 AM
I need help with this script. Send you an e-mail about it.
LikeLike
Comment by Orkut — September 6, 2012 @ 6:16 PM
Hi you there . Regards from Mexico.
I was reading your blog and seems like is very interesting , im working on a scenario where a I need to forward a set of ports to access a DVR or a web server, i have a load balancing scenario with two lines and seems like im making something wrong because even when the nat setup is ok , the portforwarding is not working. can you please give a advice ?
Regards.
LikeLike
Comment by acriollo — September 26, 2012 @ 5:36 AM
I never got a change to setup port forwarding with the PCC, its a bit complicated, read the mikrotik forum, lot of posts are there explaining the same.
LikeLike
Comment by Syed Jahanzaib / Pinochio~:) — September 28, 2012 @ 9:09 AM
Hi syed
we currently route tcp 53 80 443 using a mark routing rule through to our one gateway and all other traffic through another gateway. obviously in the routing table all the routing marks setup. My question is do you perhaps know of a script that will ping an external ip through the routing marked gateway, and automatically fail over to the second gateway if it fails.
Thanks
LikeLike
Comment by jacques grundling — October 3, 2012 @ 4:17 PM
There are few ways you can achieve this. possibilities are . . .
# Create a rule that mark traffic going to specific WAN ip (monitoring Ip lets say 8.8.8.8)
# Create a route that route monitoring ip to go through specific route (route that you want to monitor)
# Create a script that checks ping to that monitoring ip, and i it doesn’t receive response, lets say fail to get at least 3 ping reply, yhen it should disable the marking rules for marking specific traffic, and if gets replies, then it should enable the rule, its very simple to do such stuff, just try.
LikeLike
Comment by Syed Jahanzaib / Pinochio~:) — October 5, 2012 @ 8:28 AM
goodnight friend would like a hand by its what i read in your entire page,
I realize that you know much about mikrotik.
I have 2 links and 2 of 5 mb 10 mb using PPPoE to authenticate load.
you have any examples of how I can optimize these 4 link?
you did one more example I could not customize it for my load
do not you give me a hand in the rules?
LikeLike
Comment by euemerson — November 2, 2012 @ 6:16 AM
thanks for your reply its really apresiated. Didnt think of doing that to be honest.
thanks again
LikeLike
Comment by jacques grundling — October 7, 2012 @ 9:12 PM
PCC WITH UN-EQUAL WAN LINKS
If you have Un-Equal WAN Links, for example WAN,1,2,3 are of 4MB and WAN,4 is of 8 Mb, and you want to force MT to use WAN4 link more then other because of its capacity, Then you have to Add more PCC rules assigning the same two marks to a specific link i.e WAN4 , something like
Code:
1 add chain=prerouting dst-address-type=!local in-interface=Local per-connection-classifier=both-addresses-and-ports:4/0 action=mark-connection new-connection-mark=WAN1_conn passthrough=yes
2 add chain=prerouting dst-address-type=!local in-interface=Local per-connection-classifier=both-addresses-and-ports:4/1 action=mark-connection new-connection-mark=WAN2_conn passthrough=yes
3 add chain=prerouting dst-address-type=!local in-interface=Local per-connection-classifier=both-addresses-and-ports:4/2 action=mark-connection new-connection-mark=WAN3_conn passthrough=yes
4 add chain=prerouting dst-address-type=!local in-interface=Local per-connection-classifier=both-addresses-and-ports:4/3 action=mark-connection new-connection-mark=WAN4_conn passthrough=yes
5 add chain=prerouting dst-address-type=!local in-interface=Local per-connection-classifier=both-addresses-and-ports:4/4 action=mark-connection new-connection-mark=WAN4_conn passthrough=yes
the 5th one is not running and also no receiving and sending bytes and packets if we do (per-connection-classifier=both-addresses-and-ports:4/4) then it did’t receive any packet.
LikeLike
Comment by Mubashir Shahzad — October 20, 2012 @ 11:49 PM
it should be like this
1 add chain=prerouting dst-address-type=!local in-interface=Local per-connection-classifier=both-addresses-and-ports:5/0 action=mark-connection new-connection-mark=WAN1_conn passthrough=yes
2 add chain=prerouting dst-address-type=!local in-interface=Local per-connection-classifier=both-addresses-and-ports:5/1 action=mark-connection new-connection-mark=WAN2_conn passthrough=yes
3 add chain=prerouting dst-address-type=!local in-interface=Local per-connection-classifier=both-addresses-and-ports:5/2 action=mark-connection new-connection-mark=WAN3_conn passthrough=yes
4 add chain=prerouting dst-address-type=!local in-interface=Local per-connection-classifier=both-addresses-and-ports:5/3 action=mark-connection new-connection-mark=WAN4_conn passthrough=yes
5 add chain=prerouting dst-address-type=!local in-interface=Local per-connection-classifier=both-addresses-and-ports:5/4 action=mark-connection new-connection-mark=WAN4_conn passthrough=yes
LikeLike
Comment by Ahmad jamal — October 3, 2013 @ 8:20 PM
i want to force wan 4 please tell me best way of forcing
Regards.
LikeLike
Comment by Mubashir Shahzad — October 20, 2012 @ 11:51 PM
i have 1 wan 192.168.10.1 and another wan with pppoe how load banlance ?
LikeLike
Comment by Alan — October 26, 2012 @ 9:29 PM
Sir I am using three links in which two from same ISP by using DSL and 3rd is direct link in which I have live IP which is given to me by ISP I want to loadbalance
my 3 links can You tell me how can I accomplish my goal. My 1st ISP scheme is 192.168.1.1/24 2nd is 192.168.2.1/24 and third is 202.142.165.250/30.
Can You help me in this scenario?
LikeLike
Comment by Dawood Ismail — October 31, 2012 @ 2:42 PM
Hello thanks for the script have two questions
1. what is this “dst-address-type=!local” ……what do you mean dst address type = !local??????? should I be adding something in there like my “local port” ip address?????
2. what would I add to this script so that I can let certian Lan side ip address skip by the load balancing and get directed to a specific wan port?
thanks in advance for all your time and effort it is very much appreciated
LikeLike
Comment by Stephen — November 13, 2012 @ 5:28 AM
Assalaanm o alikum.. sir maine mikrotik 5.18 kia hua hai.. PPPOE setup k sath.. sir main 3 wan ki load balacing kar raha hoon magar Sara load WAN1 per ja raha hai. na load divide ho raha hai na murging :(.. PLEASE Help me.. EK hi server main load balancing kar raha hoon n pppoe server bhi usi main hai… 2gb RAm dual core processor..
LikeLike
Comment by waqas — November 14, 2012 @ 3:38 AM
Hello,
I have used your script and every thing goes fine. I would be grateful if you can help me to resolve my new issue. For the moment i have 2ADSL Lines x 24Mbps and 10/10Mbps Dedicated Fiber. Now we want that upload of our network to go out with fiber line because our ADSL lines have only 512kbps of upload.
Thanks a lot buddy!
LikeLike
Comment by maxnetisp — November 25, 2012 @ 4:52 PM
very usefull post
in my scenario i have a server with static ip and two wan connectios ,and i want the server to use only wan0 and the other part of pc to use wan1, is it possible and how?
thanks in advance, best regards
LikeLike
Comment by ronald — November 26, 2012 @ 2:30 AM
If i use Squid, then all http browsing and downloading (port 80) will only use 1 dsl line, am i correct?
LikeLike
Comment by Mark — December 2, 2012 @ 3:55 AM
not necessary, you can utilize all wan links for squid. depend on the pcc config.
LikeLike
Comment by Syed Jahanzaib / Pinochio~:) — December 2, 2012 @ 11:35 AM
sir agar ek dsl band ho jay to sab pe deta sahi nahi milta is ka koi hal ho sakta hai
LikeLike
Comment by imtiaz ali — December 10, 2012 @ 2:12 PM
Hi!
First of all, thanks alot for helping me learning mikrotik!
I am currentyl using this config at my home but I will be using only 3 WAN connection on my 5ports router.
With this config It go from WAN 1 To WAN3, If WAN1 is full it go to WAN2 and then WAN3
I have a question for you
Is there any way to make certain user or user from the hotspot to use on the other side, WAN3, if full it will go WAN2 but never WAN1 I wan to keep it for myself
LikeLike
Comment by David — December 15, 2012 @ 9:17 PM
Include 2 WAN’s only in the PCC, and mark your own ip traffic in mangle rule and bind it with WAN 3. This way no one else will be using WAN3 and only you can use it.
There is no way you can define that IF wan1 is full , then request should go to WAN2. PCC doesn’t work this way. It just distribute the traffic among various WAN depends on the classifier you set in PCC.
LikeLike
Comment by Syed Jahanzaib / Pinochio~:) — December 16, 2012 @ 10:22 AM
nice articel,lanjutkan
LikeLike
Comment by aditw — December 20, 2012 @ 11:03 PM
Nice share, how about Load balancing 4 WAN and support for Fail Over, I do need your help, please?
LikeLike
Comment by Mulyawan — December 24, 2012 @ 11:42 AM
hi all, i have rb 750gl. and connected already to a 4 (5mb adsl internet), load balance is already configure and working. why is it that when i do speedtest i only got 10 mb instead of 20mb as per line is 5mb? is anything lucking on my config? i just a follow scripts here on pcc load balancer. please help. thank you..
LikeLike
Comment by Aguilar NewTon — December 27, 2012 @ 8:50 AM
Its by default.
If you will download multiple files simultaneously, you will be able to get full combined bandwidth of all WAN links.
It also depends on the Classifier you use in PCC. Also try IDM
LikeLike
Comment by Syed Jahanzaib / Pinochio~:) — December 27, 2012 @ 9:45 AM
hi! may i know what the target of this ip add? i know that is pointing interface, what if i have a dynamic public ip?
/ip address
add address=192.168.1.2/24 network=192.168.1.0 broadcast=192.168.1.255 interface=WAN1
LikeLike
Comment by jr — December 30, 2012 @ 11:26 PM
You don’t have to set any ip address on WAN interface. It will get dynamic ip via dialing pppoe client you configure in ppp/pppoe.client.
Try with following.
http://mikrotikservers.blogspot.com/2012/02/load-balance-mikrotik-with-pcc-using.html
LikeLike
Comment by Syed Jahanzaib / Pinochio~:) — December 31, 2012 @ 9:51 AM
Asalam O Alikum ,
Can anyone help me please?
The scenario is that i have 2 Internet Connections which i want put in mikrotik RB750GL and combine their bandwidth and want it to auto balance load as well. I also want to filter some websites and block fileuploading ?
what script will be best for this scenario?
Best Regards,
Muhammad Usman
LikeLike
Comment by Muhammad Usman — January 20, 2013 @ 4:28 AM
Dear USMAN, please follow this.
LikeLike
Comment by Syed Jahanzaib / Pinochio~:) — January 21, 2013 @ 10:54 AM
main ne 2 PTCL ADSL ki loadbalancing ki hai with this script. Works Gr8.
lekin jab aik line disconnect hoti hai tu websites pe . GateWay TimeOut ka error aata hai bar bar…
So is k liye main kia kerun..???
LikeLike
Comment by hammad hassan — February 5, 2013 @ 5:33 PM
sir can u send me the backup file for 4 wan and 1 lan
with local ip 192.168.0.1 lan
and Wan1 192.168.1.1
wan2 192.168.2.1
wan3 192.168.3.1
wan 4 192.168.4.1
i am thankfull to you
@ = sadkeyjaoon@gmail.com
LikeLike
Comment by omerfraz — February 14, 2013 @ 6:59 PM
Hi,
Tried this it works like flame. Great job I must say
Please could you provide info on how to expand the Local interface to say N = 1,2,3,…N either as separate interfacese or VLANs.
I will appreciate the magic ‘cos I run a very large network with over 200 VLANs.
Thanks a billion times in advance.
LikeLike
Comment by Meshack — February 18, 2013 @ 10:18 PM
hi , i have loadbalencing 4wan , i have used you script but is not working, plz solves the problem, plz
LikeLike
Comment by adannaveed — February 27, 2013 @ 5:53 PM
add chain=prerouting dst-address-type=!local in-interface=Local per-connection-classifier=both-addresses-and-ports:4/0 action=mark-connection new-connection-mark=WAN1_conn passthrough=yes
add chain=prerouting dst-address-type=!local in-interface=Local per-connection-classifier=both-addresses-and-ports:4/1 action=mark-connection new-connection-mark=WAN2_conn passthrough=yes
add chain=prerouting dst-address-type=!local in-interface=Local per-connection-classifier=both-addresses-and-ports:4/2 action=mark-connection new-connection-mark=WAN3_conn passthrough=yes
add chain=prerouting dst-address-type=!local in-interface=Local per-connection-classifier=both-addresses-and-ports:4/3 action=mark-connection new-connection-mark=WAN4_conn passthrough=yes
add chain=prerouting dst-address-type=!local in-interface=Local per-connection-classifier=both-addresses-and-ports:4/4 action=mark-connection new-connection-mark=WAN4_conn passthrough=yes
this s not runnng
LikeLike
Comment by waqar — March 1, 2013 @ 11:14 PM
Sir Salam how r u fariya ny jo tv streming server banay us may kiya kiya acceries lagi hy or wo kese tyar hota hy plz guid
LikeLike
Comment by salman — March 3, 2013 @ 3:33 PM
All you need is following.
Any Normal pc like pentium 4 with 512MB Ram,
TV tunner card,
Windows XP or above.
VLC Media Player.
Its complete guide is available at my blog search it.
LikeLike
Comment by Syed Jahanzaib / Pinochio~:) — March 3, 2013 @ 11:43 PM
dear sir,
Fariya Or connect merge karna hain maray pas 750gl router hain main kasay karo or for example
connect pptp + Fariya pptp = lan dhcp with pptp
i need configration
LikeLike
Comment by yasir — September 6, 2014 @ 4:54 AM
Sir, i cant get Unequal Loadbalancing at all. I have 4 Wans, all are 4mb except WAN2, which is 10mb. I added extra PCC Rule for that too. something like this:
add chain=prerouting dst-address-type=!local in-interface=Local per-connection-classifier=both-addresses-and-ports:4/0 action=mark-connection new-connection-mark=WAN1_conn passthrough=yes
add chain=prerouting dst-address-type=!local in-interface=Local per-connection-classifier=both-addresses-and-ports:4/1 action=mark-connection new-connection-mark=WAN4_conn passthrough=yes
add chain=prerouting dst-address-type=!local in-interface=Local per-connection-classifier=both-addresses-and-ports:4/2 action=mark-connection new-connection-mark=WAN3_conn passthrough=yes
add chain=prerouting dst-address-type=!local in-interface=Local per-connection-classifier=both-addresses-and-ports:4/3 action=mark-connection new-connection-mark=WAN2_conn passthrough=yes
add chain=prerouting dst-address-type=!local in-interface=Local per-connection-classifier=both-addresses-and-ports:4/4 action=mark-connection new-connection-mark=WAN2_conn passthrough=yes
But still i dont get more than 4 at all. And the last PCC chain rule is not showing bytes send or recieve too. I tried to search about at as much as i could do,, but still i am not getting into solution.
LikeLike
Comment by Aftab Ahmed — March 5, 2013 @ 2:26 PM
ASLAM-O-ALAIKUM SIR ap bohat acha guide karte hain ALLAH AZZAWAJAL ap ko lambi zindagi ata kare apni tabe farmani mein aamin . sir mujhe load balancing mein problum aa rahi hai line tou merge ho jati hai laikin sirf download hi hota hai upload nahi hota plz iss k liye koi tariqa tajveez kar dein JAZZAKALLAH
LikeLike
Comment by fouzaib — March 7, 2013 @ 9:13 AM
Upload dont get merge as download does.
LikeLike
Comment by Syed Jahanzaib / Pinochio~:) — March 7, 2013 @ 11:59 AM
Assalam O Alaikum Sir mujhe 10+10+4+4 ki Script bana ha to may kiya karo???
LikeLike
Comment by Arsalan Malick — March 11, 2013 @ 2:10 AM
Assalam alli Kumm… bhaiyoon….mujjhe ek porb hay pochni hay koi bata sakta hay kaisay hoo ga sahi..
porb ya hay k may mikrotik ka router 450G use kar raha hoon.. ya 8 say 10 hurs sahi chalta hay phier hang hoo jata hay ping aa rahi hooti hay getway ki per data nahi aata na hotsport ka page khulta hay user id passwoord ka .. kiya karoon ??? please help Kashif 0300-2425540
LikeLike
Comment by Kashif — March 11, 2013 @ 8:44 PM
Possibly your WAN connection goes down after few hours.
Have you tried login to mikrotik using winbox? does it works?
Try changing the RB on a test purpose , you can use pc also for test purposes with cloned settings.
LikeLike
Comment by Syed Jahanzaib / Pinochio~:) — March 12, 2013 @ 8:57 AM
Dear jehnzaib, I am still waiting for the solution of my 4 WAN Loadbalancing unequal.
LikeLike
Comment by Aftab — March 12, 2013 @ 2:38 PM
sir ma na kitne he saawal kiye bt jawab nai mila ap sirf is sawal ka jawab da da k loadbalancing konsi best ha live channel 1 mb pa buffering karty ha wo na karan?????
LikeLike
Comment by waqar — March 20, 2013 @ 9:08 AM
You will face buffering issues in PCC. Its the default behaviour. Try with src-address approach, it works without any issue.
but user must be hitting your pcc box directly,
LikeLike
Comment by Syed Jahanzaib / Pinochio~:) — March 21, 2013 @ 9:09 AM
salam Sir mujhe PPTP ki 4 I.D k load-Balancing karni hai kindly help me please
LikeLike
Comment by waqas — March 23, 2013 @ 1:31 AM
hi,
how can i check the script working or not?
i use 2 adsl, when i check with speedtest.net on one pc it get the WAN1 and the other WAN2 is this correct?
LikeLike
Comment by ali — April 5, 2013 @ 3:20 PM
Hello, in my country we use pppoe connection with the ISP (the ISP provides username & password). In order to setup the one pppoe client to my mikrotik, I create a pppoe interface with username and password, then I chose the interface where I connect the the ethernet cable that comes from the modem (which I have installed in bridge mode). Then in the NAT I create a rule that masquerade with out interface the pppoe interface that I have created before.
Now in case that I have payed my ISP for more than one PSTN lines (for example, two lines) and in each line ISP provides me a pppoe client connection with username and password. What exactly have to do in order my mikrotik will handle the two internet connections like one and my speed will be higher?
I now that this has been mentioned again in previous post but I didn’t really understand how to configure mikrotik. Could you please provide me some instructions in order to achive this?
Regards
LikeLike
Comment by ifthisisaman — April 6, 2013 @ 2:53 AM
Is it enough if I make a bridge for the two pppoe interfaces and masquerade with out interface the bridge with the two pppoe interfaces?
LikeLike
Comment by ifthisisaman — April 6, 2013 @ 2:57 AM
when i type add chain=prerouting dst-address-type=!local in-interface=Lan per-connection-classifier=both-addresses-and-ports:2/0 action=mark-connection new-onnection-mark=WAN1_conn passthrough=yes
Than show bad argument name per-connection-classifier (line 1 column 63) for PCC any other configure need. please help me
LikeLike
Comment by santonu — April 16, 2013 @ 5:05 PM
What mikrotik version you are using?
LikeLike
Comment by Syed Jahanzaib / Pinochio~:) — April 17, 2013 @ 8:10 AM
3.22
LikeLike
Comment by santonu — April 17, 2013 @ 3:09 PM
3.22 is not supported.
Use at least 3.30 which is also obsolete version. Try with 5.20 or above.
LikeLike
Comment by Syed Jahanzaib / Pinochio~:) — April 18, 2013 @ 8:12 AM
Hello,
I use this script for 4 WAN Load Balancing on a RB2011L-RM and RouterOS 5.24.
I have 4x DSL lines 22-23Mbps each one.
The problem is that i cannot get more than 23-24Mbps in total when i make some download test from 2 Laptops at the same time.
Normally i should get 23-24Mbps in one Laptop and 23-24Mbps in the other, so ~46-48Mbps in total.
Is this right?
Thank you
LikeLike
Comment by tsatasos — April 17, 2013 @ 4:24 AM
Yes that’s right.
What classifier you are using in PCC ?
If both-addressess-and-ports are selected, then you should be able to download using both link, but if you are using browser base download, then you will be able to suck bandwidth via single wan only. Try to download multiple files using IDM or any download manager and see whats the result.
LikeLike
Comment by Syed Jahanzaib / Pinochio~:) — April 17, 2013 @ 8:08 AM
I’m using exactly the first script. I have only changed ip addresses and interface names.
I tried to download 2 files from one laptop and 2 files from the other laptop at the same time (nvidia & ati drivers).
I see that download comes from all 4 wans – 6Mbps from each wan = 24Mbps in total.
LikeLike
Comment by tsatasos — April 17, 2013 @ 11:19 AM
I tried using PPPoE in routerboard, but same situation.
Export command for mangle, nat & route:
LikeLike
Comment by tsatasos — April 18, 2013 @ 4:37 AM
How can you access the MKT wiht PCC remotely using Winbox? Thanks
LikeLike
Comment by Roberto — April 24, 2013 @ 5:05 AM
bro any idea about Bandwidth Based Load Balancing
Click to access Load_Balancing_workshop.pdf
i am unable to understand, however i can see that the configuration show bandwidth like, wan1=7 mb, wan2=3mb, wan3=9 mb, i beleive that PCC is not a good method for load balancing of different (or even same) bandwidth WANs.
http://forum.mikrotik.com/viewtopic.php?t=72016&p=365766
no help online, please help us in this regard, if you have worked on it
thanks
LikeLike
Comment by Quality DSL — April 28, 2013 @ 1:55 PM
Load Balancing 4 LINE ISP+PROXY EKSTERNAL
http://mr-ekoapriadi.blogspot.com/2013/05/tutorial-load-balancing-4-line-ispproxy.html
LikeLike
Comment by Adam Setiawan — May 6, 2013 @ 11:44 PM
Hi
i have 450g and 4x16mb ADSL
ether1=wan1 ether2=wan2 ether3=local ether4=wan4 ether5=wan5
how i can merge all dsl ?
best regart
LikeLike
Comment by ALi — May 7, 2013 @ 12:59 AM
Mikrotik DUAL WAN Load Balancing using PCC method. Complete Script !
http://mr-ekoapriadi.blogspot.com/2013/03/mikrotik-dual-wan-load-balancing-using.html
LikeLike
Comment by adam setiawan — May 12, 2013 @ 10:34 AM
Thanks for the tutorial, it helps.
A simple query:
the addresslist
“” dst-address-type=!local “”
than all the Local
there in the list address local mius would have to put all local subnets?
for example:
Wan 172.17.1.2/24
Local subnet: 192.168.50.0/24 – 192.168.51.0/24
add the list addres 192.168.50.0/24 – 192.168.51.0/24?
LikeLike
Comment by Ariel — May 17, 2013 @ 2:20 AM
Hello Thanks for your script and all the help you give us wanabees.
I have this working but some Clients can not connect to secure servers or vpns because it bounces their connection between the four WAN connections thus changing their Public IP.
What would be the mangle rule to set up an address list to force a given Client’s LAN IP out only one of the four WAN connections
LikeLike
Comment by Stephen — June 17, 2013 @ 10:26 PM
yaar mujhe 3modem ki load balcing kerni hai is ma prob ye hai k mare pass 2worldcal ki line hai or wo mac adress pe hen un ko kese add krn
LikeLike
Comment by Samar Abbas — June 21, 2013 @ 2:07 PM
i don’t understand last post. Can you be a little more understandable, pls? I have same problem 🙂
LikeLike
Comment by Vladan Bojović — June 23, 2013 @ 4:12 PM
if you have a ADSL modem.
The first step.
set you modem to bridge mode. Create interfaces pppoe for your connection ADSL with your user and password (ISP).
mark
x add default route
x use peer DNS
create de GATEWAY with IP of your modem
create the in rules in the firewall. NAT
chain: srcnat
out interface: ppoe-out [1,2,3…….]
action: masquerade
LikeLike
Comment by Lmorgoth — July 20, 2013 @ 7:46 PM
Thank you for this tutorial!
I need help on a 1:1 nat.
Since I activated the load balancing 5 lines following this wonderful tutorial, I can not run the nat 1:1. How do I use a nat 1:1, even if it is active load balancing?
Thank you!
LikeLike
Comment by SimpleMind — August 10, 2013 @ 9:07 PM
P.s. i have a 16 ip address for each ADSL.
LikeLike
Comment by SimpleMind — August 10, 2013 @ 9:14 PM
can u please tell me how to run the script?
LikeLike
Comment by suleman — September 4, 2013 @ 8:29 PM
Hi ,
I would like to know about this device-
I have 3 different ISP– One DSL , ONe Copper based Lease Line and One fiber Lease Line.Could you please do let me know that if i can use your device as a gateway and these three lines would be configured as Load balancer.
Will it work for my 100 user network?
Please suggest with which device i have to go –we have Windows network.
Thanks,
Mayank
LikeLike
Comment by Mayank — September 18, 2013 @ 11:43 AM
there are various type of load balancing in mikrotik routerOS.
You can use PCC base load balancing which will distribute traffic to all wan links.
OR
You can also use policy base routing, in which you can create user group based on ips, and then you can tag group with specific wan.
For example if you have 3 wan links, and 30 users, you can create 3 groups with 10 users each, and tag each group with each wan link.
there multiple ways to accomplish the task, choose one which suites you best.
HTH
LikeLike
Comment by Syed Jahanzaib / Pinochio~:) — September 18, 2013 @ 11:53 AM
Thanks for your fast prompt.Can you please provide me link of that model.As i am unable to find out. Does they available in India as well?
LikeLike
Comment by Mayank — September 18, 2013 @ 12:02 PM
Model choice is depend on the network load and requirements.
for smaller number of users, Mikrotik Routerboard RB450G is fine.
for higher number of users, you can go with RB100AHX2 or even better is Clour core router series.
OR you can also install Mikrotik PC version too, means same OS is used in Hardware or software.
LikeLike
Comment by Syed Jahanzaib / Pinochio~:) — September 18, 2013 @ 3:59 PM
Hello Syed!
the load balancing work perfecty , but in SSL or HTTPS website or VPN , it doesn’t work! any idea what should i do in order to solve this? it is very strange sometimes it works for a week after new implementation and then it doesn’t work again!
LikeLike
Comment by Hossein — September 29, 2013 @ 5:39 PM
I just read the post carefully with comments , i am very sorry i find the answer in your comments thanks a lot 😉
LikeLike
Comment by Hossein — September 29, 2013 @ 5:45 PM
welcome
LikeLike
Comment by Syed Jahanzaib / Pinochio~:) — September 30, 2013 @ 10:05 AM
Dear Jhanzaib Bhai
Assalam O Allaykum
3wan load balancing
1 dsl 4mb 2 dsl 4mb 3 dsl 4mb
my dsl router ip 192.168.1.1
192.168.2.1
192.168.31
LikeLike
Comment by shafqat Hussain — October 4, 2013 @ 4:08 AM
Dear Jhanzaib Bhai
Assalam O Allaykum,
I have used the following script for pcc loadbalancing. Now one of my local users wants to pass his traffics through a specific gateway either WAN1 or WAN2. what is the solution?.. Thanks in advance.
Md.Arifujjaman
/ip address
add address=220.247.162.178/30 network=220.247.162.176 broadcast=220.247.162.179 interface=ether2-MIRTEL
/ip firewall mangle
add chain=input in-interface=ether1-WAN action=mark-connection new-connection-mark=ether1-WAN_conn
add chain=input in-interface=ether2-MIRTEL action=mark-connection new-connection-mark=ether2-MIRTEL_conn
add chain=output connection-mark=ether1-WAN_conn action=mark-routing new-routing-mark=to_ether1-WAN
add chain=output connection-mark=ether2-MIRTEL_conn action=mark-routing new-routing-mark=to_ether2-MIRTEL
add chain=prerouting dst-address=172.25.5.196/30 action=accept in-interface=Bridge-Lan
add chain=prerouting dst-address=220.247.162.176/30 action=accept in-interface=Bridge-Lan
add chain=prerouting dst-address-type=!local in-interface=Bridge-Lan per-connection-classifier=both-addresses-and-ports:2/0 action=mark-connection new-connection-mark=ether1-WAN_conn passthrough=yes
add chain=prerouting dst-address-type=!local in-interface=Bridge-Lan per-connection-classifier=both-addresses-and-ports:2/1 action=mark-connection new-connection-mark=ether2-MIRTEL_conn passthrough=yes
add chain=prerouting connection-mark=ether1-WAN_conn in-interface=Bridge-Lan action=mark-routing new-routing-mark=to_ether1-WAN
add chain=prerouting connection-mark=ether2-MIRTEL_conn in-interface=Bridge-Lan action=mark-routing new-routing-mark=to_ether2-MIRTEL
/ip route
add dst-address=0.0.0.0/0 gateway= 172.25.5.197 routing-mark=to_ether1-WAN check-gateway=ping
add dst-address=0.0.0.0/0 gateway=220.247.162.177 routing-mark=to_ether2-MIRTEL check-gateway=ping
add dst-address=0.0.0.0/0 gateway=172.25.5.197 distance=1 check-gateway=ping
add dst-address=0.0.0.0/0 gateway=220.247.162.177 distance=2 check-gateway=ping
/ip firewall nat
add chain=srcnat out-interface=ether2-MIRTEL action=masquerade
LikeLike
Comment by Md.Arifujjaman — October 5, 2013 @ 4:32 PM
try this
LikeLike
Comment by Syed Jahanzaib / Pinochio~:) — October 5, 2013 @ 6:20 PM
Aoa Jehanzeb Bhai..
I am running 4 Multiwan PCC on RB750, 3 of these links are PTCL 4 MB and one is 10MB link from a different ISP. I want to force certain sites to be accessed only Via this 10mb Wan Link.. is it possible.???
LikeLike
Comment by Nabeel — October 12, 2013 @ 12:39 PM
thanks man you are amazing. i wish to see you one day 🙂
LikeLike
Comment by Joseph — October 16, 2013 @ 6:49 AM
Hi,
Please help me to setup 4 WAN loadbalancer with pppoe out 16M/2M,all 4 ADSL lines are from same provider and using same gateway. How to load balance???
Any help appreciated,
Best Regards
Nikos
LikeLike
Comment by Nikos — October 19, 2013 @ 12:39 AM
Try defining the outbound interface.
For example replace this.
/ip routeadd dst-address=0.0.0.0/0 gateway=1.2.3.4 routing-mark=to_wan-ISP1 check-gateway=ping
add dst-address=0.0.0.0/0 gateway=1.2.3.4 routing-mark=to_wan-ISP2 check-gateway=ping
With following
/ip routeadd dst-address=0.0.0.0/0 gateway=1.2.3.4%eth1-ISP routing-mark=to_wan-ISP1 check-gateway=ping
add dst-address=0.0.0.0/0 gateway=1.2.3.4%eth2-ISP routing-mark=to_wan-ISP2 check-gateway=ping
Replace the eth1-ISP with your own wan itnerface name , use the notation % for sure.
If it works , let me know
Regard’s
LikeLike
Comment by Syed Jahanzaib / Pinochio~:) — October 21, 2013 @ 11:59 AM
Hi! anyone who can help me configure my RB1100AH i have 11 DSL lines. Can i bond them together. Please need some help.
LikeLike
Comment by Ryan — October 20, 2013 @ 9:43 AM
BONDING requires ISP involvement too, so forget it if you have no such arrangement at both ends.
You probably want to use LOAD BALANCE to divide load in multiple wan links , which is called LOAD BALANCING.
What problem you are having in load balancing 11 links?
LikeLike
Comment by Syed Jahanzaib / Pinochio~:) — October 20, 2013 @ 1:45 PM
Can you please make a sample script for load balancing in my RB1100AH
Your help will be appreciated much. Thank you in advance.
LikeLike
Comment by Ryan — October 21, 2013 @ 8:23 AM
My problem is when I use the above script it will not work not unless i create a bridge and add all the ether ports.
LikeLike
Comment by Ryan — October 21, 2013 @ 8:25 AM
You don’t need a bridge to create load balancer.
LikeLike
Comment by Syed Jahanzaib / Pinochio~:) — October 21, 2013 @ 8:26 AM
PLEASE CHECK MY SCRIPT. THANKS A LOT.
DSL MODEM IP’s
DSL MODEM 1 = 192.168.3.1
DSL MODEM 2 = 192.168.4.1
DSL MODEM 3 = 192.168.52.1
DSL MODEM 4 = 192.168.60.1
DSL MODEM 5 = 10.10.1.1
DSL MODEM 6 = 10.10.2.1
DSL MODEM 7 = 10.10.3.1
DSL MODEM 8 = 10.10.4.1
DSL MODEM 9 = 10.10.5.1
DSL MODEM 10 = 10.10.6.1
DSL MODEM 11 = 10.10.7.1
/ip address
add address=10.10.100.1/24 network=10.10.100.0 broadcast=10.10.100.255 interface=ether13
add address=172.16.100.1/24 network=172.16.100.0 broadcast=172.16.100.255 interface=ether12
add address=192.168.3.2/24 network=192.168.3.0 broadcast=192.168.3.255 interface=ether1
add address=192.168.4.2/24 network=192.168.4.0 broadcast=192.168.4.255 interface=ether2
add address=192.168.52.2/24 network=192.168.52.0 broadcast=192.168.52.255 interface=ether3
add address=192.168.60.2/24 network=192.168.60.0 broadcast=192.168.60.255 interface=ether4
add address=10.10.1.2/24 network=10.10.1.0 broadcast=10.10.1.255 interface=ether5
add address=10.10.2.2/24 network=10.10.2.0 broadcast=10.10.2.255 interface=ether6
add address=10.10.3.2/24 network=10.10.3.0 broadcast=10.10.3.255 interface=ether7
add address=10.10.4.2/24 network=10.10.4.0 broadcast=10.10.4.255 interface=ether8
add address=10.10.5.2/24 network=10.10.5.0 broadcast=10.10.5.255 interface=ether9
add address=10.10.6.2/24 network=10.10.6.0 broadcast=10.10.6.255 interface=ether10
add address=10.10.7.2/24 network=10.10.7.0 broadcast=10.10.7.255 interface=ether11
/ip dns
set allow-remote-requests=yes cache-max-ttl=1w cache-size=5000KiB max-udp-packet-size=512 servers=221.132.112.8,8.8.8.8,8.8.4.4
/ip firewall mangle
add chain=input in-interface=ether1 action=mark-connection new-connection-mark=ether1_conn
add chain=input in-interface=ether2 action=mark-connection new-connection-mark=ether2_conn
add chain=input in-interface=ether3 action=mark-connection new-connection-mark=ether3_conn
add chain=input in-interface=ether4 action=mark-connection new-connection-mark=ether4_conn
add chain=input in-interface=ether5 action=mark-connection new-connection-mark=ether5_conn
add chain=input in-interface=ether6 action=mark-connection new-connection-mark=ether6_conn
add chain=input in-interface=ether7 action=mark-connection new-connection-mark=ether7_conn
add chain=input in-interface=ether8 action=mark-connection new-connection-mark=ether8_conn
add chain=input in-interface=ether9 action=mark-connection new-connection-mark=ether9_conn
add chain=input in-interface=ether10 action=mark-connection new-connection-mark=ether10_conn
add chain=input in-interface=ether11 action=mark-connection new-connection-mark=ether11_conn
add chain=output connection-mark=ether1_conn action=mark-routing new-routing-mark=to_ether1
add chain=output connection-mark=ether2_conn action=mark-routing new-routing-mark=to_ether2
add chain=output connection-mark=ether3_conn action=mark-routing new-routing-mark=to_ether3
add chain=output connection-mark=ether4_conn action=mark-routing new-routing-mark=to_ether4
add chain=output connection-mark=ether5_conn action=mark-routing new-routing-mark=to_ether5
add chain=output connection-mark=ether6_conn action=mark-routing new-routing-mark=to_ether6
add chain=output connection-mark=ether7_conn action=mark-routing new-routing-mark=to_ether7
add chain=output connection-mark=ether8_conn action=mark-routing new-routing-mark=to_ether8
add chain=output connection-mark=ether9_conn action=mark-routing new-routing-mark=to_ether9
add chain=output connection-mark=ether10_conn action=mark-routing new-routing-mark=to_ether10
add chain=output connection-mark=ether11_conn action=mark-routing new-routing-mark=to_ether11
add chain=prerouting dst-address=192.168.3.0/24 action=accept in-interface=ether13
add chain=prerouting dst-address=192.168.3.0/24 action=accept in-interface=ether12
add chain=prerouting dst-address=192.168.4.0/24 action=accept in-interface=ether13
add chain=prerouting dst-address=192.168.4.0/24 action=accept in-interface=ether12
add chain=prerouting dst-address=192.168.52.0/24 action=accept in-interface=ether13
add chain=prerouting dst-address=192.168.52.0/24 action=accept in-interface=ether12
add chain=prerouting dst-address=192.168.60.0/24 action=accept in-interface=ether13
add chain=prerouting dst-address=192.168.60.0/24 action=accept in-interface=ether12
add chain=prerouting dst-address=10.10.1.0/24 action=accept in-interface=ether13
add chain=prerouting dst-address=10.10.1.0/24 action=accept in-interface=ether12
add chain=prerouting dst-address=10.10.2.0/24 action=accept in-interface=ether13
add chain=prerouting dst-address=10.10.2.0/24 action=accept in-interface=ether12
add chain=prerouting dst-address=10.10.3.0/24 action=accept in-interface=ether13
add chain=prerouting dst-address=10.10.3.0/24 action=accept in-interface=ether12
add chain=prerouting dst-address=10.10.4.0/24 action=accept in-interface=ether13
add chain=prerouting dst-address=10.10.4.0/24 action=accept in-interface=ether12
add chain=prerouting dst-address=10.10.5.0/24 action=accept in-interface=ether13
add chain=prerouting dst-address=10.10.5.0/24 action=accept in-interface=ether12
add chain=prerouting dst-address=10.10.6.0/24 action=accept in-interface=ether13
add chain=prerouting dst-address=10.10.6.0/24 action=accept in-interface=ether12
add chain=prerouting dst-address=10.10.7.0/24 action=accept in-interface=ether13
add chain=prerouting dst-address=10.10.7.0/24 action=accept in-interface=ether12
add chain=prerouting dst-address-type=!local in-interface=ether13 per-connection-classifier=both-addresses-and-ports:11/0 action=mark-connection new-connection-mark=ether1_conn passthrough=yes
add chain=prerouting dst-address-type=!local in-interface=ether12 per-connection-classifier=both-addresses-and-ports:11/0 action=mark-connection new-connection-mark=ether1_conn passthrough=yes
add chain=prerouting dst-address-type=!local in-interface=ether13 per-connection-classifier=both-addresses-and-ports:11/1 action=mark-connection new-connection-mark=ether2_conn passthrough=yes
add chain=prerouting dst-address-type=!local in-interface=ether12 per-connection-classifier=both-addresses-and-ports:11/1 action=mark-connection new-connection-mark=ether2_conn passthrough=yes
add chain=prerouting dst-address-type=!local in-interface=ether13 per-connection-classifier=both-addresses-and-ports:11/2 action=mark-connection new-connection-mark=ether3_conn passthrough=yes
add chain=prerouting dst-address-type=!local in-interface=ether12 per-connection-classifier=both-addresses-and-ports:11/2 action=mark-connection new-connection-mark=ether3_conn passthrough=yes
add chain=prerouting dst-address-type=!local in-interface=ether13 per-connection-classifier=both-addresses-and-ports:11/3 action=mark-connection new-connection-mark=ether4_conn passthrough=yes
add chain=prerouting dst-address-type=!local in-interface=ether12 per-connection-classifier=both-addresses-and-ports:11/3 action=mark-connection new-connection-mark=ether4_conn passthrough=yes
add chain=prerouting dst-address-type=!local in-interface=ether13 per-connection-classifier=both-addresses-and-ports:11/4 action=mark-connection new-connection-mark=ether5_conn passthrough=yes
add chain=prerouting dst-address-type=!local in-interface=ether12 per-connection-classifier=both-addresses-and-ports:11/4 action=mark-connection new-connection-mark=ether5_conn passthrough=yes
add chain=prerouting dst-address-type=!local in-interface=ether13 per-connection-classifier=both-addresses-and-ports:11/5 action=mark-connection new-connection-mark=ether6_conn passthrough=yes
add chain=prerouting dst-address-type=!local in-interface=ether12 per-connection-classifier=both-addresses-and-ports:11/5 action=mark-connection new-connection-mark=ether6_conn passthrough=yes
add chain=prerouting dst-address-type=!local in-interface=ether13 per-connection-classifier=both-addresses-and-ports:11/6 action=mark-connection new-connection-mark=ether7_conn passthrough=yes
add chain=prerouting dst-address-type=!local in-interface=ether12 per-connection-classifier=both-addresses-and-ports:11/6 action=mark-connection new-connection-mark=ether7_conn passthrough=yes
add chain=prerouting dst-address-type=!local in-interface=ether13 per-connection-classifier=both-addresses-and-ports:11/7 action=mark-connection new-connection-mark=ether8_conn passthrough=yes
add chain=prerouting dst-address-type=!local in-interface=ether12 per-connection-classifier=both-addresses-and-ports:11/7 action=mark-connection new-connection-mark=ether8_conn passthrough=yes
add chain=prerouting dst-address-type=!local in-interface=ether13 per-connection-classifier=both-addresses-and-ports:11/8 action=mark-connection new-connection-mark=ether9_conn passthrough=yes
add chain=prerouting dst-address-type=!local in-interface=ether12 per-connection-classifier=both-addresses-and-ports:11/8 action=mark-connection new-connection-mark=ether9_conn passthrough=yes
add chain=prerouting dst-address-type=!local in-interface=ether13 per-connection-classifier=both-addresses-and-ports:11/9 action=mark-connection new-connection-mark=ether10_conn passthrough=yes
add chain=prerouting dst-address-type=!local in-interface=ether12 per-connection-classifier=both-addresses-and-ports:11/9 action=mark-connection new-connection-mark=ether10_conn passthrough=yes
add chain=prerouting dst-address-type=!local in-interface=ether13 per-connection-classifier=both-addresses-and-ports:11/10 action=mark-connection new-connection-mark=ether11_conn passthrough=yes
add chain=prerouting dst-address-type=!local in-interface=ether12 per-connection-classifier=both-addresses-and-ports:11/10 action=mark-connection new-connection-mark=ether11_conn passthrough=yes
add chain=prerouting connection-mark=ether1_conn in-interface=ether13 action=mark-routing new-routing-mark=to_ether1
add chain=prerouting connection-mark=ether1_conn in-interface=ether12 action=mark-routing new-routing-mark=to_ether1
add chain=prerouting connection-mark=ether2_conn in-interface=ether13 action=mark-routing new-routing-mark=to_ether2
add chain=prerouting connection-mark=ether2_conn in-interface=ether12 action=mark-routing new-routing-mark=to_ether2
add chain=prerouting connection-mark=ether3_conn in-interface=ether13 action=mark-routing new-routing-mark=to_ether3
add chain=prerouting connection-mark=ether3_conn in-interface=ether12 action=mark-routing new-routing-mark=to_ether3
add chain=prerouting connection-mark=ether4_conn in-interface=ether13 action=mark-routing new-routing-mark=to_ether4
add chain=prerouting connection-mark=ether4_conn in-interface=ether12 action=mark-routing new-routing-mark=to_ether4
add chain=prerouting connection-mark=ether5_conn in-interface=ether13 action=mark-routing new-routing-mark=to_ether5
add chain=prerouting connection-mark=ether5_conn in-interface=ether12 action=mark-routing new-routing-mark=to_ether5
add chain=prerouting connection-mark=ether6_conn in-interface=ether13 action=mark-routing new-routing-mark=to_ether6
add chain=prerouting connection-mark=ether6_conn in-interface=ether12 action=mark-routing new-routing-mark=to_ether6
add chain=prerouting connection-mark=ether7_conn in-interface=ether13 action=mark-routing new-routing-mark=to_ether7
add chain=prerouting connection-mark=ether7_conn in-interface=ether12 action=mark-routing new-routing-mark=to_ether7
add chain=prerouting connection-mark=ether8_conn in-interface=ether13 action=mark-routing new-routing-mark=to_ether8
add chain=prerouting connection-mark=ether8_conn in-interface=ether12 action=mark-routing new-routing-mark=to_ether8
add chain=prerouting connection-mark=ether9_conn in-interface=ether13 action=mark-routing new-routing-mark=to_ether9
add chain=prerouting connection-mark=ether9_conn in-interface=ether12 action=mark-routing new-routing-mark=to_ether9
add chain=prerouting connection-mark=ether10_conn in-interface=ether13 action=mark-routing new-routing-mark=to_ether10
add chain=prerouting connection-mark=ether10_conn in-interface=ether12 action=mark-routing new-routing-mark=to_ether10
add chain=prerouting connection-mark=ether11_conn in-interface=ether13 action=mark-routing new-routing-mark=to_ether11
add chain=prerouting connection-mark=ether11_conn in-interface=ether12 action=mark-routing new-routing-mark=to_ether11
/ip route
add dst-address=0.0.0.0/0 gateway=192.168.3.1 routing-mark=to_ether1 check-gateway=ping
add dst-address=0.0.0.0/0 gateway=192.168.4.1 routing-mark=to_ether2 check-gateway=ping
add dst-address=0.0.0.0/0 gateway=192.168.52.1 routing-mark=to_ether3 check-gateway=ping
add dst-address=0.0.0.0/0 gateway=192.168.60.1 routing-mark=to_ether4 check-gateway=ping
add dst-address=0.0.0.0/0 gateway=10.10.1.1 routing-mark=to_ether5 check-gateway=ping
add dst-address=0.0.0.0/0 gateway=10.10.2.1 routing-mark=to_ether6 check-gateway=ping
add dst-address=0.0.0.0/0 gateway=10.10.3.1 routing-mark=to_ether7 check-gateway=ping
add dst-address=0.0.0.0/0 gateway=10.10.4.1 routing-mark=to_ether8 check-gateway=ping
add dst-address=0.0.0.0/0 gateway=10.10.5.1 routing-mark=to_ether9 check-gateway=ping
add dst-address=0.0.0.0/0 gateway=10.10.6.1 routing-mark=to_ether10 check-gateway=ping
add dst-address=0.0.0.0/0 gateway=10.10.7.1 routing-mark=to_ether11 check-gateway=ping
add dst-address=0.0.0.0/0 gateway=192.168.3.1 distance=1 check-gateway=ping
add dst-address=0.0.0.0/0 gateway=192.168.4.1 distance=2 check-gateway=ping
add dst-address=0.0.0.0/0 gateway=192.168.52.1 distance=3 check-gateway=ping
add dst-address=0.0.0.0/0 gateway=192.168.60.1 distance=4 check-gateway=ping
add dst-address=0.0.0.0/0 gateway=10.10.1.1 distance=5 check-gateway=ping
add dst-address=0.0.0.0/0 gateway=10.10.2.1 distance=6 check-gateway=ping
add dst-address=0.0.0.0/0 gateway=10.10.3.1 distance=7 check-gateway=ping
add dst-address=0.0.0.0/0 gateway=10.10.4.1 distance=8 check-gateway=ping
add dst-address=0.0.0.0/0 gateway=10.10.5.1 distance=9 check-gateway=ping
add dst-address=0.0.0.0/0 gateway=10.10.6.1 distance=10 check-gateway=ping
add dst-address=0.0.0.0/0 gateway=10.10.7.1 distance=11 check-gateway=ping
/ip firewall nat
add chain=srcnat out-interface=ether1 action=masquerade
add chain=srcnat out-interface=ether2 action=masquerade
add chain=srcnat out-interface=ether3 action=masquerade
add chain=srcnat out-interface=ether4 action=masquerade
add chain=srcnat out-interface=ether5 action=masquerade
add chain=srcnat out-interface=ether6 action=masquerade
add chain=srcnat out-interface=ether7 action=masquerade
add chain=srcnat out-interface=ether8 action=masquerade
add chain=srcnat out-interface=ether9 action=masquerade
add chain=srcnat out-interface=ether10 action=masquerade
add chain=srcnat out-interface=ether11 action=masquerade
LikeLike
Comment by Ryan — October 21, 2013 @ 8:26 AM
Sir please help. Is my script correct? There is no traffic comming in or out
LikeLike
Comment by Ryan — October 21, 2013 @ 8:45 AM
Dear Sir,
mey 3 website ko kisi ek wan se hi open karwana chata ho un site’s ki request dosrey wan pe na jae plz guide me, mey apka 4 WAN Load Balancing using PCC method use kar raha ho is k wan3 pe jo line hai us pe all other site k lia off karna hai or bas un 3 site pe use ho or baki 3no wan’s pe ye 3 site’s block ho jain
plz guide me
Thanks
LikeLike
Comment by Ehtisham — October 20, 2013 @ 4:36 PM
Read this
LikeLike
Comment by Syed Jahanzaib / Pinochio~:) — October 21, 2013 @ 8:33 AM
Sir,
Is my posted script correct or wrong?
LikeLike
Comment by Ryan — October 21, 2013 @ 8:39 AM
Ryan,
did your script work?
LikeLike
Comment by Ahmad jamal — October 21, 2013 @ 10:25 PM
no internet connection coming out in ether 13 and 12. thats the port i designated to connect it into LAN
LikeLike
Comment by Ryan — October 22, 2013 @ 10:15 AM
Hi, Thank you for this tip 🙂
I have question, how make MT to know what is our WAN max limit in this scanerio so it wont overload one connection ? for example I have 2x 20/4, should I set it in global tree based on marked connection ?
LikeLike
Comment by Krzysztof — November 2, 2013 @ 6:35 PM
Hi,
I try to run my loadbalancing but without success, stay on WAN1 and do not go on other WAN.
My script:
/ip address
add address=192.168.3.252/24 network=192.168.3.0 broadcast=192.168.0.255 interface=Local
add address=192.168.4.252/24 network=192.168.4.0 broadcast=192.168.1.255 interface=WAN1
add address=192.168.6.252/24 network=192.168.6.0 broadcast=192.168.2.255 interface=WAN2
add address=192.168.7.252/24 network=192.168.7.0 broadcast=192.168.3.255 interface=WAN3
add address=192.168.8.252/24 network=192.168.8.0 broadcast=192.168.4.255 interface=WAN4
/ip firewall mangle
add chain=input in-interface=WAN1 action=mark-connection new-connection-mark=WAN1_conn
add chain=input in-interface=WAN2 action=mark-connection new-connection-mark=WAN2_conn
add chain=input in-interface=WAN3 action=mark-connection new-connection-mark=WAN3_conn
add chain=input in-interface=WAN4 action=mark-connection new-connection-mark=WAN4_conn
add chain=output connection-mark=WAN1_conn action=mark-routing new-routing-mark=to_WAN1
add chain=output connection-mark=WAN2_conn action=mark-routing new-routing-mark=to_WAN2
add chain=output connection-mark=WAN3_conn action=mark-routing new-routing-mark=to_WAN3
add chain=output connection-mark=WAN4_conn action=mark-routing new-routing-mark=to_WAN4
add chain=prerouting dst-address=192.168.4.0/24 action=accept in-interface=Local
add chain=prerouting dst-address=192.168.6.0/24 action=accept in-interface=Local
add chain=prerouting dst-address=192.168.7.0/24 action=accept in-interface=Local
add chain=prerouting dst-address=192.168.8.0/24 action=accept in-interface=Local
add chain=prerouting dst-address-type=!local in-interface=Local per-connection-classifier=both-addresses-and-ports:4/0 action=mark-connection new-connection-mark=WAN1_conn passthrough=yes
add chain=prerouting dst-address-type=!local in-interface=Local per-connection-classifier=both-addresses-and-ports:4/1 action=mark-connection new-connection-mark=WAN2_conn passthrough=yes
add chain=prerouting dst-address-type=!local in-interface=Local per-connection-classifier=both-addresses-and-ports:4/2 action=mark-connection new-connection-mark=WAN3_conn passthrough=yes
add chain=prerouting dst-address-type=!local in-interface=Local per-connection-classifier=both-addresses-and-ports:4/3 action=mark-connection new-connection-mark=WAN4_conn passthrough=yes
add chain=prerouting connection-mark=WAN1_conn in-interface=Local action=mark-routing new-routing-mark=to_WAN1
add chain=prerouting connection-mark=WAN2_conn in-interface=Local action=mark-routing new-routing-mark=to_WAN2
add chain=prerouting connection-mark=WAN3_conn in-interface=Local action=mark-routing new-routing-mark=to_WAN3
add chain=prerouting connection-mark=WAN4_conn in-interface=Local action=mark-routing new-routing-mark=to_WAN4
/ip route
add dst-address=0.0.0.0/0 gateway=192.168.4.250 routing-mark=to_WAN1 check-gateway=ping
add dst-address=0.0.0.0/0 gateway=192.168.6.240 routing-mark=to_WAN2 check-gateway=ping
add dst-address=0.0.0.0/0 gateway=192.168.7.240 routing-mark=to_WAN3 check-gateway=ping
add dst-address=0.0.0.0/0 gateway=192.168.8.240 routing-mark=to_WAN4 check-gateway=ping
add dst-address=0.0.0.0/0 gateway=192.168.4.250 distance=1 check-gateway=ping
add dst-address=0.0.0.0/0 gateway=192.168.6.240 distance=2 check-gateway=ping
add dst-address=0.0.0.0/0 gateway=192.168.7.240 distance=3 check-gateway=ping
add dst-address=0.0.0.0/0 gateway=192.168.8.240 distance=4 check-gateway=ping
/ip firewall nat
add chain=srcnat out-interface=WAN1 action=masquerade
add chain=srcnat out-interface=WAN2 action=masquerade
add chain=srcnat out-interface=WAN3 action=masquerade
add chain=srcnat out-interface=WAN4 action=masquerade
Please help me .
Thx
LikeLike
Comment by gergos — November 20, 2013 @ 10:42 PM
Look at your IP configurations. Mistakes are there.
LikeLike
Comment by Syed Jahanzaib / Pinochio~:) — November 21, 2013 @ 11:22 AM
I just do not see the IP, which is why I am appealing to you.
LikeLike
Comment by gergos — November 21, 2013 @ 5:41 PM
This is exactly the same configuration as your 😦
LikeLike
Comment by gergos — November 21, 2013 @ 6:26 PM
Hi,
I have a trouble in mikrotik and i am sure you will help me out.
My Senario:
—————————————————————————————————————————————————————–
WAN1
—————————————————————————————————————————————————————–
DSL Line Ip =========> A.P 1 ip =========> A.P 2 ip =========> WAN1 in Mikrotik Server
192.168.1.1 192.168.1.3 192.168.1.4
Gateway Gateway
192.168.1.1 192.168.1.1
—————————————————————————————————————————————————————–
WAN2
—————————————————————————————————————————————————————–
DSL Line Ip =========> A.P 1 ip =========> A.P 2 ip =========> WAN2 in Mikrotik Server
192.168.2.1 192.168.2.3 192.168.2.4
Gateway Gateway
192.168.2.1 192.168.2.1
—————————————————————————————————————————————————————–
So as mentioned above I am using this to add WAN1 and WAN2 Lines in Mikrotik Server, When I am using your load balancing scripts, I got successfully login in Hotspot but after login internet in not working….
—————————————————————————————————————————————————————–
/ip address
add address=192.168.0.1/24 network=192.168.0.0 broadcast=192.168.0.255 interface=Local
add address=192.168.1.2/24 network=192.168.1.0 broadcast=192.168.1.255 interface=WAN1
add address=192.168.2.2/24 network=192.168.2.0 broadcast=192.168.2.255 interface=WAN2
/ip firewall mangle
add chain=input in-interface=WAN1 action=mark-connection new-connection-mark=WAN1_conn
add chain=input in-interface=WAN2 action=mark-connection new-connection-mark=WAN2_conn
add chain=output connection-mark=WAN1_conn action=mark-routing new-routing-mark=to_WAN1
add chain=output connection-mark=WAN2_conn action=mark-routing new-routing-mark=to_WAN2
add chain=prerouting dst-address=192.168.1.0/24 action=accept in-interface=Local
add chain=prerouting dst-address=192.168.2.0/24 action=accept in-interface=Local
add chain=prerouting dst-address-type=!local in-interface=Local per-connection-classifier=both-addresses-and-ports:4/0 action=mark-connection new-connection-mark=WAN1_conn passthrough=yes
add chain=prerouting dst-address-type=!local in-interface=Local per-connection-classifier=both-addresses-and-ports:4/1 action=mark-connection new-connection-mark=WAN2_conn passthrough=yes
add chain=prerouting connection-mark=WAN1_conn in-interface=Local action=mark-routing new-routing-mark=to_WAN1
add chain=prerouting connection-mark=WAN2_conn in-interface=Local action=mark-routing new-routing-mark=to_WAN2
/ip route
add dst-address=0.0.0.0/0 gateway=192.168.1.1 routing-mark=to_WAN1 check-gateway=ping
add dst-address=0.0.0.0/0 gateway=192.168.2.1 routing-mark=to_WAN2 check-gateway=ping
add dst-address=0.0.0.0/0 gateway=192.168.1.1 distance=1 check-gateway=ping
add dst-address=0.0.0.0/0 gateway=192.168.2.1 distance=2 check-gateway=ping
/ip firewall nat
add chain=srcnat out-interface=WAN1 action=masquerade
add chain=srcnat out-interface=WAN2 action=masquerade
—————————————————————————————————————————————————————–
Hopefully you can understand my case situation…. looking forward for your kind response….
Thanks & Regards,
LikeLike
Comment by khurrem — November 22, 2013 @ 7:08 PM
AOA, Sir ma ne app ka script same use kia ha lakin net nei chul rha or na ptcl k router access hotay hai.
LikeLike
Comment by Irfan — November 22, 2013 @ 8:14 PM
Hello do you have a script where I need to get all download from WAN1 and all the UPLOAD traffic will flow on WAN2
LikeLike
Comment by DEXLAINE — November 27, 2013 @ 5:10 PM
plz help me i have 4 wans
4+4+4+2
in need good script just merge
thanks 4 u
email : yasser.alrewad@gmail.com
LikeLike
Comment by alrewad — December 5, 2013 @ 4:21 PM
Assalam-o-Alaikum
Respected Syed Jahanzaib Sir,
Sir i need your help, i m using Mikrotik 450GL with 2-wan Loadbalancing Hotpsot Server, m also using windows server 2003 (file sharing). My hotspot is working great but my sharing is not working.
Sir please help me…
Regards,
Anees
LikeLike
Comment by Anees Riaz — December 13, 2013 @ 12:09 PM
what is the error you are getting while accessing your sharing serveR? is it on same subnet as hotspot users?
Have you tried to add it in WALLED GARDEN IP section to bypass?
LikeLike
Comment by Syed Jahanzaib / Pinochio~:) — December 16, 2013 @ 10:46 AM
Actually sir some time like when i restart my server then sharing is working but suddenly after few mints when i access my server from client pc then i can’t access my server, that time i have checked from many clients pc and my personal pc but same result.. but some time when i restart server then a “Generic Host Servicce” error appear on screen…..
LikeLike
Comment by anees506 — December 16, 2013 @ 12:22 PM
and sir i haven’t tried WALLED GARDEN IP section, how can i use this section for bypass?
LikeLike
Comment by anees506 — December 16, 2013 @ 12:24 PM
Aslam-o-Alaikum
Respected Syed Jahanzeb Sir,
Sir me 4WAN load balancing use kar raha ho Router Board 750GL pe me ne 3DSL lagaye he en me se koi bhi DSL modem se jab internet ki problem ajati he to sara system distorb ho jata he masla ye he modem connect hota he lkn net nhi ata. ab koi aisa tariqa batawo k jo bhi modem ping nhi hota usko request na send ho.
Thanks in Advance.
LikeLike
Comment by Maqsood Khan — December 15, 2013 @ 7:17 PM
use failover for pcc.
try this.
https://aacable.wordpress.com/tag/pcc-with-fail-over/
LikeLike
Comment by Syed Jahanzaib / Pinochio~:) — December 16, 2013 @ 10:37 AM
sir.i have 2wan 4mb but 1wan is not work.please check my setting
. i/ip address
add address=192.168.0.1/24 network=192.168.0.0 broadcast=192.168.0.254 interface=Local
add address=192.168.1.2/24 network=192.168.1.0 broadcast=192.168.1.254 interface=WAN1
add address=192.168.2.2/24 network=192.168.2.0 broadcast=192.168.2.254 interface=WAN2
/ip firewall mangle
add chain=input in-interface=WAN1 action=mark-connection new-connection-mark=WAN1_conn passthrough=yes
add chain=input in-interface=WAN2 action=mark-connection new-connection-mark=WAN2_conn passthrough=yes
add chain=output connection-mark=WAN1_conn action=mark-routing new-routing-mark=to_WAN1 passthrough=yes
add chain=output connection-mark=WAN2_conn action=mark-routing new-routing-mark=to_WAN2 passthrough=yes
add chain=prerouting dst-address=192.168.1.0/24 action=accept in-interface=Local passthrough=yes
add chain=prerouting dst-address=192.168.2.0/24 action=accept in-interface=Local passthrough=yes
add chain=prerouting dst-address-type=!local in-interface=Local per-connection-classifier=both-addresses-and-ports:2/0 action=mark-connection new-connection-mark=WAN1_conn passthrough=yes
add chain=prerouting dst-address-type=!local in-interface=Local per-connection-classifier=both-addresses-and-ports:2/1 action=mark-connection new-connection-mark=WAN2_conn passthrough=yes
add chain=prerouting connection-mark=WAN1_conn in-interface=Local action=mark-routing new-routing-mark=to_WAN1 passthrough=yes
add chain=prerouting connection-mark=WAN2_conn in-interface=Local action=mark-routing new-routing-mark=to_WAN2 passthrough=yes
/ip route
add dst-address=0.0.0.0/0 gateway=192.168.1.1 routing-mark=to_WAN1 check-gateway=ping
add dst-address=0.0.0.0/0 gateway=192.168.2.1 routing-mark=to_WAN2 check-gateway=ping
add dst-address=0.0.0.0/0 gateway=192.168.1.1 distance=1 check-gateway=ping
add dst-address=0.0.0.0/0 gateway=192.168.2.1 distance=2 check-gateway=ping
/ip firewall nat
add chain=srcnat out-interface=WAN1 action=masquerade
add chain=srcnat out-interface=WAN2 action=masquerade
LikeLike
Comment by m.abidraza — December 16, 2013 @ 8:09 PM
Is your PCC box configured with some other services too ? like hotspot pppope?
LikeLike
Comment by Syed Jahanzaib / Pinochio~:) — December 17, 2013 @ 9:06 AM
Dear Sir salam,
Need some help on routing job.
Just bought Mikrotik RB2011UAS-RM. Firmware v6.7. RouterBoard 3.10
I’m from a Hotel company (Hospitality)
Hardware/ISP list-
5 x adsl 4mbps – For Guest(need to be combine to get 20mbps)
3 x sdsl 1.5mbps – For Work Stations(need to be combine to get 4.5mbps)
1 x Guest lan (IP add – 10.1.0.0/19)
1 x Work station Lan (IP add – 192.168.1.0/24)
1 x Fortigate 40c firewall(curently running with 2 wan sdsl 1.5mbps for work stations)
I’m currently running on NTH load balancing method and running fine for only guest network.
Was deciding to add 3 sdsl into mikrotik rb2011.
Because of my fortigate only supports up to 2WAN’s,my connection is super snail for work stations, and it couldnt do something like combine bandwith, even it could it’s still slow.
My Current network Infrastructure
5adsl —-> | Mikrotik RB2011 (ether6(GuestLan)) —> | Switch —-> | AP’s network 10.1.0.0/19 (no hotspot running)
2sdsl —-> | Fortigate 40c Firewall (LAN PORT INTERFACE) —> | Switch —-> |Workstation Network 192.168.0.0/24
| Fortigate 40c Firewall (LAN PORT INTERFACE) —> | Domain Server IP (192.168.0.240)
Wanted to change to
5 adsl ———–> | |(ether6(guestLan)) —> | Switch —-> | AP’s network 10.1.0.0/19 (run with hotspot)
3 sdsl ———-> | Mikrotik RB2011 —> |(ether10(workstations)) —> | fortigate (run on transparent mode but firewall policy,etc running) —> | —-> Switch —-> | Workstation’s network 192.168.0.0/24
| |(ether10(workstations)) —-> | fortigate (run on transparent mode but firewall policy,etc running) —> | —-> Domain server for workstation (IP 192.168.0.240)
1st question – would like to know how do i seperate the guest ISP for Guest Lan and Work ISP for Work station?? and No communication for both Network’s.
If after managed to seperate those ISP, will firewall mangle rules for Guest bound together into WorkStation and PCQ for Guest bound into Workstation and mess up together??
My workers here are complaining about slow internet, have solve this quick =.=””
2nd question – For guest network need to add hotspot from RB2011, Can my 5 adsl 20mbps be able to do this kind of service? which means i guarantee for the person who pays for a Higher speed internet gets his speed while other user speed doesnt goes too low.
Thanks very much dear guru, your reply is much appreciated. 🙂
LikeLike
Comment by Nicholas Yan — January 10, 2014 @ 4:10 AM
sorry please allowed me to redraw my infrastructure
Currently using
5 adsl —–> Mikrotik RB2011 (ether6(guestLAN)) ——> Switch —–> AP’s (Network 10.1.0.0/19) not running hotspot
2 sdsl ——> Fortigate 40c Firewall (LAN PORT INTERFACE) —–> Switch —–> Workstation (network 192.168.0.0/24)
————–> Fortigate 40c Firewall (LAN PORT INTERFACE) —–> Domain Server (192.168.0.240)
Wanted to change to
5 adsl ————>Mikrotik RB2011 —-> (ether6(guestLan)) ———-> Switch ———> AP’s network 10.1.0.0/19 (run with hotspot)
3 sdsl ————>Mikrotik RB2011 —-> (ether10(workstations)) —–> Fortigate (run on transparent mode but firewall policy,etc running) —–> Switch —–> Workstation’s network 192.168.0.0/24
——————–>Mikrotik RB2011 —-> (ether10(workstations)) —–> Fortigate (run on transparent mode but firewall policy,etc running) —–> Domain Server (192.168.0.240)
Thanks
LikeLike
Comment by Nicholas Yan — January 10, 2014 @ 4:18 AM
asalam o allaikum,
dear zaib bhai, 4 wan ki load balancing kerne k bad hot spot kase configure karenge?
uski script bataden plz, or pppoe server bhe, same mikrotik server per, jsmain 4 wan ki load blancing hoe hy, ushe main ab mujhy hot spot or pppoe configure ker na khy.. ya jis terhan hot spot configure kert hen as ir is wase he kerna hoga? means pool add, routes main gateway add, firewall main nat rule etc..
waiting for your reply bro
LikeLike
Comment by raheel — January 11, 2014 @ 3:47 PM
Hello, I would like to setup a mikrotik 450g 4 wans, son 4 motorola sb5100 cable modem, these modems provide a public IP.
As much as I do not find any search method works well for me.
Might you send me a script or tell me how to set it up.
billion thanks!
LikeLike
Comment by jon — January 20, 2014 @ 3:59 AM
Well we are improving.
So far I’ve got the settings here:
https://aacable.wordpress.com/2…t-by-zaib/
faults:
– I have the laptop connected to the Local and I have to make the data in tcp / ip hand
192.168.0.4
255.255.255.0
192.168.0.1
8.8.8.8
8.8.4.4
Do not swinging, just download me a wan the second reboot it, random.
any help?
LikeLike
Comment by jon — January 21, 2014 @ 2:09 AM
Hi and thanks for this script.
I’m trying to use it for 2 WANs with dynamic IPs, but no luck. Please help me because i’m dummy in RouterOS )). Here’s the script:
/ip firewall mangle
add chain=input in-interface=WAN_ADSL action=mark-connection new-connection-mark=WAN_ADSL_conn
add chain=input in-interface=WAN_3G action=mark-connection new-connection-mark=WAN_3G_conn
add chain=output connection-mark=WAN_ADSL_conn action=mark-routing new-routing-mark=to_WAN_ADSL
add chain=output connection-mark=WAN_3G_conn action=mark-routing new-routing-mark=to_WAN_3G
add chain=prerouting dst-address=192.168.1.0/24 action=accept in-interface=Local /What to write instead of ips?
add chain=prerouting dst-address=192.168.2.0/24 action=accept in-interface=Local /What to write instead of ips?
add chain=prerouting dst-address-type=!local in-interface=Local per-connection-classifier=both-addresses-and-ports:4/0 action=mark-connection new-connection-mark=WAN_ADSL_conn passthrough=yes
add chain=prerouting dst-address-type=!local in-interface=Local per-connection-classifier=both-addresses-and-ports:4/1 action=mark-connection new-connection-mark=WAN_3G_conn passthrough=yes
add chain=prerouting connection-mark=WAN_ADSL_conn in-interface=Local action=mark-routing new-routing-mark=to_WAN_ADSL
add chain=prerouting connection-mark=WAN_3G_conn in-interface=Local action=mark-routing new-routing-mark=to_WAN_3G
/ip route
add dst-address=0.0.0.0/0 gateway=WAN_ADSL routing-mark=to_WAN_ADSL check-gateway=ping
add dst-address=0.0.0.0/0 gateway=WAN_3G routing-mark=to_WAN_3G check-gateway=ping
add dst-address=0.0.0.0/0 gateway=WAN_ADSL distance=1 check-gateway=ping
add dst-address=0.0.0.0/0 gateway=WAN_3G distance=2 check-gateway=ping
/ip firewall nat
add chain=srcnat out-interface=WAN_ADSL action=masquerade
add chain=srcnat out-interface=WAN_3G action=masquerade
Thank you.
LikeLike
Comment by Max — February 5, 2014 @ 11:41 PM
Just copy and paste, then modifications of addresses and names of ports and working as a charm.
But, i am noticed something:
I have server on LAN, and i am set a port forwarding to the server, but sometime when i try to connect to the server from other place from internet, i get connection timeout in browser of that remote computer, after couple of “refresh” i connect to server.
What do you think is happening.
By the way, on server is running NoIP DUC, because i do not have static IP on my WAN connections.
LikeLike
Comment by Belfegor — February 10, 2014 @ 9:19 PM
is there a way you can help me out with teamviewer? I would like you to help me configure my RB951G for 4 wan load balancing. Thanks. any reply will be deeply appreciated
LikeLike
Comment by Cyril — February 13, 2014 @ 5:58 PM
How this configuration performing if there is multiple LANs, in my case i have 2 WANs a 2 LANs?
LikeLike
Comment by Belfegor — March 1, 2014 @ 4:30 PM
Hi, this is the best on the net… where do you start to learn how to get juice out of the mikrotik?… Any book you recomend?
Regards from Spain
LikeLike
Comment by Robert — March 20, 2014 @ 1:57 PM
LikeLike
Comment by Syed Jahanzaib / Pinochio~:) — March 21, 2014 @ 9:10 AM
Respected SIr,
I need script .
I have 2 WAN, I want ,that at a time one should be activated, but when main WAN get down so automatically second WAN have to on.
I try some of your blogs, Fail over one, but not getting good result please help me out regarding this issue.
thanks
LikeLike
Comment by Rafi — April 25, 2014 @ 7:04 PM
Dear Rafi,
You should read following.
https://aacable.wordpress.com/2013/04/12/mikrotik-multiple-wan-fail-over-scripts/
and go with SCENARIO # 2 (using netwatch script) Its very well tested and works 100%. I deployed at various places and working good so far
LikeLike
Comment by Syed Jahanzaib / Pinochio~:) — April 26, 2014 @ 10:18 AM
Asalam o alaiqum jahanzaib bhai i need help i have 750gl i used it to manage more than 50 users through user manager. user manger works fine on 25 users. then its increases up to 30 newly connected users local area shows limited connectivity.. help me.. plz.. in advance jazakAllah.
LikeLike
Comment by Zohaib Ahmed — April 1, 2014 @ 7:19 AM
rb75- Gl have L4 license which is limited for user manager.
look at here.
http://wiki.mikrotik.com/wiki/Manual:License_levels
LikeLike
Comment by Syed Jahanzaib / Pinochio~:) — April 1, 2014 @ 10:23 AM
dear sir
assalam o alykum
mainy rb750gl main load balancing ki hai 2mb k 2 pkg merge kiye hain jaisy k apki dual wan load balancing ki script hai but local pey wo kisi time 4mb sy ooper jata hai or kabi sirf aik line chalti hai kabi wan1 chalti hai kabi wan2 jab is ko mikrotik k lan card main enter kartey hain to sirf aik he line chalti hai kindly batayen k is issue ka solution kya hai bohat shukria sir
LikeLike
Comment by Kamran Shahzad Janjua — April 7, 2014 @ 11:01 PM
you have to check the PCC config closely. check in mangle if all rules are counting packets.
LikeLike
Comment by Syed Jahanzaib / Pinochio~:) — April 10, 2014 @ 9:48 AM
Hello how do you overcome the problem of 2 WANS with the same gateway? Both WANS are havving pppoe dialer
LikeLike
Comment by charles — April 8, 2014 @ 11:43 AM
I have not tried with same gateway situation, either use two simple cheap routers who dials pppoe client and then use these routers as gateway in your pcc box.
OR try this.
Try defining the outbound interface.
For example replace this.
/ip route
add dst-address=0.0.0.0/0 gateway=1.2.3.4 routing-mark=to_wan-ISP1 check-gateway=ping
add dst-address=0.0.0.0/0 gateway=1.2.3.4 routing-mark=to_wan-ISP2 check-gateway=ping
With following
/ip route
add dst-address=0.0.0.0/0 gateway=1.2.3.4%eth1-ISP routing-mark=to_wan-ISP1 check-gateway=ping
add dst-address=0.0.0.0/0 gateway=1.2.3.4%eth2-ISP routing-mark=to_wan-ISP2 check-gateway=ping
Replace the eth1-ISP with your own wan interface name , use the notation % for sure.
If it works , let me know
LikeLike
Comment by Syed Jahanzaib / Pinochio~:) — April 10, 2014 @ 8:56 AM
This seems to be working. How do we incorporate this to a script so it would automatically put %eth1-ISP in the gateway field
LikeLike
Comment by charles — April 17, 2014 @ 5:57 AM
Sir…………we are Using ptcl modems in BRIDGE mode on this methord
ptcl modem page is not open………..how to solved this issue.
Allah aap ko jaza e khair dey…………Ameen
LikeLike
Comment by Salman — April 14, 2014 @ 10:03 AM
Dear Sir
I Have mikrotik RB750 Router I want to connect 4 dsl with 1 lan can u tell me how can i configure it is it same wan which you give for PC thanks
LikeLike
Comment by Shery Zeribs — April 15, 2014 @ 6:15 AM
yes this script will help you in this case.
LikeLike
Comment by Syed Jahanzaib / Pinochio~:) — April 15, 2014 @ 8:36 AM
hello!
I’ve gotten 4 wans to connect but do not get to join 4 wans and unified by leaving lan, is this possible? thank you!
LikeLike
Comment by jon — April 15, 2014 @ 11:36 AM
Sir if i have RB750GL Router Then Same Script I Use For 4 WAN And 1 Lan And Also Confirm That The Wan And Lan Is Auto Detect The DSL IP And PC IP Thanks
LikeLike
Comment by Shery Zeribs — April 15, 2014 @ 4:04 PM
I inserted your script for my setup and everything is load balancing between 2 WANS. I have multiple subnets running in 4 different ports now load balancing, I modified the script as:
/ip firewall mangle
add chain=input in-interface=WAN1 action=mark-connection new-connection-mark=WAN1_conn
add chain=input in-interface=WAN2 action=mark-connection new-connection-mark=WAN2_conn
add chain=output connection-mark=WAN1_conn action=mark-routing new-routing-mark=to_WAN1
add chain=output connection-mark=WAN2_conn action=mark-routing new-routing-mark=to_WAN2
add chain=prerouting dst-address=192.168.1.0/24 action=accept in-interface=LAN1
add chain=prerouting dst-address=192.168.2.0/24 action=accept in-interface=LAN1
add chain=prerouting dst-address-type=!local in-interface=LAN1 per-connection-classifier=src-address:2/0 action=mark-connection new-connection-mark=WAN1_conn passthrough=yes
add chain=prerouting dst-address-type=!local in-interface=LAN1 per-connection-classifier=src-address:2/1 action=mark-connection new-connection-mark=WAN2_conn passthrough=yes
add chain=prerouting connection-mark=WAN1_conn in-interface=LAN1 action=mark-routing new-routing-mark=to_WAN1
add chain=prerouting connection-mark=WAN2_conn in-interface=LAN1 action=mark-routing new-routing-mark=to_WAN2
add chain=prerouting dst-address=192.168.1.0/24 action=accept in-interface=LAN2
add chain=prerouting dst-address=192.168.2.0/24 action=accept in-interface=LAN2
add chain=prerouting dst-address-type=!local in-interface=LAN2 per-connection-classifier=src-address:2/0 action=mark-connection new-connection-mark=WAN1_conn passthrough=yes
add chain=prerouting dst-address-type=!local in-interface=LAN2 per-connection-classifier=src-address:2/1 action=mark-connection new-connection-mark=WAN2_conn passthrough=yes
add chain=prerouting connection-mark=WAN1_conn in-interface=LAN2 action=mark-routing new-routing-mark=to_WAN1
add chain=prerouting connection-mark=WAN2_conn in-interface=LAN2 action=mark-routing new-routing-mark=to_WAN2
add chain=prerouting dst-address=192.168.1.0/24 action=accept in-interface=LAN3
add chain=prerouting dst-address=192.168.2.0/24 action=accept in-interface=LAN3
add chain=prerouting dst-address-type=!local in-interface=LAN3 per-connection-classifier=src-address:2/0 action=mark-connection new-connection-mark=WAN1_conn passthrough=yes
add chain=prerouting dst-address-type=!local in-interface=LAN3 per-connection-classifier=src-address:2/1 action=mark-connection new-connection-mark=WAN2_conn passthrough=yes
add chain=prerouting connection-mark=WAN1_conn in-interface=LAN3 action=mark-routing new-routing-mark=to_WAN1
add chain=prerouting connection-mark=WAN2_conn in-interface=LAN3 action=mark-routing new-routing-mark=to_WAN2
add chain=prerouting dst-address=192.168.1.0/24 action=accept in-interface=LAN4
add chain=prerouting dst-address=192.168.2.0/24 action=accept in-interface=LAN4
add chain=prerouting dst-address-type=!local in-interface=LAN4 per-connection-classifier=src-address:2/0 action=mark-connection new-connection-mark=WAN1_conn passthrough=yes
add chain=prerouting dst-address-type=!local in-interface=LAN4 per-connection-classifier=src-address:2/1 action=mark-connection new-connection-mark=WAN2_conn passthrough=yes
add chain=prerouting connection-mark=WAN1_conn in-interface=LAN4 action=mark-routing new-routing-mark=to_WAN1
add chain=prerouting connection-mark=WAN2_conn in-interface=LAN4 action=mark-routing new-routing-mark=to_WAN2
It is working! Not sure if there is an easier method?
The one thing I have noticed after the Load Balance is that I no longer have access to the different networks. I am unable to access servers between the different subnets. Please advise what I must do. If I disable the mangle rules, I can access the different subnets, once enabled, I lose that ability.
Thanks in advance.
LikeLike
Comment by Mario — April 17, 2014 @ 5:25 PM
Mario veo que controlas, necesito ayuda, tengo 4 wans que quiero sacar por una lan, tengo la configuracion y cunsigo que las 4 vayan pero no consigo hacer que se sume la velocidad por la LAN, solo se me conecta el router por una de las WANS…
Thks!
LikeLike
Comment by jon — April 19, 2014 @ 9:15 PM
sir mere pass facebook ke elawa koi wabsite open nahe ho rahi hai mikrotic server lagane ke bad plz help me or sab set chal raha hai
LikeLike
Comment by shadab hussain — April 30, 2014 @ 1:08 AM
Reblogged this on weera00.
LikeLike
Comment by weera00 — May 17, 2014 @ 12:55 PM
Hi. After so many tries to get LB working with all your configs, this did the trick! Thanks for this! I wanted to ask few questions…
1. I configured my RB750 for 2 WAN ports and one LAN and its working, but when I’m downloading something it doesn’t go full speed. I have 2×15 Mbits and it only goes about 20-23 Mbits. Maybe this is maximum for RB750 or theres something else going on because CPU usage is 15-25% and theres always around 12MB of RAM free…
2. I wanted to add one more WAN (again 15 Mbits) but then just 2 of 3 works (1 and 3) and sometimes just one (3). I’m going to play more with this but if you have any suggestion… Maybe again its hardware related or something to do with right pcc numbers. I tried 3/0, 3/1, 3/2. I looked a little about this and it needs to be diferente number for each WAN to work, example: WAN1 0/3=0, WAN2 1/3=0.33=again 0 bacause it below 0.5 and WAN3 2/3=0.66=1 because its above 0.5. If this is true then I ned to configure it diferently so that my result is 0, 1, 2… right? I’ll play with this and report what happens…
Thanks in advance
LikeLike
Comment by Viktor — May 22, 2014 @ 4:17 PM
Nader szałowy post, badawcze teksty polecam wszystkim literaturę
LikeLike
Comment by systemy call center — June 4, 2014 @ 5:02 AM
Sir Syed Jahanzaib !
salam !
i have two connection of wan one is DSL and the other one is the fiber optic connection. i want to merge both connection to get the double bandwidth and also have to do fail-over can you do it for me via team-viewer, as i am newbie to the mikrotik i need your help please !
And this will also be a great chance for to learn something 🙂
LikeLike
Comment by Ismail khan — June 4, 2014 @ 10:52 AM
Tried this config on my RB750 with 4x15MB/s links and only 2 are working correctly, other 2 idle, and maximum speed that I managed to get is 25-27MB/s. Any idea? RB limit?
LikeLike
Comment by ViktorX — June 16, 2014 @ 1:29 AM
Hello,
can anybody help me why network WAN network id and dst-address id is same? through this configuration net is not working. but when i use in dst-address id is 0.0.0.0/24 net is working fine.
Kindly pin out where is i am wrong. Thanks
/ip address
add address=192.168.0.1/24 network=192.168.0.0 broadcast=192.168.0.255 interface=Local
add address=192.168.1.2/24 network=192.168.1.0 broadcast=192.168.1.255 interface=WAN1
add address=192.168.2.2/24 network=192.168.2.0 broadcast=192.168.2.255 interface=WAN2
/ip firewall mangle
add chain=input in-interface=WAN1 action=mark-connection new-connection-mark=WAN1_conn
add chain=input in-interface=WAN2 action=mark-connection new-connection-mark=WAN2_conn
add chain=output connection-mark=WAN1_conn action=mark-routing new-routing-mark=to_WAN1
add chain=output connection-mark=WAN2_conn action=mark-routing new-routing-mark=to_WAN2
add chain=prerouting dst-address=192.168.1.0/24 action=accept in-interface=Local
add chain=prerouting dst-address=192.168.2.0/24 action=accept in-interface=Local
LikeLike
Comment by Wasim — June 16, 2014 @ 9:27 PM
Reblogged this on Jrojo's Blog and commented:
Una passada de Script per a balancejar 4 ADSL
LikeLike
Comment by jrojoal — June 16, 2014 @ 11:41 PM
Hi, very nice script! Thanks for that!
Basic stuff works, but banking sites don’t …
I replaced the classifier with src address, but it still disconnects when visiting banking sites.
It came to my attention that this doesn’t happen when I disable the passthrough in the line where the classifier is set.
I can’t seem to find any explanation about the need for passthrough to be enabled here?
Why doesn’t it just keep the connection sticky when src address is used ?
Thanks again 🙂
LikeLike
Comment by Joris — July 19, 2014 @ 10:47 PM
/ip address
add address=192.168.1.1/24 network=192.168.1.0 broadcast=192.168.1.255 interface=WLAN
add address=192.168.2.1/24 network=192.168.2.0 broadcast=192.168.2.255 interface=Local-1
add address=192.168.3.1/24 network=192.168.3.0 broadcast=192.168.3.255 interface=Local-2
add address=192.168.4.2/24 network=192.168.4.0 broadcast=192.168.4.255 interface=WAN1
add address=192.168.5.2/24 network=192.168.5.0 broadcast=192.168.5.255 interface=WAN2
add address=192.168.6.2/24 network=192.168.6.0 broadcast=192.168.6.255 interface=WAN3
/ip firewall mangle
add chain=input in-interface=WAN1 action=mark-connection new-connection-mark=WAN1_conn
add chain=input in-interface=WAN2 action=mark-connection new-connection-mark=WAN2_conn
add chain=input in-interface=WAN3 action=mark-connection new-connection-mark=WAN3_conn
add chain=output connection-mark=WAN1_conn action=mark-routing new-routing-mark=to_WAN1
add chain=output connection-mark=WAN2_conn action=mark-routing new-routing-mark=to_WAN2
add chain=output connection-mark=WAN3_conn action=mark-routing new-routing-mark=to_WAN3
add chain=prerouting dst-address=192.168.4.0/24 action=accept in-interface=Local-1
add chain=prerouting dst-address=192.168.5.0/24 action=accept in-interface=Local-1
add chain=prerouting dst-address=192.168.6.0/24 action=accept in-interface=Local-1
add chain=prerouting dst-address-type=!local in-interface=Local-1 per-connection-classifier=both-addresses-and-ports:3/0 action=mark-connection new-connection-mark=WAN1_conn passthrough=yes
add chain=prerouting dst-address-type=!local in-interface=Local-1 per-connection-classifier=both-addresses-and-ports:3/1 action=mark-connection new-connection-mark=WAN2_conn passthrough=yes
add chain=prerouting dst-address-type=!local in-interface=Local-1 per-connection-classifier=both-addresses-and-ports:3/2 action=mark-connection new-connection-mark=WAN3_conn passthrough=yes
add chain=prerouting connection-mark=WAN1_conn in-interface=Local-1 action=mark-routing new-routing-mark=to_WAN1
add chain=prerouting connection-mark=WAN2_conn in-interface=Local-1 action=mark-routing new-routing-mark=to_WAN2
add chain=prerouting connection-mark=WAN3_conn in-interface=Local-1 action=mark-routing new-routing-mark=to_WAN3
/ip route
add dst-address=0.0.0.0/0 gateway=192.168.4.1 routing-mark=to_WAN1 check-gateway=ping
add dst-address=0.0.0.0/0 gateway=192.168.5.1 routing-mark=to_WAN2 check-gateway=ping
add dst-address=0.0.0.0/0 gateway=192.168.6.1 routing-mark=to_WAN3 check-gateway=ping
add dst-address=0.0.0.0/0 gateway=192.168.4.1 distance=1 check-gateway=ping
add dst-address=0.0.0.0/0 gateway=192.168.5.1 distance=2 check-gateway=ping
add dst-address=0.0.0.0/0 gateway=192.168.6.1 distance=3 check-gateway=ping
/ip firewall nat
add chain=srcnat out-interface=WAN1 action=masquerade
add chain=srcnat out-interface=WAN2 action=masquerade
add chain=srcnat out-interface=WAN3 action=masquerade
/ip dns
set allow-remote-requests=yes cache-max-ttl=1w cache-size=5000KiB max-udp-packet-size=512 servers=217.218.127.127,8.8.8.8
pleaz chek it and tell me this is right???
LikeLike
Comment by soroush shakhsi — August 18, 2014 @ 6:16 AM
[…] : aacable + wiki.mikrotik.com + mikrotik.co.id + […]
LikeLike
Pingback by Load Balancing 2 ISP Dengan PCC Mikrotik | bodi — August 20, 2014 @ 2:40 PM
goodmorning
I need your help to setup my microtik rb750 . i have 3 adsl with port forwarding rules . Kinldy contact me . Paypal donation is available
LikeLike
Comment by Nick Tsif — August 21, 2014 @ 12:40 PM
Example:
10.0.0.1 = Web Server (or any other required server on LAN)
3389/tcp = RDP port
First, the NAT rules:
Code:
/ip firewall nat
add chain=dstnat action=dst-nat in-interface=WAN1 dst-address=YOUR_WAN1_IP dst-port=3389 to-address=10.0.0.1
add chain=dstnat action=dst-nat in-interface=WAN2 dst-address=YOUR_WAN2_IP dst-port=3389 to-address=10.0.0.1
Now, mark all connections coming into WAN1 as such, do the same for WAN2:
Code:
/ip firewall mangle
add chain=prerouting in-interface=WAN1 action=mark-connection new-connection-mark=WAN1_connection
add chain=prerouting in-interface=WAN1 action=mark-connection new-connection-mark=WAN2_connection
Set routing marks for all packets in those connections that come in from the LAN and go back out to the internet:
Code:
/ip firewall mangle
add chain=prerouting in-interface=LAN connection-mark=WAN1_connection action=mark-routing new-routing-mark=to_WAN1
add chain=prerouting in-interface=LAN connection-mark=WAN2_connection action=mark-routing new-routing-mark=to_WAN2
And lastly install some routes that fire for those routing marks to make sure the packets go back out the right pipe:
Code:
/ip route
add dst-address=0.0.0.0/0 routing-mark=to_WAN1 gateway=YOUR_WAN_GARTEWAY
add dst-address=0.0.0.0/0 routing-mark=to_WAN2 gateway=YOUR_WAN_GARTEWAY
LikeLike
Comment by Syed Jahanzaib / Pinochio~:) — August 21, 2014 @ 2:43 PM
Dear Mr. Syed Jahanzaib,
Thank you for your blog everything here is very useful for me.
Regards,
Ahmed Salah
Egypt
LikeLike
Comment by Ahmed Salah — September 1, 2014 @ 9:32 PM
Dear Jahanzaib Sir,
I have two WAN Links
WAN1=203.80.130.74, 255.2555.255,252, DGW=203.80.130.73, DNS-203.80.130.1
WAN2 = DSL Model 10.92.4.2
please advise me how can configure failover router.
Regards
Abdul Wahab
Sukkur
LikeLike
Comment by Abdul Wahab — September 6, 2014 @ 10:12 AM
teen
Mikrotik 4 WAN Load Balancing using PCC method. Complete Script ! by zaiB | Syed Jahanzaib Personnel Blog to Share Knowledge !
LikeLike
Trackback by teen — September 11, 2014 @ 12:31 PM
i have 2 pppoe connection in one router from one isp .. can i use frome this command..?
or where should i change the commands..?
thanks a lot
LikeLike
Comment by sdb — September 15, 2014 @ 3:51 PM
hi sir i have 5.20
i am running already 4 lines of ptcl on routing mode now i have a problem that net is not working on routing mode in the modem therefor i configure the modem on bridge mode but when i configure the mikrotik on bridge mode only one line works others are not working i want that all lines are work with bridge mode plz help me
LikeLike
Comment by ijaz — October 9, 2014 @ 1:00 PM
mr sayed : alslam alekm : At first I apologize for my poor English i have 5.26 on 750 gl board and When used your script The merger is not correctly And this is my lines data
first line 192.168.1.254 isp data is
IP Address 195.140.178.67
IP Subnet Mask 255.255.255.255
Gateway IP Address 195.140.30.1
Second Line 192.168.2.1 isp data is
IP Address 195.160.153.192
IP Subnet Mask 255.255.255.255
Gateway IP Address 195.140.30.1
Third Line 192.168.3.1 isp data is
IP Address 195.140.158.154
IP Subnet Mask 255.255.255.255
Gateway IP Address 195.140.30.1
Fourth Line 192.168.4.1 isp data is
IP Address 195.140.154.147
IP Subnet Mask 255.255.255.255
Gateway IP Address 195.140.30.1
Please help in Load Balance of these lines
LikeLike
Comment by amgad — December 2, 2014 @ 5:46 PM
hI Bro, I am using your script with Dual Wan PCC and is working great.
WAN1 = 213.14.14.0/23 (BGP) with ISP1
WAN2 = 41.41.41.0/28 Static with ISP2
I have noticed that i can reach dns of my peer (WAN1) from the MT router however i cannot reach peer dns from users side(LAN).
NB: Peer dns is reachable (pingable) from ISP2.
please advice
LikeLike
Comment by Landi Ahmed — December 3, 2014 @ 4:28 PM
pls i need Script Integration pcc for 3 lines 2M (2M+2M+2M) on routerbored 750
LikeLike
Comment by HEMA — December 6, 2014 @ 5:54 AM
Hello Sir,
I have Mikrotik 750GL & TP Link 470+ completely new to the Setup, have read most of posts and replies, have Question after trying both. but not sure if this blog is till active. will be grateful if you can respond so i can post my issues. your help will be like fortune for me.
JAZAK ALLAH
LikeLike
Comment by Hasham Wahaib — December 18, 2014 @ 4:57 AM
What issue you are facing ?
LikeLike
Comment by Syed Jahanzaib / Pinochio~:) — December 29, 2014 @ 9:16 AM
Thank you very much for your walk-through. It has been extremely helpful! 🙂 I was wondering if you could help me set up our RB1100ahx2 to load balance 8 ADSL lines. I realize that the script is much the same as the one you showed us for 4 WANs, but the RB1100 has 2 different switch groups (ether1-5 and ether6-10) and I do not know how to get all 10 ports on the same group (bridging maybe), so that my router can take advantage of the additional WANs. I am currently using ether11 as my Local port and 2-5 was WAN ports. I want to add 4 more WANs now. Thank you very very much in advance!
LikeLike
Comment by Ing Guadalupe — December 26, 2014 @ 6:25 AM
you can simply remove grouping and use every port as individual (by not using master port). then add the addition appropriate rules to accommodate additional wan links.
LikeLike
Comment by Syed Jahanzaib / Pinochio~:) — December 29, 2014 @ 9:14 AM
Hello,
I configured the script for my mikrotik (1 LAN, 2 ADSL WANs).
It seems traffic goes over WAN1 only.
If I turn off WAN1 router, then traffic finally goes through WAN2
Have you please some pointers in debugging that sort of troubles?
LikeLike
Comment by Francesco — January 21, 2015 @ 3:19 PM
i’ve just seen one of my default routes (WAN2) is not active, is that normal for this configuration?
0 A S 0.0.0.0/0 10.10.0.1 1
1 A S 0.0.0.0/0 192.168.0.1 1
2 A S 0.0.0.0/0 10.10.0.1 1
3 S 0.0.0.0/0 192.168.0.1 2
LikeLike
Comment by Francesco — January 21, 2015 @ 3:37 PM
Hi,
i have 4 internet connections per Connection Speed 8 Mbps, how to equal balance with mikrotik.? please send me configuration thanks
LikeLike
Comment by faixii — February 6, 2015 @ 5:50 PM
Hi. I’m attempting to get your script to work in my scenario.. However i have two VLANS for Office users and Guest Users and want to share 5 connections and make sure that under heavy load that the office users don’t see degradation in service….is that possible
LikeLike
Comment by Kevin Davis — February 11, 2015 @ 4:55 AM
I have 4 wan connection from same ISP .4 mbps of each.my ISP give dynamic IP in ppoe dialing.I want to combine these connections. How to do with dynamic IP.
LikeLike
Comment by shailendraparmar — February 19, 2015 @ 9:12 PM
My Muslim Brother Sayed
Aslam Alikom Wa Rahmtullah
I follow you complete PCC script and it’s very clear
I have Q, how can I define WAN1 for browsing only not for streaming or download ?? for advance I need to route HTML extension like “png,jpg,html.xhtml,php,sql”. etc. from Layer7
Thanks
LikeLike
Comment by akha666 — March 6, 2015 @ 5:20 PM
Hello Brother Syed,
This is Nahid From Bangladesh, Need help from you about Load Balancing problem, I merged to ISP Connection together (WAN1 & WAN2), Where Internet Packet is working together no problem, Also Youtube Packets passing together in both WAN port, But problem is that both ISP have there own FTP server, Online TV, & Movie Server, After merging bandwidth I cant access WAN2 ISPs FTP sites, its show :
“Forbidden
You don’t have permission to access / on this server.
Additionally, a 404 Not Found error was encountered while trying to use an ErrorDocument to handle the request.””
IF i disable WAN1 for few time then WAN2 FTP sites working fine, I tried “Mark Route” with Dst.Address list ip to pass with Only WAN2. In this process its also not working, If i simple disable WAN1 then again WAN2 FTP sites start work, But i need both ISP s FTP site for my users, Please brother help me how to solve this issue, waiting for your response its urgent,
LikeLike
Comment by Nahidul Islam — April 10, 2015 @ 3:14 PM
@nahid,
in your mangle section, put at the top this:
add action=accept chain=prerouting disabled=no dst-address=1.1.1.1 (Replace this ip with Your ISP Sharing Server IP Address)With the command above you will exclude traffic designated for that address from the PCC, it will just pass through the mangle without adding and mark…
and then put static route for that ip to go through WAN1:
ip route add dst-address=1.1.1.1/32 gateway=x.x.x.x WAN1check n let me know
LikeLike
Comment by Syed Jahanzaib / Pinochio~:) — April 14, 2015 @ 11:58 AM
Hi, can you check this script?
the first 4 WAN is 7/1mbps and the Last WAN is 20/2mbps….
all right but the speed test is ever less than 8/1.2…..
/interface bridge
add name=LAN_BR
/interface ethernet
set [ find default-name=ether1 ] name=ether1_WAN1
set [ find default-name=ether2 ] name=ether2_WAN2
set [ find default-name=ether3 ] name=ether3_WAN3
set [ find default-name=ether4 ] name=ether4_WAN4
set [ find default-name=ether5 ] name=ether5_WAN5
/ip pool
add name=dhcp_pool_LAN ranges=192.168.0.100-192.168.0.199
/ip dhcp-server
add address-pool=dhcp_pool_LAN disabled=no interface=LAN_BR name=dhcp_LAN
/interface bridge port
add bridge=LAN_BR interface=ether9
add bridge=LAN_BR interface=ether10
add bridge=LAN_BR interface=ether8
add bridge=LAN_BR interface=ether7
/ip address
add address=192.168.88.1/24 comment=”default managed configuration” \
interface=ether13 network=192.168.88.0
add address=10.0.1.10/24 interface=ether1_WAN1 network=10.0.1.0
add address=10.0.2.10/24 interface=ether2_WAN2 network=10.0.2.0
add address=10.0.3.10/24 interface=ether3_WAN3 network=10.0.3.0
add address=10.0.4.10/24 interface=ether4_WAN4 network=10.0.4.0
add address=10.0.5.10/24 interface=ether5_WAN5 network=10.0.5.0
add address=192.168.0.1/24 interface=LAN_BR network=192.168.0.0
/ip dhcp-server network
add address=192.168.0.0/24 dns-server=192.168.0.1 gateway=192.168.0.1
/ip dns
set allow-remote-requests=yes cache-size=5000KiB max-udp-packet-size=512 \
servers=8.8.4.4,8.8.8.8
/ip firewall mangle
add action=mark-connection chain=input in-interface=ether1_WAN1 \
new-connection-mark=WAN1_conn passthrough=no
add action=mark-connection chain=input in-interface=ether2_WAN2 \
new-connection-mark=WAN2_conn passthrough=no
add action=mark-connection chain=input in-interface=ether3_WAN3 \
new-connection-mark=WAN3_conn passthrough=no
add action=mark-connection chain=input in-interface=ether4_WAN4 \
new-connection-mark=WAN4_conn passthrough=no
add action=mark-connection chain=input in-interface=ether5_WAN5 \
new-connection-mark=WAN5_conn passthrough=no
add action=mark-routing chain=output connection-mark=WAN1_conn \
new-routing-mark=to_WAN1 passthrough=no
add action=mark-routing chain=output connection-mark=WAN2_conn \
new-routing-mark=to_WAN2 passthrough=no
add action=mark-routing chain=output connection-mark=WAN3_conn \
new-routing-mark=to_WAN3 passthrough=no
add action=mark-routing chain=output connection-mark=WAN4_conn \
new-routing-mark=to_WAN4 passthrough=no
add action=mark-routing chain=output connection-mark=WAN5_conn \
new-routing-mark=to_WAN5 passthrough=no
add chain=prerouting dst-address=10.0.1.0/24 in-interface=LAN_BR
add chain=prerouting dst-address=10.0.2.0/24 in-interface=LAN_BR
add chain=prerouting dst-address=10.0.3.0/24 in-interface=LAN_BR
add chain=prerouting dst-address=10.0.4.0/24 in-interface=LAN_BR
add chain=prerouting dst-address=10.0.5.0/24 in-interface=LAN_BR
add action=mark-connection chain=prerouting dst-address-type=!local \
in-interface=LAN_BR new-connection-mark=WAN1_conn \
per-connection-classifier=both-addresses-and-ports:6/0
add action=mark-connection chain=prerouting dst-address-type=!local \
in-interface=LAN_BR new-connection-mark=WAN2_conn \
per-connection-classifier=both-addresses-and-ports:6/5
add action=mark-connection chain=prerouting dst-address-type=!local \
in-interface=LAN_BR new-connection-mark=WAN3_conn \
per-connection-classifier=both-addresses-and-ports:6/2
add action=mark-connection chain=prerouting dst-address-type=!local \
in-interface=LAN_BR new-connection-mark=WAN4_conn \
per-connection-classifier=both-addresses-and-ports:6/3
add action=mark-connection chain=prerouting dst-address-type=!local \
in-interface=LAN_BR new-connection-mark=WAN5_conn \
per-connection-classifier=both-addresses-and-ports:6/4
add action=mark-connection chain=prerouting dst-address-type=!local \
in-interface=LAN_BR new-connection-mark=WAN5_conn \
per-connection-classifier=both-addresses-and-ports:6/1
add action=mark-routing chain=prerouting connection-mark=WAN1_conn \
in-interface=LAN_BR new-routing-mark=to_WAN1
add action=mark-routing chain=prerouting connection-mark=WAN2_conn \
in-interface=LAN_BR new-routing-mark=to_WAN2
add action=mark-routing chain=prerouting connection-mark=WAN3_conn \
in-interface=LAN_BR new-routing-mark=to_WAN3
add action=mark-routing chain=prerouting connection-mark=WAN4_conn \
in-interface=LAN_BR new-routing-mark=to_WAN4
add action=mark-routing chain=prerouting connection-mark=WAN5_conn \
in-interface=LAN_BR new-routing-mark=to_WAN5
/ip firewall nat
add action=masquerade chain=srcnat comment=”masquerade LAN network” \
src-address=192.168.0.0/24
add action=masquerade chain=srcnat comment=”masquerade WAN1 network” \
out-interface=ether1_WAN1
add action=masquerade chain=srcnat comment=”masquerade WAN2 network” \
out-interface=ether2_WAN2
add action=masquerade chain=srcnat comment=”masquerade WAN3 network” \
out-interface=ether3_WAN3
add action=masquerade chain=srcnat comment=”masquerade WAN4 network” \
out-interface=ether4_WAN4
add action=masquerade chain=srcnat comment=”masquerade WAN5 network” \
out-interface=ether5_WAN5
/ip route
add distance=1 gateway=172.16.1.1 routing-mark=to_WAN1
add distance=1 gateway=172.16.2.1 routing-mark=to_WAN2
add distance=1 gateway=172.16.3.1 routing-mark=to_WAN3
add distance=1 gateway=172.16.4.1 routing-mark=to_WAN4
add distance=1 gateway=172.16.5.1 routing-mark=to_WAN5
add check-gateway=ping distance=1 gateway=208.67.220.220 scope=10
add check-gateway=ping distance=1 gateway=208.67.220.222 scope=10
add distance=1 gateway=172.16.5.1 scope=10
add check-gateway=ping distance=1 gateway=208.67.222.220 scope=10
add check-gateway=ping distance=1 gateway=208.67.222.222 scope=10
add check-gateway=ping distance=1 gateway=208.67.220.123 scope=10
add distance=2 gateway=172.16.4.1 scope=10
add distance=3 gateway=172.16.3.1 scope=10
add distance=4 gateway=172.16.2.1 scope=10
add distance=5 gateway=172.16.1.1 scope=10
add check-gateway=ping distance=1 dst-address=172.16.1.1/32 gateway=\
208.67.220.220 scope=10
add check-gateway=ping distance=1 dst-address=172.16.2.1/32 gateway=\
208.67.220.222 scope=10
add check-gateway=ping distance=1 dst-address=172.16.3.1/32 gateway=\
208.67.222.220 scope=10
add check-gateway=ping distance=1 dst-address=172.16.4.1/32 gateway=\
208.67.222.222 scope=10
add check-gateway=ping distance=1 dst-address=172.16.5.1/32 gateway=\
208.67.220.123 scope=10
add distance=1 dst-address=208.67.220.123/32 gateway=10.0.5.1 scope=10
add distance=1 dst-address=208.67.220.220/32 gateway=10.0.1.1 scope=10
add distance=1 dst-address=208.67.220.222/32 gateway=10.0.2.1 scope=10
add distance=1 dst-address=208.67.222.220/32 gateway=10.0.3.1 scope=10
add distance=1 dst-address=208.67.222.222/32 gateway=10.0.4.1 scope=10
/ip upnp
set allow-disable-external-interface=yes
/system clock
set time-zone-name=Europe/Rome
/system ntp client
set enabled=yes primary-ntp=193.204.114.232 secondary-ntp=193.204.114.233
/system scheduler
add interval=1d name=”schedule_reboot_one_day” on-event=\
“system reboot” policy=\
ftp,reboot,read,write,policy,test,password,sniff,sensitive start-date=\
jan/01/1970 start-time=03:00:00
LikeLike
Comment by m4 — April 12, 2015 @ 5:44 AM
Salve
Ho un problema :
Le adsl sono 40 a 30/3Mb e uso un CCR a 12 porte lan.
eth1 è Local Port , ports eth2..eth12, sono le WAN.
Indirizzi ip su eth2, rinominata WAN_00-03 sono:
1) 192.168.200.xx/24 on WAN_00-03 (ex eth2)
2) 192.168.201.xx/24 on WAN_00-03 (ex eth2)
3) 192.168.202.xx/24 on WAN_00-03 (ex eth2)
4) 192.168.204.xx/24 on WAN_00-03 (ex eth2).
indirizzi ip su eth3, rinominata WAN_04-07 sono:
1) 192.168.205.xx/24 on WAN_04-07 (ex eth3)
2) 192.168.206.xx/24 on WAN_04-07 (ex eth3)
eccetera …
…
…
1) 192.168.236.xx/24 on WAN_36-39 (ex eth11)
2) 192.168.237.xx/24 on WAN_36-39 (ex eth11)
3) 192.168.238.xx/24 on WAN_36-39 (ex eth11)
4) 192.168.239.xx/24 on WAN_36-39 (ex eth11)
1) 192.168.240.xx/24 on WAN_40-43 (ex eth12 non usate al momento)
2) 192.168.241.xx/24 on WAN_40-43 (ex eth12 non usate al momento)
ti chiedo se è possibile realizzare un bilanciatore PCC in queste condizioni.
grazie
LikeLike
Comment by Salvatore Palermo — April 26, 2015 @ 1:39 AM
in english
hi
I have a problem:
The ADSL are 40 to 30 / 3Mb and use a CCR 12-port LAN.
eth1 is Local Port, eth2..eth12 ports are the WAN.
Ip addresses on eth2, renamed WAN_00-03 are:
1) 192.168.200.xx / 24 on WAN_00-03 (ex eth2)
2) 192.168.201.xx / 24 on WAN_00-03 (ex eth2)
3) 192.168.202.xx / 24 on WAN_00-03 (ex eth2)
4) 192.168.204.xx / 24 on WAN_00-03 (ex eth2).
ip addresses on eth3, renamed WAN_04-07 are:
1) 192.168.205.xx / 24 on WAN_04-07 (ex eth3)
2) 192.168.206.xx / 24 on WAN_04-07 (ex eth3)
etc …
…
…
1) 192.168.236.xx / 24 on WAN_36-39 (ex eth11)
2) 192.168.237.xx / 24 on WAN_36-39 (ex eth11)
3) 192.168.238.xx / 24 on WAN_36-39 (ex eth11)
4) 192.168.239.xx / 24 on WAN_36-39 (ex eth11)
1) 192.168.240.xx / 24 on WAN_40-43 (ex eth12 not used at the time)
2) 192.168.241.xx / 24 on WAN_40-43 (ex eth12 not used at the time)
I ask if it is possible to realize a balancer PCC in these conditions.
thanks
LikeLike
Comment by Salvatore Palermo — April 26, 2015 @ 1:41 AM
sir 2 pptp server ek lan pe chal sakhte hain kiyaa
LikeLike
Comment by shani — May 20, 2015 @ 2:02 AM
matlab ek fariya ka pptp ho or dosra
mein apna server laga ke ek he lan pe 2 pptp chal jain
LikeLike
Comment by shani — May 20, 2015 @ 2:04 AM
add chain=prerouting dst-address-type=!local in-interface=Local per-connection-classifier=both-addresses-and-ports:2/0 action=mark-connection new-connection-mark=WAN1_conn passthrough=yes
sir app ic command ka imge upload kar skty hain mujy (dst-address-type=!local in-interface=Loca) clear nahi ho raha
LikeLike
Comment by sahir — August 27, 2015 @ 12:18 AM
plz send me ur contact number 03415549350
LikeLike
Comment by safdar — October 11, 2015 @ 7:45 PM
4WAN PPPOE Loadblance 1 Lan
/interface ethernet
set [ find default-name=ether5 ] name=Local
set [ find default-name=ether1 ] name=WAN1
set [ find default-name=ether2 ] name=WAN2
set [ find default-name=ether3 ] name=WAN3
set [ find default-name=ether4 ] name=WAN4
/interface pppoe-client
add disabled=no interface=WAN1 max-mru=1480 max-mtu=1480 name=PPPOE1
add disabled=no interface=WAN2 max-mru=1480 max-mtu=1480 name=PPPOE2
add disabled=no interface=WAN3 max-mru=1480 max-mtu=1480 name=PPPOE3
add disabled=no interface=WAN4 max-mru=1480 max-mtu=1480 name=PPPOE4
/interface wireless
set [ find default-name=wlan1 ] disabled=no mode=ap-bridge ssid=ABS
/ip neighbor discovery
set PPPOE1 discover=no
set PPPOE2 discover=no
set PPPOE3 discover=no
set PPPOE4 discover=no
/interface wireless security-profiles
set [ find default=yes ] supplicant-identity=MikroTik
/ip ipsec proposal
set [ find default=yes ] enc-algorithms=3des
/ip pool
add name=dhcp_pool1 ranges=192.168.24.2-192.168.24.254
/ip dhcp-server
add add-arp=yes address-pool=dhcp_pool1 disabled=no interface=Local lease-time=3d name=dhcp1
/tool user-manager customer
set admin access=own-routers,own-users,own-profiles,own-limits,config-payment-gw
/ip address
add address=192.168.24.1/24 interface=Local network=192.168.24.0
/ip dhcp-server network
add address=192.168.24.0/24 gateway=192.168.24.1
/ip dns
set allow-remote-requests=yes cache-size=5000KiB max-udp-packet-size=5000 servers=8.8.8.8,8.8.4.4
/ip firewall mangle
# b1 not ready
add action=mark-connection chain=input in-interface=PPPOE1 new-connection-mark=in1_conn
# b2 not ready
add action=mark-connection chain=input in-interface=PPPOE2 new-connection-mark=in2_conn
# b3 not ready
add action=mark-connection chain=input in-interface=PPPOE3 new-connection-mark=in3_conn
# b4 not ready
add action=mark-connection chain=input in-interface=PPPOE4 new-connection-mark=in4_conn
add action=mark-routing chain=output connection-mark=in1_conn new-routing-mark=in1
add action=mark-routing chain=output connection-mark=in2_conn new-routing-mark=in2
add action=mark-routing chain=output connection-mark=in3_conn new-routing-mark=in3
add action=mark-routing chain=output connection-mark=in4_conn new-routing-mark=in4
add action=mark-connection chain=prerouting dst-address-type=!local in-interface=Local new-connection-mark=in1_conn per-connection-classifier=both-addresses-and-ports:9/0
add action=mark-connection chain=prerouting dst-address-type=!local in-interface=Local new-connection-mark=in2_conn per-connection-classifier=both-addresses-and-ports:9/1
add action=mark-connection chain=prerouting dst-address-type=!local in-interface=Local new-connection-mark=in3_conn per-connection-classifier=both-addresses-and-ports:9/2
add action=mark-connection chain=prerouting dst-address-type=!local in-interface=Local new-connection-mark=in4_conn per-connection-classifier=both-addresses-and-ports:9/3
add action=mark-routing chain=prerouting connection-mark=in1_conn in-interface=Local new-routing-mark=in1
add action=mark-routing chain=prerouting connection-mark=in2_conn in-interface=Local new-routing-mark=in2
add action=mark-routing chain=prerouting connection-mark=in3_conn in-interface=Local new-routing-mark=in3
add action=mark-routing chain=prerouting connection-mark=in4_conn in-interface=Local new-routing-mark=in4
/ip firewall nat
# b1 not ready
add action=masquerade chain=srcnat out-interface=PPPOE1
# b2 not ready
add action=masquerade chain=srcnat out-interface=PPPOE2
# b3 not ready
add action=masquerade chain=srcnat out-interface=PPPOE3
# b4 not ready
add action=masquerade chain=srcnat out-interface=PPPOE4
/ip hotspot user
add name=admin
/ip packing
add interface=WAN1 packing=compress-all unpacking=compress-all
add interface=WAN2 packing=compress-all unpacking=compress-all
add interface=WAN3 packing=compress-all unpacking=compress-all
add interface=WAN4 packing=compress-all unpacking=compress-all
/ip route
add check-gateway=ping distance=1 gateway=PPPOE1 routing-mark=in1
add check-gateway=ping distance=1 gateway=PPPOE2 routing-mark=in2
add check-gateway=ping distance=1 gateway=PPPOE3 routing-mark=in3
add check-gateway=ping distance=1 gateway=PPPOE4 routing-mark=in4
add check-gateway=ping distance=1 gateway=PPPOE1
add check-gateway=ping distance=2 gateway=PPPOE2
add check-gateway=ping distance=3 gateway=PPPOE3
add check-gateway=ping distance=4 gateway=PPPOE4
/ip service
set api disabled=yes
/lcd interface pages
set 0 interfaces=WAN1,WAN2,WAN3,WAN4,Local
/system identity
set name=RASHED01769202980
/tool user-manager database
set db-path=user-manager
LikeLike
Comment by RASHED — November 4, 2015 @ 10:32 PM
SalaaM,
Sir,
I have 2 Wan connection with static IP.
Sir Jahanzaib mujhay jo setup kerna he wo ye he k merey pass mikrotik router rb750gl he.
mujhay WAN1 se sirf Lotusnot ka trafic set kerna he.
or WAN2 se others internet traffic ko pass kerna he.
Kindly is setup k liye script bata dain.
or Mikrotik RB750GL me 2 WANs ko configure kis terhan kerna he ye bhi semjha dain.
I am waiting for your response.
LikeLike
Comment by Abbas — November 25, 2015 @ 8:06 AM
you can do through the following method
http://wiki.mikrotik.com/wiki/Load_Balancing_over_Multiple_Gateways
another method is you need to create mangle and route rule for 2 WAN. In mangle rule you will create mark routing and connection then set routes for those and same thing will do for second WAN connection.
Also, you can divide one subnet through following method 192.168.0.0 e.g
192.168.0.0/25 and 192.168.0.128/25
Regards,
LikeLike
Comment by wasimashiq — November 26, 2015 @ 6:16 PM
i think the rules are perfect however it is making me confuse why you are marking packets on input chains? why would someone need to mark a packet which is destined to a firewall. and i think output chain is also overkill as the firewall it self is in forwarding state. Prerouting ruls are OK.
LikeLike
Comment by Yousuf — December 16, 2015 @ 11:57 PM
Sir………..whatsapp videos slow and no downloading on loadbalancer pcc method
if i connected direct vdsl modem via wifi than perfect download the videos from whatsapp
how can i solved this problem…………?
ALLAH aap ko jaza e khair dey
LikeLike
Comment by Salman — January 3, 2016 @ 7:10 PM
Hi,
sorry to buzzyng you…
I’m using the following script, but it still not working:
/ip address
add address=192.168.102.222/24 network=192.168.102.0 broadcast=192.168.102.255 interface=P2_LOCAL
add address=192.168.25.30/24 network=192.168.25.0 broadcast=192.168.25.255 interface=P3_NET_1
add address=192.168.0.2/24 network=192.168.0.0 broadcast=192.168.0.255 interface=P4_NET_2
/ip firewall mangle
add chain=input in-interface=P3_NET_1 action=mark-connection new-connection-mark=conexao_net1
add chain=input in-interface=P4_NET_2 action=mark-connection new-connection-mark=conexao_net2
add chain=output connection-mark=conexao_net1 action=mark-routing new-routing-mark=para_conexao_net1
add chain=output connection-mark=conexao_net2 action=mark-routing new-routing-mark=para_conexao_net2
add chain=prerouting dst-address=192.168.25.0/24 action=accept in-interface=P2_LOCAL
add chain=prerouting dst-address=192.168.0.0/24 action=accept in-interface=P2_LOCAL
add chain=prerouting dst-address-type=!local in-interface=P2_LOCAL per-connection-classifier=both-addresses-and-ports:2/0 action=mark-connection new-connection-mark=conexao_net1 passthrough=yes
add chain=prerouting dst-address-type=!local in-interface=P2_LOCAL per-connection-classifier=both-addresses-and-ports:2/1 action=mark-connection new-connection-mark=conexao_net2 passthrough=yes
add chain=prerouting connection-mark=conexao_net1 in-interface=P2_LOCAL action=mark-routing new-routing-mark=para_conexao_net1
add chain=prerouting connection-mark=conexao_net2 in-interface=P2_LOCAL action=mark-routing new-routing-mark=para_conexao_net2
/ip route
add dst-address=0.0.0.0/0 gateway=192.168.25.1 routing-mark=para_conexao_net1 check-gateway=ping
add dst-address=0.0.0.0/0 gateway=192.168.0.1 routing-mark=para_conexao_net2 check-gateway=ping
add dst-address=0.0.0.0/0 gateway=192.168.25.1 distance=1 check-gateway=ping
add dst-address=0.0.0.0/0 gateway=192.168.0.1 distance=2 check-gateway=ping
/ip firewall nat
add chain=srcnat out-interface=P3_NET_1 action=masquerade
add chain=srcnat out-interface=P4_NET_2 action=masquerade
/ip dns set allow-remote-requests=yes cache-max-ttl=1w cache-size=5000KiB max-udp-packet-size=512 servers=208.67.222.222,208.67.220.220
When i ping a outside ip host, it is ok, but when I try to ping using a named host, it isn’t work.
Could you help me?
Local client machine config:
ip: 192.168.102.3
mask: 255.255.255.0
gw: 192.168.102.222
dns: 192.168.102.222, but I’ve tried a external dns too, like opendns ips ()208.67.222.222 and 208.67.220.220).
Thank you….
LikeLike
Comment by thiago — February 2, 2016 @ 8:23 PM
Asalam o Alaiqum.. IS it compulsory to use all class C IPs with this script. or mixed classes can work? e.g., on LA< we use 192.x.x.x while on WANS
LikeLike
Comment by a1technoman — February 3, 2016 @ 6:08 PM
Asalam o Alaiqum.. IS it compulsory to use all class C IPs with this script. or mixed classes can work? e.g., on LAN we use 192.x.x.x while on WANs its vary.. both 192… and 110.. with its gateways..
LikeLike
Comment by a1technoman — February 3, 2016 @ 6:09 PM
ip series is not compulsory. you can use any scheme of your choice.
LikeLike
Comment by Syed Jahanzaib / Pinochio~:) — February 4, 2016 @ 10:10 AM
Asalam o Alaiqum. how r u bhai?
i have tried the above script. but it is not working on all ready running hotspot server. but this script runs on separate PC base routerOS properly.
i have 2 dedicated links of 20MB each and 2 shared links (PTCL) of 4MB each. while have 2 ports for Local use. 1 use for PPPOE and 2nd for hotspot service.
The problem is, i’m unable to understand how to utilize it in a way that my both ports will use this script. what do i need to add more in this script to work exactly what i need.
Looking forward for reply. Thankyou..
LikeLike
Comment by a1technoman — February 7, 2016 @ 2:17 PM
Dear sir
Thanks for this script but i have 3 questions if you don’t mind
1 – will there be a problem if 1 or 2 or even 3 out of the 4 WANs was disconnected?
2-does this script work with Hotspot??
3-can we direct the balanced internet into “two” ports instead of one???i want to run 2 hotspot servers from the same internet source,so can i just duplicate the lines to go to lets say “LAN2″along the LAN port?
thank you and best regards
LikeLike
Comment by Mohamed — February 9, 2016 @ 9:53 AM
Dear sir
I have 2 isp leaseline with public ip i want to loadbalance each 10+10=20 MB on another static ip can you help me???
LikeLike
Comment by sunil wayal — February 11, 2016 @ 6:45 PM
Dear Shahzab ! Thanks for sharing knowledge with us !
I have 3 WANs , 2 X PTCL 4Mbps and 1 X Qubee 1 Mbps. I want to use Unequal Load Balancing. Can i repeat PCC Rule for 4 Mbps Connection 4 Times and for 1Mbps Connection 1 Times ?
PPC Rule for 4 Mbps WAN1
PPC Rule for 4 Mbps WAN1
PPC Rule for 4 Mbps WAN1
PPC Rule for 4 Mbps WAN1
PPC Rule for 4 Mbps WAN2
PPC Rule for 4 Mbps WAN2
PPC Rule for 4 Mbps WAN2
PPC Rule for 4 Mbps WAN2
PPC Rule for 1 Mbps WAN3
Am i right ? is the load balancing technique that you have discussed here is applicable to my case ?
we have already a mikrotik running with out Loadbalance , only DHCP DNS Static Route and Firewall
Thanks again.
LikeLike
Comment by Ammar — February 13, 2016 @ 2:11 PM
hi! im a beginner is it possible to use pcc using dynamic WAN???and possible to bond bandwidth with different ISP??
LikeLike
Comment by clyde drexler — February 20, 2016 @ 6:15 AM
Yes
LikeLike
Comment by Syed Jahanzaib / Pinochio~:) — February 23, 2016 @ 12:48 PM
Assalam Oo Aykum
Sir maine dekha hai ek hi UTP kay ander Multiple ISP chal rahi hotin hain
LIke Fariya , Connect and Leo bas net provider IP enter karta hai or ISP change hojati hai sir please mujhay yah janna hai kay yah kis tarha hoti hai or kon kon say Switch or Router lagtain hain or kis tarha ek hi UTP Kay ander 3 service chal saktin hain ….
apkay jawab ka intizar hai………
LikeLike
Comment by hammad — April 17, 2016 @ 2:38 AM
hai sir
can not teach me how to script 4 WAN load balancing method PCC along with transperncy web proxy … I ‘m trying to do but to no avail … please sir can help saya..TQ
LikeLike
Comment by osman — May 24, 2016 @ 4:25 AM
Hi, When i crate these Mangles the connection between my remote office and my local office is dropped. Please be inform that i have ptp link connected to mikrotik with a static route, so both office with different IP segment can see each other but after creating these ip mangles the remote office can ping the mikrotik router itself but can’t ping any client behind the router.
LikeLike
Comment by Masoud — May 31, 2016 @ 3:07 PM
Could you explain why use different distance?
add dst-address=0.0.0.0/0 gateway=192.168.1.1 distance=1 check-gateway=ping
add dst-address=0.0.0.0/0 gateway=192.168.2.1 distance=2 check-gateway=ping
add dst-address=0.0.0.0/0 gateway=192.168.3.1 distance=3 check-gateway=ping
add dst-address=0.0.0.0/0 gateway=192.168.4.1 distance=4 check-gateway=ping
LikeLike
Comment by Nick — July 13, 2016 @ 3:49 AM
i have a problem, i used the script and work but if i use the rb how bilance server and an other rb how pppoe server the bilance work only in one ip how i can fix it?
LikeLike
Comment by Giuseppe — August 30, 2016 @ 4:21 PM
aoa sir how to copy script 750gl terminal plz help
LikeLike
Comment by sadaqatew — September 6, 2016 @ 4:51 PM
Simply works great thank you(just need to do an ip pool and a dhcp server for local interface)
LikeLike
Comment by paser — October 20, 2016 @ 4:47 AM
salam bhaii.. mene RB750gl me load balancing+pppoe server banaya hai lekn 1 waqt me 1 hi wan use horhi hai kya issue hai ??
LikeLike
Comment by Rkr Minhaj — October 27, 2016 @ 3:45 AM
probably something missing either in mangle/nat or route section.
LikeLike
Comment by Syed Jahanzaib / Pinochio~:) — October 27, 2016 @ 11:39 AM
HI, ANY TUTORIAL FOR 6 WAN
LikeLike
Comment by Are Dieyz — October 27, 2016 @ 5:03 PM
sir i’m use already a method in which 2 connection through wan1 and wan2 but it’s a method overflow .that no add 4mb+4mb=8mb .sir what i do
LikeLike
Comment by muddsir — November 4, 2016 @ 6:21 PM
AoA.. bro agr 3line 4Mb ke r 2line 8Mb ke houn phr kis tara seeting karni hote code kasay add karna party hain
LikeLike
Comment by adi khan — November 23, 2016 @ 12:09 PM
AOA, I have setup Mikrotik 4 WAN Load Balancing using PCC method scripted by Zaib Bhai. My All WAN are not equal Because they linked with Wireless bridge ( Client mode). 1 Wan is PTCL ADSL for 4 MB connection, 2 WANS are also PTCL 4MB with the Wireless bridge (client Mode) connection,1 Wan is 4MB Witribe Wireless bridge connection ( Client Mode). The problem is 2 PTCL WAN wireless bridge connection are working fine with Mikrotik, But my 3rd Wireless bridge connection (Witribe) is not working with Mikrotik.
Senario: Witribe is connected ——–> My Client Wireless router( TPLINK 5110G)———-> Client router is connected in Mikrotik (750GL) Port 2 which already has been configured.Now the problem is Mikrotik is not communicating with Witribe Modem. When i get the cable out from mikrotik Lan to my laptop. it doesn’t connect with internet and doesn’t browse at all. if i take the cable out from my Mikrotik device and connect directly with my laptop wich is coming from my Client router, it works absolutely fine but not through with Mikrotik. I have tried every thing changed the port with configuration , even switched my client router but issue remained the same.
Witribe IP: 192.168.15.1 ( Open- No Security)
My Client Router(192.168.2.1) with DCHP on/off ( i tried both) connected in Port 2 as configured by Script
Mikrotik: 192.168.0.1
Please help me out.
Also Zaib bhai I already emailed to you my device script, Just have a look if something wrong in scrpit or need to added ( If needed.)
Thanks in advance.
LikeLike
Comment by ayubwaheed — March 1, 2017 @ 1:34 PM
We want to used 40 MB how is it possible.. We have 3 WAN 25MB, 5MB, 10MB pls provide the exact Script
LikeLike
Comment by Hasan Bosunia — May 25, 2017 @ 2:34 PM
PCC works best with same wan links only.
for your scenario, try to use both-address-and-ports in classifier, and put full load, hopefully you will be able to get good amount of bandwidth. but still theoretically things works best with same links.
LikeLike
Comment by Syed Jahanzaib / Pinochio~:) — May 26, 2017 @ 12:16 PM
[…] Mikrotik 4 WAN Load Balancing using PCC method […]
LikeLike
Pingback by Mikrotik 4 WAN Load Balancing using PCC method | IT WORLD — May 31, 2017 @ 7:07 PM
[admin@MikroTik] /ip route> print
Flags: X – disabled, A – active, D – dynamic, C – connect, S – static, r – rip, b – bgp, o – ospf, m – mme,
B – blackhole, U – unreachable, P – prohibit
# DST-ADDRESS PREF-SRC GATEWAY DISTANCE
0 A S 0.0.0.0/0 192.168.1.1 1
1 A S 0.0.0.0/0 192.168.2.1 1
2 A S 0.0.0.0/0 192.168.1.1 1
3 S 0.0.0.0/0 192.168.2.1 2
LikeLike
Comment by ahmed fathy — July 4, 2017 @ 11:43 PM
hello plz helpvme … sir same is ko dack ka ma nay load balanceing bani ha phr work nahi kar rahi … plz helpme
LikeLike
Comment by ali — July 16, 2017 @ 12:32 AM
Can you plz help me? I don’t know if this question was already answered so I post it or repead the request.
Connections on some ports (in my case for RDP-connections) should only be allowed on WAN1.
Scenario: 2 WANs, 1 LAN; Incoming connections work if WAN2 is disabled. I guess that a mangle-roule is missing (or is PCC not possible for WANs that should be reachable for incoming connections?). Routing- + connection-part of my /ip firewall mange – config:
chain=prerouting action=mark-connection new-connection-mark=WAN1_conn passthrough=yes
dst-address-type=!local in-interface=LAN per-connection-classifier=both-addresses-and-ports:2/0 log=no
log-prefix=””
chain=prerouting action=mark-connection new-connection-mark=WAN2_conn passthrough=yes
dst-address-type=!local in-interface=LAN per-connection-classifier=both-addresses-and-ports:2/1 log=no
log-prefix=””
missing connection-mark?
chain=prerouting action=mark-routing new-routing-mark=to_WAN1 passthrough=yes in-interface=WAN1 log=no
log-prefix=””
chain=prerouting action=mark-routing new-routing-mark=to_WAN2 passthrough=yes in-interface=WAN2 log=no
log-prefix=””
chain=prerouting action=mark-routing new-routing-mark=to_RDP passthrough=yes protocol=tcp
src-address-list=WAN1 dst-port=3389,XXX* log=no log-prefix=””
*other DST-ports that should be reachable from outside
Name of my Interfaces: WAN1, WAN2, LAN
LikeLike
Comment by Wilfried — October 2, 2017 @ 1:33 PM
SalaM
1- Sir ager 2 WAN 8MB k hon or 1 WAN 4MB ka or 1 WAN 2MB ka to phir bhi yehi script kaam karegi? Ye Kuch Changer Kerna Hoga?
OR
2- Ye 4 WAN Ki Script Laga K Ager Sirf 2 WAN Filhal Active Karon To Bhi Ye Script Kam Karegi Like Failover? Ya 4 WAN Active Hona Lazmi He..??
Q k me kafi script try ker chuka hn load balancing or failover ki but kam nahi ben raha tha q k merey pass 1st WAN 4MB he or 2nd WAN 8MB he.. ab apki ye script dekhi to samujh aya k dono wans ki bendwidh aleg aleg honey ki wejha se aisa ho raha tha.
PCC WITH UN-EQUAL WAN LINKS
If you have Un-Equal WAN Links, for example WAN,1,2,3 are of 4MB and WAN,4 is of 8 Mb, and you want to force MT to use WAN4 link more then other because of its capacity, Then you have to Add more PCC rules assigning the same two marks to a specific link i.e WAN4 , something like
Code:
add chain=prerouting dst-address-type=!local in-interface=Local per-connection-classifier=both-addresses-and-ports:4/0 action=mark-connection new-connection-mark=WAN1_conn passthrough=yes
add chain=prerouting dst-address-type=!local in-interface=Local per-connection-classifier=both-addresses-and-ports:4/1 action=mark-connection new-connection-mark=WAN2_conn passthrough=yes
add chain=prerouting dst-address-type=!local in-interface=Local per-connection-classifier=both-addresses-and-ports:4/2 action=mark-connection new-connection-mark=WAN3_conn passthrough=yes
add chain=prerouting dst-address-type=!local in-interface=Local per-connection-classifier=both-addresses-and-ports:4/3 action=mark-connection new-connection-mark=WAN4_conn passthrough=yes
add chain=prerouting dst-address-type=!local in-interface=Local per-connection-classifier=both-addresses-and-ports:4/4 action=mark-connection new-connection-mark=WAN4_conn passthrough=yes
Kindly Reply
JAZAK ALLAH
LikeLike
Comment by SYED ABBAS HUSSAIN — November 6, 2017 @ 9:42 AM
Aslamo Alikum, Syed Bhai
When i chnge pcc rule per connection classifier from both adress and ports to src-adress ,
only one wan works at a time if i disable that working wan then other wan start working but both wans are not working on same time. please help if you can
thnaks
LikeLike
Comment by USMAN YOUSAF — December 8, 2017 @ 3:01 PM
AOA,
That is the src-address, when one connection will attach with any link so it will stuck with that link it will not bind other available link. in src-address use only one link stuck with one WAN. instead in both address and ports it goes with all available WANS.
LikeLike
Comment by Ayub Waheed — February 13, 2019 @ 2:51 PM
hello sir i am ali … sir mujy mikrotik ki window chye update 6.20 ya pher koi or update with key and license plz sir
LikeLike
Comment by muhammad ali — March 25, 2018 @ 7:18 PM
[…] normal LB, read my article at https://aacable.wordpress.com/2011/06/04/mikrotik-4-wan-load-balance-pcc-complete-script-by-zaib/ In this example I used MikrotikT RB750 5 ports router. 4 ports were connected with four DSL […]
LikeLike
Pingback by Mikrotik 4 WAN Load Balancing using PCC with PPPoE Server / Complete Script ! | Syed Jahanzaib Personal Blog to Share Knowledge ! — April 24, 2018 @ 11:05 PM
Thank you for sharing and for this great blog !!!! good luck
LikeLike
Comment by Beso — May 3, 2018 @ 9:50 PM
hello sir kasy ha app sir mujy cisco ki vlan banai ha or sath ma is ma he load blasing bi plz help me sie
On Sun, May 6, 2018 at 12:05 AM, Syed Jahanzaib Personal Blog to Share Knowledge ! wrote:
> Beso commented: “Thank you for sharing and for this great blog !!!! good > luck” >
LikeLike
Comment by maher Ali — May 15, 2018 @ 12:10 AM
What is the function of the following rules?
# Accept Connections
/ip firewall mangle
add action=accept chain=prerouting in-interface=WAN1
add action=accept chain=prerouting in-interface=WAN2
add action=accept chain=prerouting in-interface=WAN3
add action=accept chain=prerouting in-interface=WAN4
LikeLike
Comment by David — October 23, 2018 @ 5:38 PM
Above mentioned script is for PCC src-address or both address and port?
LikeLike
Comment by Ayub Waheed — February 13, 2019 @ 2:43 PM
both address and port
LikeLike
Comment by Syed Jahanzaib / Pinochio~:) — February 15, 2019 @ 3:18 PM
How to Mikrotik RB3011 UiAS-RM router setup
LikeLike
Comment by SABKUCHSITE — July 11, 2019 @ 6:46 PM
Hi, i did exactly as your script and the loadbalance works but cant get a combined bandwidth for dual WANs. (300Mbps+300Mbps). Only managed to get 300Mbps on speedtest.net. Thank you
LikeLike
Comment by Siang Chew — September 4, 2019 @ 3:35 PM
@Siang Chew
speedtest should not be used to measure LB. you should download multiple big files form the internet preferably via “Internet download manager” type tool, and then test multiple download. Also you should use both addresses and ports in PCC classifier.
LikeLike
Comment by Syed Jahanzaib / Pinochio~:) — September 4, 2019 @ 4:14 PM
Welcome, Beck Urid, is happy to integrate and distribute
LikeLike
Comment by Ahmed Ismail — May 16, 2020 @ 5:55 AM
Brother VLAN loadbalancing bi hu sakti ha
8 Connection pr loadbalancing karna chahta hun
LikeLike
Comment by MUHAMMAD WAKEEL — May 21, 2020 @ 10:12 PM
i have mikrotik os with 2 physical port
i have connect 2 wan with two ip 192.168.2.1 and 192.168.3.1 to switch and then connected to on port of mikrotik and other port with ip 192.168.1.1 as LOCAL connected to pc
now there is any way to load balancing two wan with pcc
i search internet and so many say can do it with create vlan for first port but can’t find any script or full tutorial
LikeLike
Comment by Soroush Shakhsi — December 7, 2020 @ 4:46 AM
Dear Syed Jahanzaib hope you are fine , i have mikrotik router with 4 DSL everything working fine but some websites not open like FBR website not login just main page open but when i want login its session expire or logout and same other websites not login whats the reason please advise ? how to resolve this issue ?
LikeLike
Comment by khurram — June 10, 2023 @ 1:53 PM
Dear Khurram,
This is because of changing of IP. Kindly make rules for such traffic to a dedicated DSL connection so that IP will not be changed.
LikeLike
Comment by Muhammad Fawad — June 11, 2023 @ 3:43 PM
Thanks fawad for response kindly help for making rule for specific wan connection for some dedicated website.
I want some specific website traffic out from specific wan .
LikeLike
Comment by Khurram — June 16, 2023 @ 9:54 PM
Dear Zaib,
I have use Mikrotik as a load balancer with 4 WAN , everything working fine but some sites not open page stuck or again and again show login page e.g FBR website main page open but when login with correct id and password but page show again login page also same as my cpenal (cpenal show error your ip has been change that means my request shifting to wan 1 to want 2 and so on … and cpenal not login )
Kindly tell me how to resolve this issue ?
LikeLike
Comment by Khurram — June 13, 2023 @ 3:00 PM
gv .chkvgjhmbchmvyujfjhm, /jk/ukbvj, jmvn nmvyuhkfgufjh, .byigkwsnkln yukbk. nkhbh. b, klnilwn;klnm:Ink.. njklnm /j, wj, j,bujkbk.n/j,b
LikeLike
Comment by asher — June 14, 2023 @ 10:51 AM